Akamai is the cybersecurity and cloud computing company that powers and protects business online. Our market-leading security solutions, superior threat intelligence, and global operations team provide defense in depth to safeguard enterprise data and applications everywhere. Akamai’s full-stack cloud computing solutions deliver performance and affordability on the world’s most distributed platform. Global enterprises trust Akamai to provide the industry-leading reliability, scale, and expertise they need to grow their business with confidence.
What is Zero Trust?
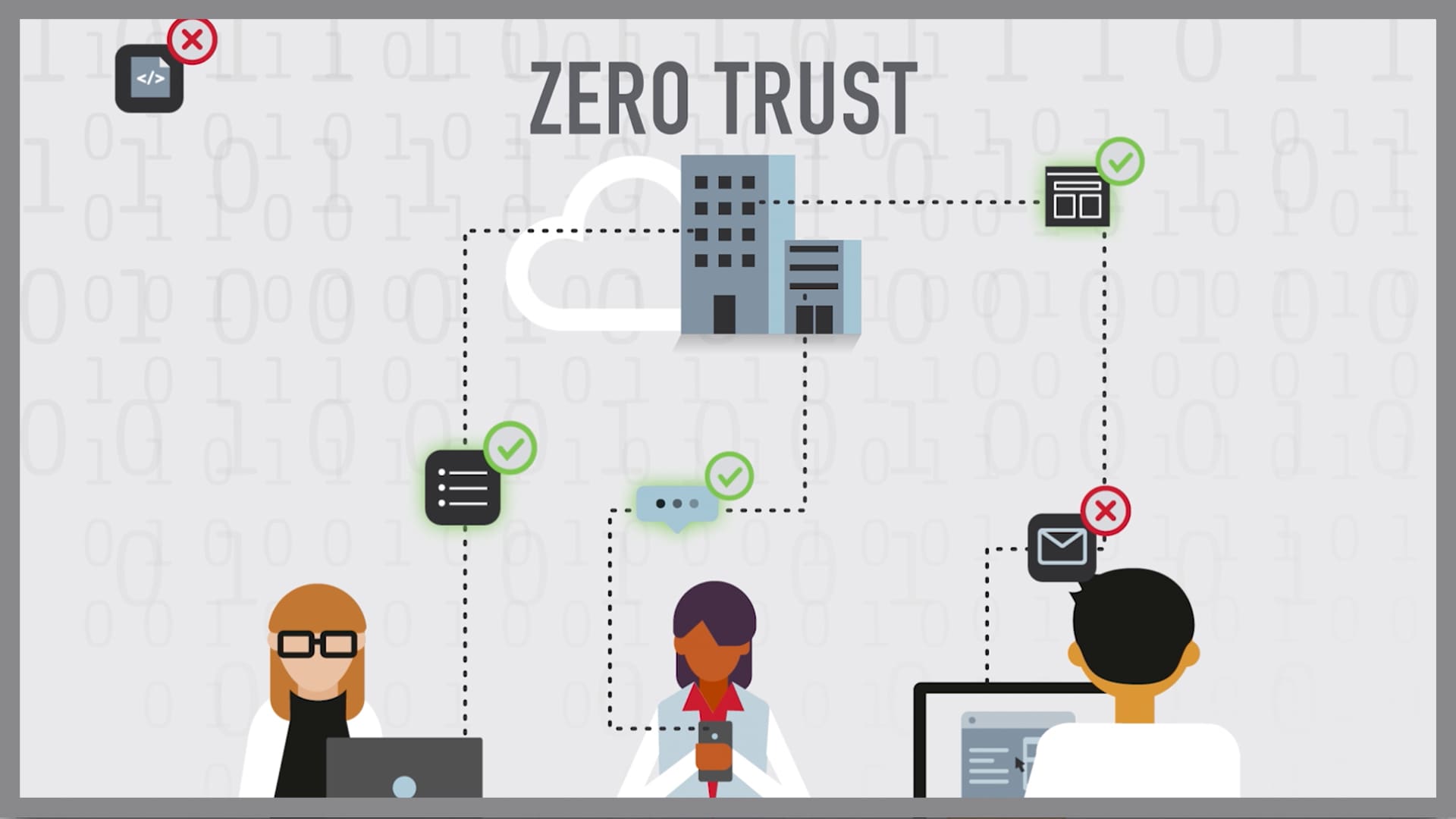
Zero Trust is a network security strategy based on the philosophy that no person or device inside or outside of an organization’s network should be granted access to connect to IT systems or workloads unless it is explicitly deemed necessary. In short, it means zero implicit trust.
What is the Zero Trust model?
In 2010, Forrester Research analyst John Kindervag proposed a solution he termed “Zero Trust.”
It was a shift from the strategy of “trust but verify” to “never trust, always verify.” In the Zero Trust model, no user or device is trusted to access a resource until their identity and authorization are verified. This process applies to those normally inside a private network, like an employee on a company computer working remotely from home or on their mobile device while at a conference across the world. It also applies to every person or endpoint outside of that network. It makes no difference if you have accessed the network before or how many times — your identity is not trusted until verified again. The idea is that you should assume every machine, user, and server to be untrusted until proven otherwise.
Historically, a castle-and-moat approach to cybersecurity seemed workable — the idea of a network perimeter where everyone outside the network — or moat — was “bad” and everyone inside was “good” once prevailed. Just as castles and moats are a thing of the past, so should be the castle-and-moat approach to security. Just think about the current state of remote work. Today’s workforce and workplace have changed — when, how, and where people do their work have moved beyond the four walls of an office. With the rise of the cloud, the network perimeter no longer exists in the way it used to. Users and applications are just as likely to be outside of the moat as they are inside. That introduces weaknesses in the perimeter that malicious actors can exploit. Once inside the moat, lateral movement is typically unchecked, leading to adversaries accessing resources and high-value assets, like customer data (or the crown jewels!) — or launching a ransomware attack.
