A Zero Trust security solution replaces perimeter-centric security architecture. It ensures that security and access decisions are dynamically enforced based on identity, device, and user context. A Zero Trust security framework also dictates that only authenticated and authorized users and devices can access applications and data. At the same time, it protects those applications and users from advanced threats on the internet.
Implementing a Zero Trust strategy
Implementing Zero Trust strategies should be a core component of your security posture. Not sure where to start? Let’s start with the basics:
What is Zero Trust security?
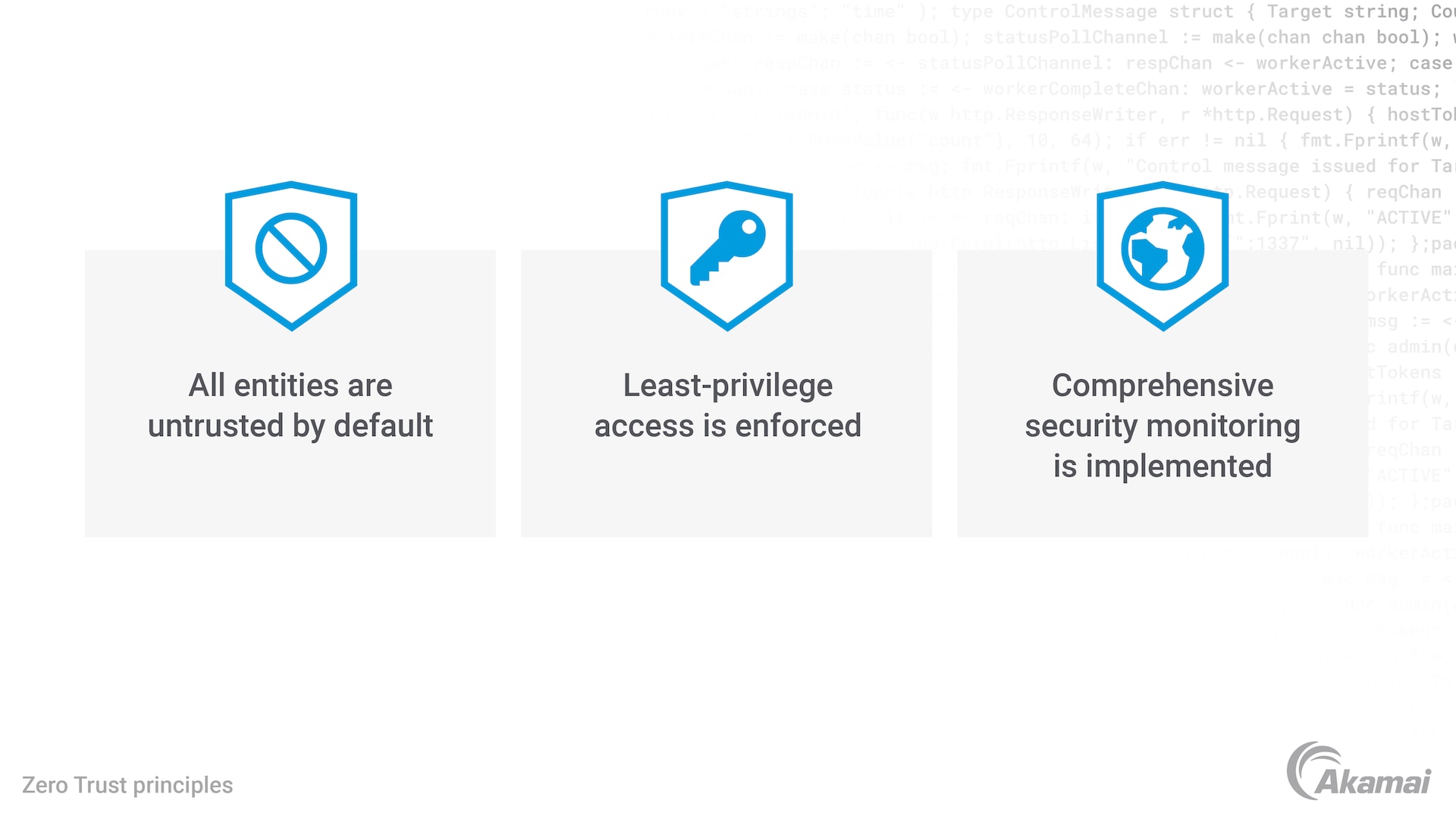
In 2010, Forrester Research analyst John Kindervag proposed a solution he termed “Zero Trust.” It was a shift from the strategy of “trust but verify” to “never trust, always verify.”
The Zero Trust model is a strategic approach to cybersecurity that secures an organization by removing implicit trust across users, devices, networks, data, and applications. Instead of assuming everything behind the corporate firewall is safe, the Zero Trust approach assumes a breach at any moment and applies least-privilege access to every request, regardless of where it originates.
Why Zero Trust matters now
Zero Trust architecture has become top of mind for organizations that need to more effectively adapt to the ever-changing modern environment. These organizations are looking for a new security model that embraces the hybrid workforce and protects users, devices, and apps wherever they are located.
