Confluence Server Webwork OGNL Injection (CVE-2021-26084): How Akamai Helps You Protect Against Zero-Day Attacks
Recently Atlassian has disclosed a critical remote code execution (RCE) vulnerability in its Confluence server and Data Center products (CVE-2021-26084), which might allow unauthenticated users to execute arbitrary code on vulnerable servers.
The Core Issue
The vulnerability is an Object-Graph Navigation Language (OGNL) injection in one of Confluence’s “Velocity” (templating engine) templates that could be triggered by accessing “/pages/createpage-entervariables.action” and potentially other URLs as well. Some proof-of-concept (PoC) exploits and our data suggest additional URLs, although those are not seen in the original patch analysis.
The parameters “queryString” and “linkCreation” allow attackers to inject JAVA code. Figure 1 shows the differences between the patched and unpatched versions of Confluence Server.
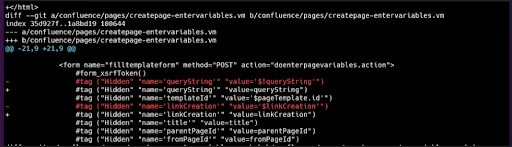 Fig. 1: The character “$” was removed for 2 tags (https://github.com/httpvoid/writeups/blob/main/Confluence-RCE.md)
Fig. 1: The character “$” was removed for 2 tags (https://github.com/httpvoid/writeups/blob/main/Confluence-RCE.md)
Massive Malicious Activity
The exploitation complexity of this vulnerability is low, and since the disclosure on August 25, tens of (PoC variants have emerged. As it happens with other zero-day RCEs, some of those PoCs were adopted in no time by several threat actors, while first mass reconnaissance and exploitation attempts were already observed on August 28.
Current attack campaigns are already reported to deploy XMRig and Kinsing cryptocoin miners, and more recent ones also include Tsunami/Kaiten DDoS bots.
Although the early adopter attackers copy-pasted the existing PoCs, we now see in our data the natural evolution of variants in the wild. As well as the original two URLs that were initially published, we now have these variants:
/pages/createpage.action
/pages/createpage-entervariables.action
/pages/doenterpagevariables.action
/confluence/pages/createpage-entervariables.action
/confluence/pages/doenterpagevariables.action
/collaboration/pages/createpage.action
/jirapages/doenterpagevariables.action
/wiki/pages/doenterpagevariables.action
/-/media/pages/doenterpagevariables.action
/ae/en/pages;/createpage-entervariables.action
/link/lookup/pages;/createpage-entervariables.action
/pages;/createpage-entervariables.action
In the examples above, we can see that attackers are already utilizing a known evasion technique by adding a semicolon in the path (which represents the “path parameters“). Many servers that support path parameters will strip the semicolon before calling the URL, thus successfully reaching the vulnerable Confluence resource, while possibly evading URL-based detection.
