Passwords — Extinction Event Looming?
Passwords are the bane of users and security teams’ lives. Despite years of security teams educating users about not using 123456 as a password, not recycling passwords across multiple personal and professional accounts, and implementing even more rigorous password rules and investments in password manager tools, these combinations of letters, numbers, and special characters remain a rich target for attackers. But now, we might be on the cusp of the extinction of passwords as we know them, and moving to passwordless authentication.
Extinction events are commonly associated with events that cause a sudden decrease in biodiversity on the planet. Many have been associated with volcanoes and asteroids that have affected the heat of the planet or the amount of CO2 in the air. Whilst that may be poignant given the recent news on climate change, I also think that it is relevant when we look at less dramatic events that still affect a huge amount of people.
Many of us are now familiar with the concepts around multi-factor authentication, which typically involves at least two of three factors:
something you know (password)
something you are (fingerprint or other biometric factor)
something you have (cellphone or another physical device)
The first one has always been the default option — the first method any application developer or IT manager uses to allow access. Passwords are something we feel familiar with, although not because we like them. They are seen as a necessary evil. How many people actually like using, remembering, and creating new passwords every day? Consider the hundreds of services we use and networks we access, or how many exist that we are in control of and need to manage.
I recently checked the stored passwords in my password manager app and counted 258 different logins for apps relating to work, travel, and social. These covered things like airline loyalty points, my cell phone provider, my salary details, and the ability to order a drink in a pub during COVID-19 lockdown.
But I do use a password manager — so they are all complex and all unique — so hopefully relatively secure. Otherwise, there would be a danger that the password I use for the app to order drinks at the pub could be the same as my payroll provider, stockbroker, or corporate email. If that was the case, then there would be a real risk that if one of those credentials is spilt (hacked) onto the internet, all the other accounts would be at risk of account takeover. However, password managers — as effective as they can be — are never going to be accepted by the general population, as many users will not “see” the benefit. They can also be quite cumbersome and complicated for less tech-savvy users.
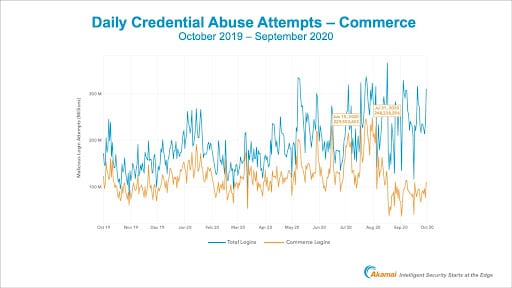
Credential spills are becoming more frequent, especially since lockdown was imposed on most areas of the globe, and more people have been working from home and using the internet more frequently for a whole host of services such as grocery deliveries, streaming video, and anything else that can be delivered to your door. So much so that on the popular site haveibeenpwned.com, where spilt credentials are posted so that legitimate users can check to see if their credentials have been exposed, now lists nearly 11.5 billion accounts. When you realise the number of internet users is only just over 4.5 billion, that means about 2½ credentials for every user on the planet have been spilt and are now in the hands of the bad guys.
The bad guys know we are bad at passwords, so they can spray these spilt passwords at websites across the globe in the hope that they will find some that stick. When you think about the fact that the success rate can be as high as 1%, it is clear to see that this is an effective way to compromise accounts across the world.
This is why the other two elements are increasingly being used to verify users that log in with just a password. You may get a text message or an email to check who you say you are. But again, this is a cumbersome extra step that many online services don’t want to put their customers through — copying and pasting a code from an SMS into a website doesn’t scream “frictionless,” which is the aspiration of the site owner to ensure a positive user experience.
So if we want a good UX for our users, why do we keep requiring passwords? Aside from them being ubiquitous, we know the downfalls and the risks. We could use one of the other two factors instead — when you hit a website that you have an account with, it will send a notification to your cell phone that you just need to acknowledge. No need to remember a password, and it falls into the “something you have” category. If we require the acknowledgement to be a fingerprint, then we have two-factor authentication — “something you have” and “something you are.” This would work across web apps and mobile apps with no differentiation.
Inclusivity is often seen as a major hurdle once we move to alternatives to passwords, but passwords themselves, and all the reset/captcha pages that are used around them, have always been seen as exclusive to a degree. With approximately 20% of the English-speaking world impacted by dyslexia, it is clear that the current password position is far from ideal.
So the alternatives can actually be more inclusive than what is already there. Facial recognition, fingerprint scans, or voice recognition are all alternatives that can be used in place of a password. None need to be remembered and all are unique. The current pandemic has accelerated many technologies over the past 18 months that make our lives easier and more secure, so why do we still sit in the mire created by passwords?
It might not be a dinosaur extinction event for passwords, but they could soon be seen to be going the same way as the dodo.