What are the benefits of a Zero Trust approach?
Distributed workforce. Allow users to work more securely from anywhere, anytime, on any device
Cloud migration. Provide secure access control across cloud and hybrid cloud environments
Risk mitigation. Stop cyber threats and minimize lateral movement of ransomware and other types of malware
Compliance support. Ensure compliance with microperimeters around sensitive data
Consolidation is essential
Integrated end-to-end approach
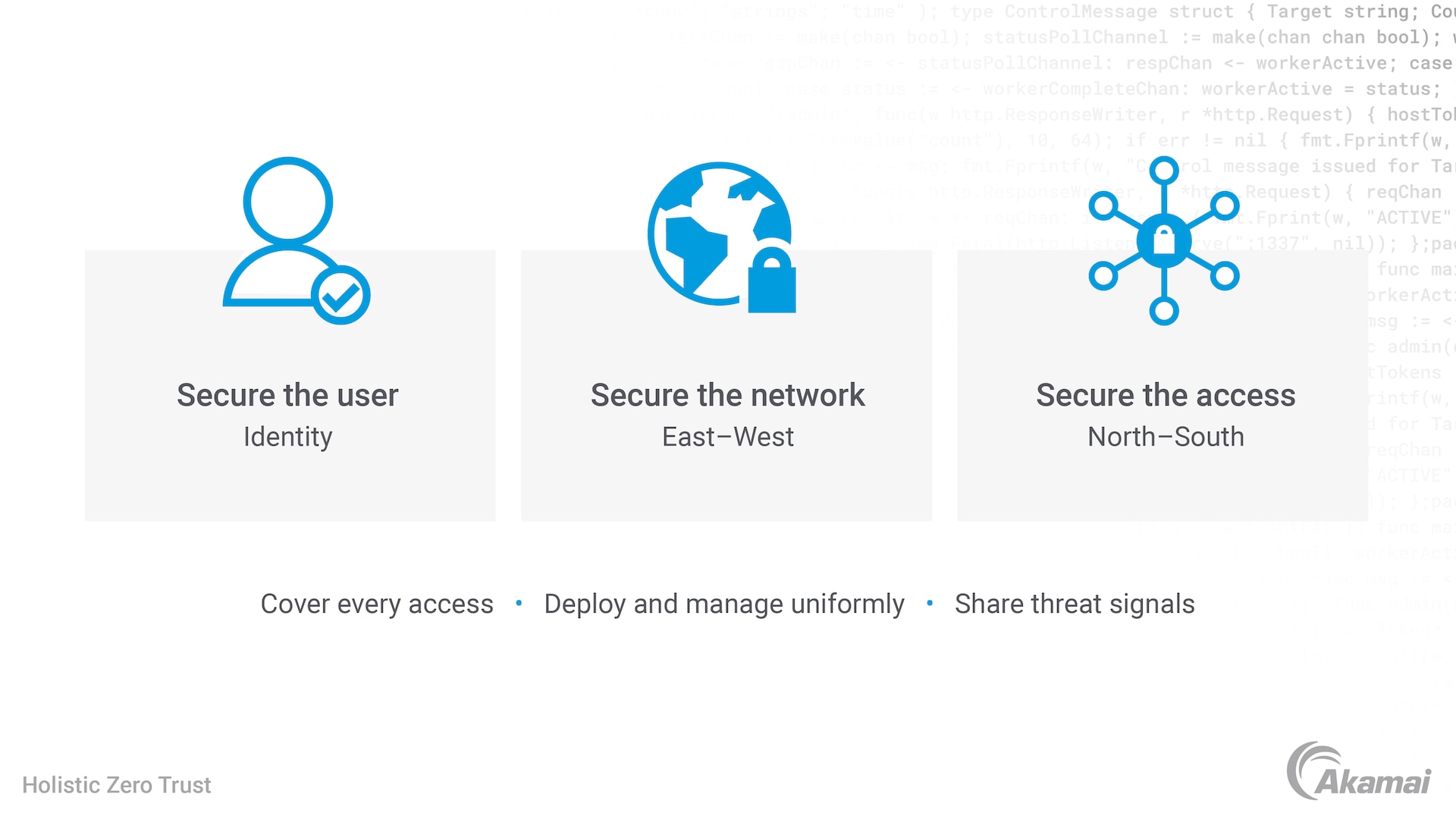
A holistic approach to a Zero Trust security strategy should extend to all the organization’s entities, including identities, network, and apps. Zero Trust principles serve as an end-to-end strategy, which is why they require integration across all elements. Going with multiple, loosely integrated point solutions does not align with this strategic approach.
Akamai has assembled a robust portfolio to deliver all the Zero Trust solutions that are critical for the modern organization. Instead of installing, running, and fixing multiple security products, organizations can rely on a single vendor to deliver all the technologies required and enjoy reduced costs and improved operational efficiencies.
Read the blog post Zero Trust and the Fallacy of Secure Networks.