How Zero Trust works
Imagine the Zero Trust model like an extremely vigilant security guard — methodically and repeatedly checking your credentials before allowing you access to the office building where you work, even if they recognize you — then duplicating that process to verify your identity continuously.
The Zero Trust model relies on strong authentication and authorization for every device and person before any access or data transfer takes place on a private network, no matter if they are inside or outside that network perimeter. The process also combines analytics, filtering, and logging to verify behavior and to continually watch for signals of compromise. If a user or device shows signs of acting differently than before, it is taken note of and monitored as a possible threat. For example, Marcus at Acme Co. typically logs in from Columbus, Ohio, in the United States, but today, he’s attempting to access Acme’s intranet from Berlin, Germany. Even though Marcus’ username and password were entered correctly, a Zero Trust approach would recognize the anomaly in Marcus’ behavior and take action, such as serving Marcus another authentication challenge to verify his user identity.
This basic shift in approach defeats many common security threats. Attackers can no longer spend time taking advantage of weaknesses in the perimeter, and then exploiting sensitive data and applications because they made it inside the moat. Now there is no moat. There are just applications and users, each of which must mutually authenticate, and verify authorization before access can occur. Mutual authentication takes place when two parties authenticate each other at the same time, such as a user with a login and password, and an application they are connecting with through a digital certificate.
What are the components of Zero Trust?
The Zero Trust security model of today has expanded. There are many implementations of its principles, including Zero Trust architecture, Zero Trust Network Access (ZTNA), Zero Trust secure web gateway (SWG), and microsegmentation. Zero Trust security is also sometimes referred to as “perimeterless security.”
Don’t think of Zero Trust as one discrete technology. Rather, a Zero Trust architecture uses a variety of security controls and principles to address common security challenges through preventive techniques. These components are designed to provide advanced threat protection as the boundaries between work and home disappear, and an increasingly distributed remote workforce becomes the norm.
Key capabilities for implementing Zero Trust
- Visibility of on-prem, cloud environments and IoT devices
- Control of network flows between all assets
- Verification of identity and ability to grant access to the cloud
- Network segmentation as well as application-layer segmentation
- Authentication and authorization, including multi-factor authentication (MFA)
- Granular access policies (application access vs. access to the entire network)
- Least-privilege user access to all applications (IaaS, SaaS, and on-premises)
- Minimization of VPN and firewall usage
- Service insertion
- Security at the edge
- Improved application performance
- Improved security posture against advanced threats
- Automation and integration capabilities
Key benefits of Zero Trust architecture
A Zero Trust architecture works seamlessly for users, reduces the attack surface, protects against cyberattacks, and simplifies infrastructure requirements. Different components of Zero Trust architecture can:
Help ensure network trust and thwart malicious attacks
IT teams need to ensure that users and devices can safely connect to the internet, regardless of where the access request is from, without the complexity associated with legacy approaches. They also need to proactively identify, block, and mitigate targeted threats such as malware, ransomware, phishing, DNS data exfiltration, and advanced zero-day vulnerabilities for users. Zero Trust security can improve security postures while reducing the risk of malware.
Provide secure application access for employees and partners
Traditional access technologies, like VPN, rely on antiquated access management principles, and are particularly vulnerable through compromised user credentials that have led to breaches. IT needs to rethink its access model and technologies to ensure the business is secure, while still enabling fast and simple access for all users, including third-party users. Zero Trust security can reduce risk and complexity, while delivering a consistent user experience through granular security policies.
Reduce complexity and save on IT resources
Enterprise access and security is complex and constantly changing. Changes and deployments with traditional enterprise technologies often take days (and often across many hardware and software components) using valuable resources. A Zero Trust security model can reduce architectural complexity.
Other compelling reasons to adopt a Zero Trust strategy
- Users, devices, applications, and data are moving outside of the enterprise perimeter and zone of control, away from traditional data centers
- New business requirements driven by digital transformation increase risk exposure
- “Trust but verify” is no longer an option, as targeted advanced threats are moving inside the corporate perimeter
- Traditional perimeters are complex, increase risk, and are no longer compatible with today’s business models
- To be competitive, security teams need a Zero Trust network architecture able to protect enterprise data, wherever users and devices are, while ensuring that applications work quickly and seamlessly
What are the principles of Zero Trust ?
The Zero Trust model is based on three basic principles:
- All entities are untrusted by default
- Least-privilege access is enforced
- Constant security monitoring is implemented
Why is a Zero Trust security model needed?
The modern workforce is becoming increasingly mobile, accessing applications and cloud services from multiple devices outside of the business perimeter. In the past, many enterprises adopted a “verify, then trust” model — which meant if someone had the correct user credentials, they were admitted to whichever site, app, or device they were requesting. This resulted in an increased risk of exposure, dissolving what was once the trusted enterprise zone of control and leaving many organizations exposed to data breaches, malware, and ransomware attacks. Protection is now needed within specific digital infrastructures where applications and data, and users and devices, are located.
Implementing a Zero Trust architecture with Akamai
Akamai’s cloud security services can be combined to build a complete Zero Trust solution that best suits your specific business needs. By enabling safe application access in a cloud-native world, internal corporate networks can become a thing of the past.
Using our advanced distributed ZTNA solution, industry leading microsegmentation, phish-proof MFA, and a proactive secure web gateway, along with the power of the over 20-year-strong Akamai Connected Cloud, you can easily move to a perimeterless world, phasing in applications, protecting your business, and enabling growth.