Over 25% of Malicious JavaScript Is Being Obfuscated
Last year, Akamai released research on obfuscation techniques being used by cybercriminals to create malicious JavaScript. The code is unreadable, un-debuggable, and as a result, much more challenging to analyze and detect.
According to recent research that analyzes over 10,000 malicious JavaScript samples — representing threats like malware droppers, phishing pages, scammers, and cryptominers’ malware — at least 25% of the examined samples use JavaScript obfuscation techniques to evade detection. This significant percentage of files indicates continued adoption of obfuscation techniques by cybercriminals that want to stay under the detection radar.
On top of that, JavaScript obfuscation isn’t solely used for malicious purposes. Research that examines the 20,000 top-ranked websites according to Alexa.com reveals that at least 0.5% of those websites contain embedded, obfuscated JavaScript code. The most common driver of obfuscation on these non-malicious websites is the concealment of code functionality from public access so it’s harder to understand.
It’s all about packers
Software packing is a method of compressing or encrypting code that makes it unreadable or non-debuggable. As a result, the code changes in an attempt to avoid signature- or hash-based detection. Research that will be presented at the SecTor 2021 conference introduces a technique that profiles the unique functionality of packers to detect JavaScript prior to it being obfuscated, regardless of the original code. That way, any JavaScript code that represents a threat — like phishing, malware droppers, or scammers — will be detected based on the techniques the packer introduces.
Below is a snapshot of four pieces of JavaScript code that originated from four unrelated malicious files. Two of them are phishing, one is a malware dropper, and one is a Magecart scammer. Those four pieces of code use different variables and function names, yet they have the same structure and execute the same obfuscation functionality — iteratively going over a given payload in the form of an array and reshuffling the order of that array. These four examples are the output of the same unique packer functionality being used to obfuscate any given JavaScript code.
 Image 1: Four examples of the same obfuscation functionality
Image 1: Four examples of the same obfuscation functionality