Signal sharing between solutions
Akamai has automation built in and across its Zero Trust portfolio, greatly reducing complexity and customization. This way, the portfolio products can share threat knowledge across all its products, making each product more secure. If one product identifies a threat, another product can be alerted to mitigate it.
The Akamai advantage
Akamai offers a few advantages that set it apart from other Zero Trust providers. We offer the broadest coverage: legacy and modern; Windows and Linux; on-premises and virtualized, containers, and more. Because of our unmatched visibility capabilities, users are able to know what each workload is doing with full context. Our elite in-house threat detection services extend any security team’s capabilities, allowing your organization to stay ahead of threats and cyberattacks.
A holistic end-to-end portfolio: user, network, and access
Secure the workload
Akamai Guardicore Segmentation: Zero Trust for applications
Akamai Guardicore Segmentation provides the industry-leading microsegmentation solution, designed to limit the spread of ransomware and other malware. The product provides visibility and understanding into the workloads, processes, and applications, as well as enforcement of secure access management policies.
Read the blog post Stopping Ransomware and Lateral Movement with Segmentation
Secure the user
Secure Internet Access: Zero Trust internet access
Secure Internet Access is a cloud-based secure web gateway solution. It inspects every web request that users make and applies real-time threat intelligence and advanced malware analysis techniques to ensure that only safe content is delivered. Malicious requests and content are proactively blocked.
Multi-factor authentication: strong Zero Trust identity
Akamai MFA protects employee accounts from phishing and other machine-in-the-middle attacks. This ensures that only strongly identity-based authenticated employees can access the accounts they own, unauthorized access is denied, and employee account takeover is prevented.
Secure the network and network access
Enterprise Application Access: Zero Trust Network Access (ZTNA)
Akamai’s Zero Trust Network Access technology was designed to replace the traditional VPN technology for strong user identity. Instead of risking the entire network, Enterprise Application Access allows user permissions based on the specific app the user needs to access to perform a function. Enterprise Application Access control provides visibility into user identity and strong enforcement of identification and authentication.
Additionally, track and monitor
Hunt: security services
By adopting an “always assume a state of breach” approach, Akamai’s elite team of threat hunters continuously hunts for vulnerabilities, anomalous attack behavior, and advanced threats, which often escape standard network security solutions. Our threat hunters immediately notify you of any critical incident detected in your network and then work closely with your team to remediate the situation.
Frequently Asked Questions (FAQ)
The notion of a network perimeter — where everyone outside the enterprise’s zone of control is malicious and everyone inside is honest and well-intentioned — can’t be relied on in today’s business landscape. Wide adoption of SaaS applications, migration to cloud-based architectures, a growing amount of remote work, and an influx of BYOD devices have rendered perimeter-based security irrelevant.
Furthermore, a perimeter-centric defense requires appliance and security policy management and frequent software upgrades, causing operational complexity and taxing already overwhelmed IT teams. As the attack surface expands, and strapped IT resources struggle to govern ever-more-convoluted network security architecture, cybercriminals are increasingly proficient, sophisticated, and incentivized to evade security measures. A strategic security ecosystem and framework that addresses these distinct challenges is needed.
Digital systems grant access to anyone who enters the correct password, without verifying the identity of the person. Weak credentials and password reuse significantly increase an enterprise’s attack surface and risk. In today’s threat landscape, relying on single-factor authentication, like username and password, is no longer enough. Multi-factor authentication (MFA) provides an extra level of validation and security; it ensures that only validated users gain access to business-critical applications.
Once the user is authenticated and authorized through MFA, single sign-on (SSO) enables users to log in to all applications with one set of credentials. This improves productivity and the user experience; there’s no need to reconfirm identity for each application and no syncing issues across applications. Making continuous access decisions on a multitude of signals — including MFA and SSO across laaS, on-premises, and SaaS applications — affords the business greater protection while also providing convenience for end users.
Despite wide corporate adoption of layered security, malicious actors continue to gain remote access to enterprises by exploiting security weaknesses. Even with firewalls, secure web gateways, sandboxes, intrusion prevention systems, endpoint security, and anti-virus mechanisms deployed, businesses are exposed and falling victim to phishing, zero-day malware, and DNS-based data exfiltration. So what security risks are enterprises missing?
DNS is an often-overlooked vector. And cybercriminals have developed malware that is specifically tailored to exploit this security gap, evading existing security layers to infiltrate the network and exfiltrate data. Adding a layer of security that leverages the DNS protocol is critical; by utilizing this initial query stage as a security control point, a DNS security solution can detect and stop cyberattacks early in the kill chain, proactively protecting the enterprise.
Why customers choose Akamai
Akamai is the cybersecurity and cloud computing company that powers and protects business online. Our market-leading security solutions, superior threat intelligence, and global operations team provide defense in depth to safeguard enterprise data and applications everywhere. Akamai’s full-stack cloud computing solutions deliver performance and affordability on the world’s most distributed platform. Global enterprises trust Akamai to provide the industry-leading reliability, scale, and expertise they need to grow their business with confidence.