Getting Ready for Some Holiday Shopping? So Are the Bots

Black Friday and Cyber Monday are just around the corner, and if India’s Diwali festival and China’s Singles Day are any indication, U.S. retailers could be bombarded with bad bots, aimed at competing with real shoppers this holiday season. And the stakes are high. Global supply chain issues, skyrocketing shipping costs, inflation, and domestic labor shortages have rapidly compounded problems within a sector already slammed by the COVID-19 pandemic. Consumers have been repeatedly warned that hot items on holiday shopping lists will be hard to secure and may not arrive in time for Christmas. According to a recent report, 42% of holiday shoppers should expect to find more out-of-stock items this year than in the past.
Threat actors are well aware of the increased pressure facing retailers (and consumers) globally and stand ready to take advantage of the industry’s “make or break it” time of year. While cybercriminals have an arsenal of attack vectors, tools, and exploits to leverage, one in particular, malicious bots, poses a significant threat to online retailers — and their bottom line.
The battle of the bots
As a quick refresher, bots can be broken down into two buckets — good bots and bad bots. Good bots, like Googlebot and Bingbot, crawl and index retailer websites to help improve search results. These types of bots are not built with bad intentions, and they respect rules as defined by the webmaster’s robots.txt file. However, malicious bots are purpose-built for a variety of nefarious activities like credential abuse for account takeover (ATO) attacks, grabbing limited inventory ahead of real customers, Layer 7 application DDoS attacks, price scraping, gift card fraud, and more. Juniper Research estimates that ecommerce fraud — oftentimes associated with bad bots — will increase 18% in 2021 to reach $20 billion in losses for retailers globally. Another study by RiskIQ found the ecommerce industry lost ~$38,000 per minute to online payment fraud.
With so much on the line, it comes as no surprise that Akamai observed bot operators out in full force, causing significant upticks in malicious bot activity leading up to and during the most recent online shopping mega-holidays like Diwali and Singles Day.
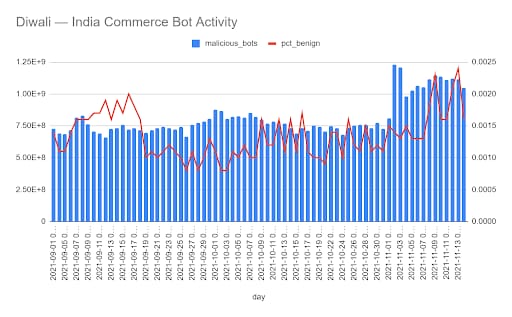
For India’s Diwali festival, consumers helped shatter previous shopping records, bringing in Rs 1.25 trillion (~$16.8 billion) in revenue.
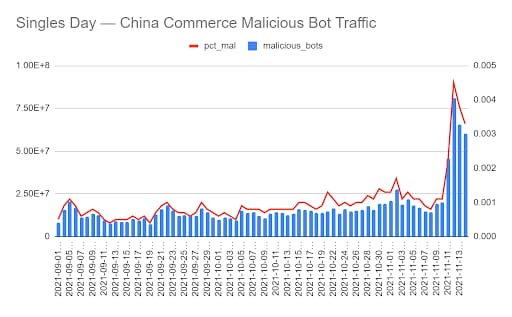
Taking place on November 11, Singles Day in China resulted in a record-setting $138 billion in transactions in a single day for Alibaba and JD.com.
So what does this mean for Black Friday and Cyber Monday?
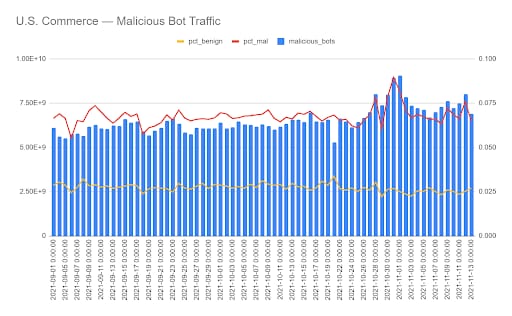
Based on the data above, it’s not a leap of faith to assume that we’ll also see a massive surge in malicious bot activity aimed at disrupting U.S. online retailers. Looking at our data leading up to Black Friday and Cyber Monday, we’ve already observed an uptick since early September in malicious bot attacks, with a significant jump toward the end of October (see chart below). The timing of this increase aligns with the early push by many retailers for American consumers to start their holiday shopping early. And when consumers show up, bot operators do too, with stolen credentials in tow.
What businesses can do to help ensure bots don’t ruin holiday cheer
Be alert to evidence of an attacker moving through the ATO kill chain. For example, threat actors often start preparing for full-scale attacks with some testing, so you might see a small spike in failed logins over the next few days before Black Friday and Cyber Monday. Keep in mind that discovering and stopping bot attackers early in the weaponization and delivery phases of the ATO kill chain means organizations can better defend against fraud and abuse.
Tune your bot solution if you see more bots coming through. Note: Not all bot management solutions need manual tuning; check if yours does.
What consumers can do to protect their accounts from being stolen and used by bot operators
Check your accounts for any changes you didn’t make — address, credit card, phone number, email, etc. These are strong indicators that the attacker will use the account later, for example changing the address now so the goods will get shipped to their drop location later.
Change all of your retail passwords and add multi factor authentication (MFA) if you haven’t already. Good password hygiene is always recommended, of course, but now is the time to change all of your spending account passwords to something new, so even if your credentials are somewhere out in the dark web, they’ll be invalid if the attackers try to use them for their own holiday shopping sprees. And adding MFA will give another layer of protection against motivated attackers.
Be wary of any new social friend requests or “10 questions” games. Social engineering and phishing are ways that attackers get new passwords or answers to security questions. So be extra careful now with new friend requests from people you don’t know (or who maybe aren’t even people, but bots)! And even though they’re fun, don’t post answers to those list games where you are asked for things like the city you were born in, favorite color, first pet, etc. Attackers can use those answers to try and guess passwords.
Additional resources:
Break the Account Takeover Kill Chain
The Underground Economy: Recon, Weaponization & Delivery for Account Takeovers