Coming Together to Tackle Phishing — For the Greater Good
Every day, Akamai’s Threat Research team tracks and mitigates phishing attack campaigns to help keep our customers — and their reputations — protected. Recently, they tracked an orchestrated attack campaign comprising more than 9,000 domains and subdomains, mainly targeting victims located in China. The phishing scam was abusing more than 15 high-profile and trusted brands spanning ecommerce, travel, and food & beverage industries. By using well-known brand names, the threat actors attempted to engage victims to participate in a quiz that, once completed, would result in winning an attractive prize. Akamai refers to this malicious modus operandi as a “question quiz” phishing attack campaign.
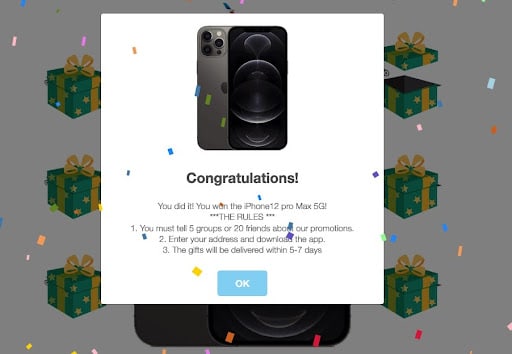
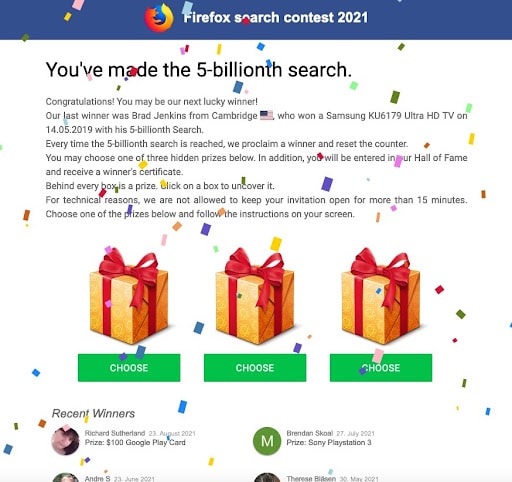 An example of a “question quiz” website
An example of a “question quiz” website
While phishing campaigns are an extremely common and pervasive type of threat vector, the sheer scale and continuous change in the usage of the domains and subdomains to evade detection were unique. Further analysis revealed the distinct nature of this attack campaign by which threat actors took advantage of the content delivery network (CDN) features, scale, and reputation to make the scam much more resilient to detection and mitigation (more on this below). Because of the short life span of domains and subdomains used in the attacks, by the time a domain would have been classified as malicious, a new domain was introduced into the wild. This new domain still delivered the same phishing website content shielded behind the CDN.
Examining the latest phishing tricks ’n’ techniques
Delving further into the “question quiz” phishing toolkit being used, our researchers observed features that enabled targeting specific victims, anti-detection techniques, and the ability to easily distribute attacks throughout social networks — reaching more potential victims. These features were all intended to make the phishing attack as effective as possible.
More specifically, we were able to see that this campaign was targeting mobile device victims, using WhatsApp and Facebook as main distribution channels. The phishing website also contained fake social network users as part of the scam to make the phishing site appear more legitimate and to drive increased trust and engagement from potential victims.
While we don’t have clear evidence concerning the origin resources that were used to deliver this attack campaign, Akamai highly suspects that those origins were limited and that the usage of CDN features amplified, fortified, and scaled the attack. Registration of domain and subdomain names, management and availability of those domains, and the shielding of origin IP addresses are examples of CDN features the attackers leveraged to make the campaign more effective.
Looking at our data, Akamai observed the abuse of the CDN vendor proxying traffic from the phishing campaign domains and subdomains going back to at least early June 2021, indicating that the attackers flew under the radar for quite some time. Once details became clear, Akamai threat researchers worked proactively with the security team of the abused CDN vendor to help mitigate the scam. While the competition between security and web performance providers can be fierce, we have a role to play for the greater good of the InfoSec community — combining forces to disrupt threat actors conducting criminal campaigns across the global internet.
Summary
The internet is the conduit powering global connections across both our personal and professional lives. With that notion in mind, quickly collaborating with our competitors was the obvious thing to do, making sure they were well informed and had all the relevant information to eliminate a phishing campaign leveraging their CDN features. Abuse of service providers by threat actors to execute more resilient, trustworthy, and evasive attack campaigns is not new to the threat landscape. But this attack campaign should be seen as an important reminder for us all to remain vigilant, build our platforms with security in mind, and collaborate as an industry to make the internet safer.