By profiling packers and their functionality, we evaluated 30,000 benign and malicious JavaScript files and were able to see that at least 25% of the malicious files used one of five profiled packer functionalities. The high percentage of malicious files being obfuscated shows that cybercriminals continue to adopt techniques that enable them to evade detection.
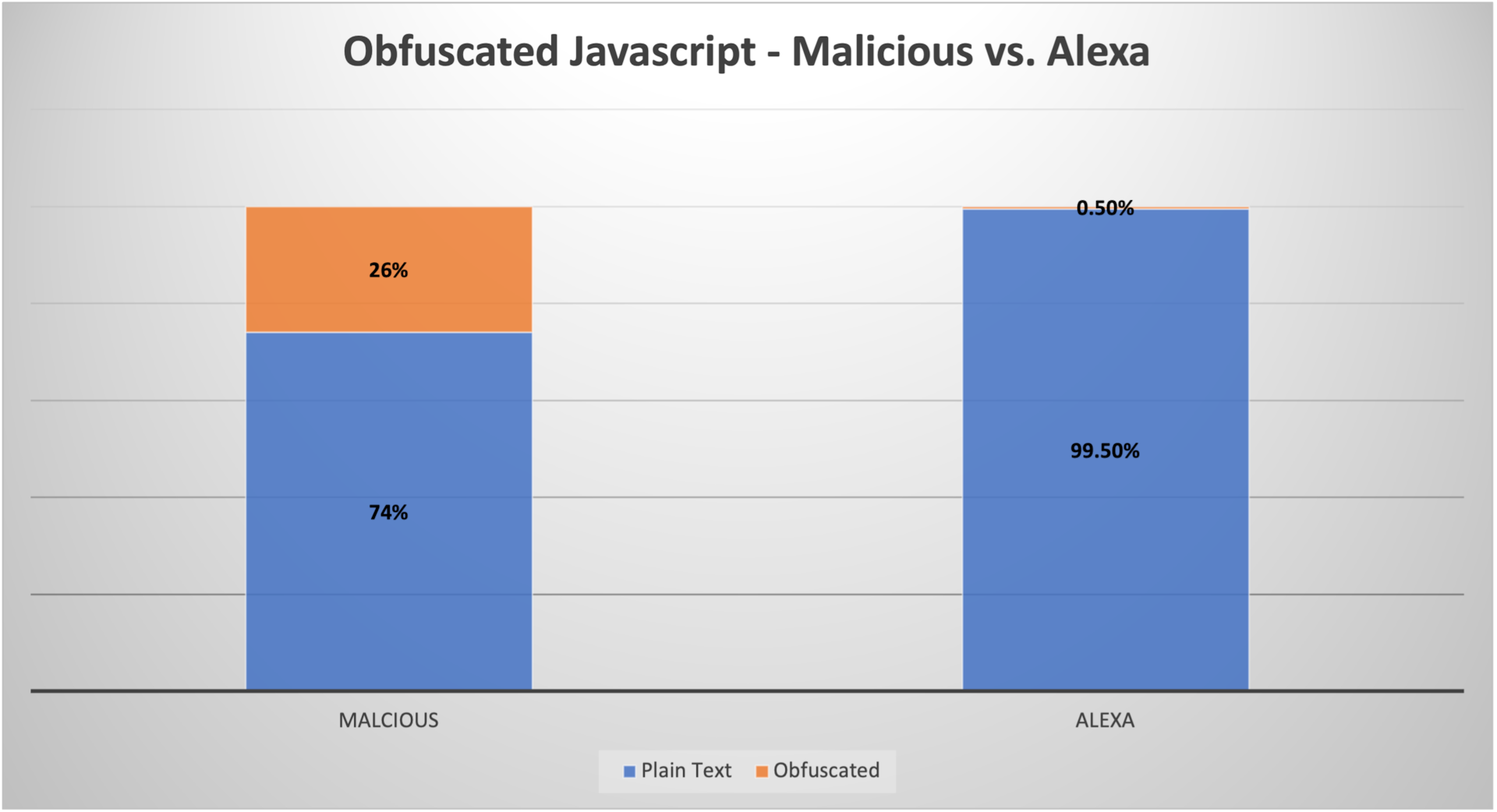 Image 2: Obfuscated JavaScript: Malicious vs. 20,000 top-ranked websites according to Alexa.com
Image 2: Obfuscated JavaScript: Malicious vs. 20,000 top-ranked websites according to Alexa.com
A more challenging result was found in the benign files from the 20,000 top-ranked websites according to Alexa.com, where we were able to see that 0.5% of files also used packer obfuscation techniques. Further inspection reveals that the obfuscation being used is the result of various legitimate scenarios, including:
Websites that are trying to conceal some of their client-side code functionality
Code that was obfuscated by a third-party provider
The obfuscation of sensitive information like email addresses
This evidence sheds more light on the challenges of detecting malicious JavaScript, as obfuscation by itself is not enough to indicate the presence of malicious code. The approach for detecting malicious obfuscation requires more advanced machine learning techniques that enable differentiation between malicious and benign obfuscated JavaScript.
Summary
In the threat landscape, the ongoing tension between cybercriminals and defensive forces means that every millisecond counts, and the availability of limited resources plays a critical role.
As the scale of malware and phishing threats continues to expand, obfuscation might result in the need for more time and resources, which might lead to missed detection — making attacks more effective and valuable to cybercriminals.
Research also shows that obfuscation has legitimate use cases and clearly can’t be used as a single indication for flagging malicious content. A better approach for detection should be one that uses additional indicators and considers obfuscated code as suspicious till proven otherwise. Indicators can be in the form of website features, like domain age and website popularity rank, or in the form of JavaScript code features, like code size and complexity.
While not considered a new technique, the use of JavaScript obfuscation indicates the continuous adoption of evasion techniques by cybercriminals. Consequently, we need to keep an eye on the threat landscape, monitoring trends and evaluating the evolution of techniques and methods being used in the wild.