As shown in Figures 2–4, in just the last 24 hours, we observed on our global platform:
Almost 2 million attempts to scan and/or exploit these vulnerabilities
88,378 unique hosts targeted
91% of attack activity targeted against Commerce, High Technology, Manufacturing, and Financial Services verticals
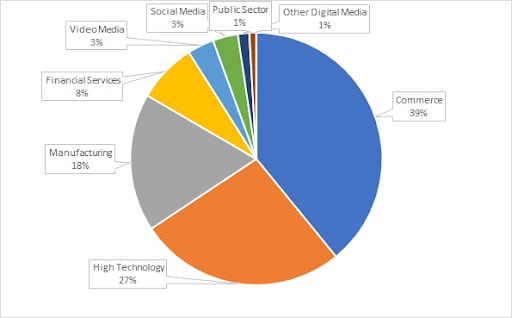 Fig. 2: Most targeted verticals
Fig. 2: Most targeted verticals
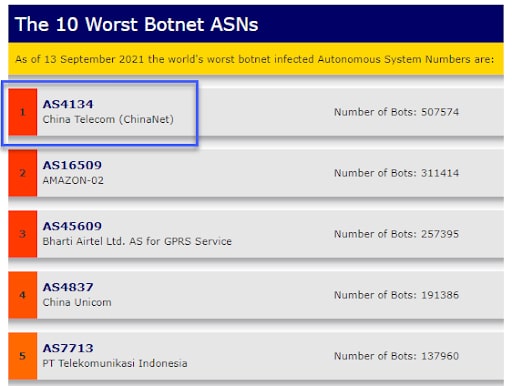
7,456 unique IPs involved in these attempts
- Top 3 ASNs involved in the attacks were AS4134, AS14061, and AS15169, which are known to be the origin of many malicious activities on the internet (despite being operated by legit cloud providers)
Fig. 3: Top 10 worst botnet ASNs reported by Spamhaus
Most of the attacks originated from the United States (43%), China (15%), and India (10%)
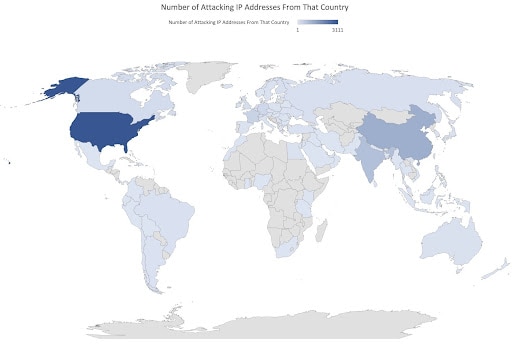 Fig. 4: Number of attacking IP addresses by country
Fig. 4: Number of attacking IP addresses by country
From our experience with similar vulnerabilities in the past, there is a real concern that these campaigns will level up to deploy server-side ransomware to lock companies’ knowledge base or trade with corporate secrets.
Mitigating Zero-Day Attacks
The protection provided by Akamai’s platform against web exploitation attempts, including many of the zero-day attacks, benefits from Akamai’s threat detection ecosystem. Furthermore, Akamai’s vast and worldwide coverage provides its customers with unprecedented visibility into threat intelligence, which is translated into protections. “Layered defense” is not just a marketing phrase when operating at Akamai’s scale. Besides the threat intelligence–based Client Reputation, which includes deeper protection layers, such as scanning activity and client requests anomaly detection, Akamai provides HTTP request compliance checks and a collection of generic Kona Site Defender rules to identify “weaponized” adversarial payloads.
Figures 5 and 6 show examples of a real attacker, sending a weaponized HTTP request (i.e., a request with the ability to deploy malware or to take over the server) detected by existing rule sets.
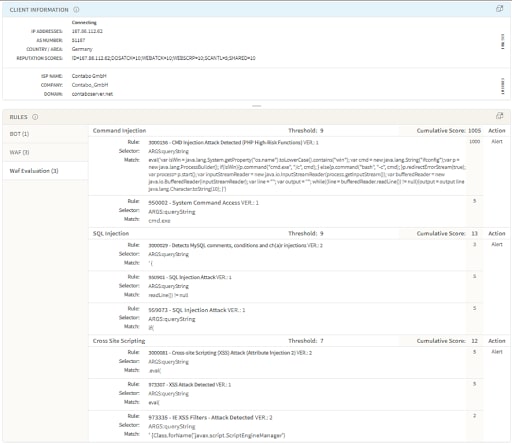 Fig. 5: Detected by Akamai Adaptive Security Engine
Fig. 5: Detected by Akamai Adaptive Security Engine
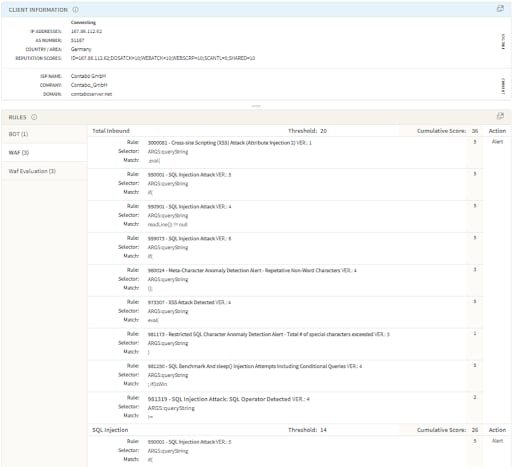 Fig. 6: Detected by Kona Rule Set
Fig. 6: Detected by Kona Rule Set
Besides detecting the attack due to the maliciousness of the origin known to Akamai Client Reputation (Web Attacker, Web Scanner, etc), the attack is also detected by existing generic rules that are aimed at detecting dangerous commanding patterns used by attackers.
Adaptive Security Engine is detecting and blocking the current weaponized exploits based on existing rules in command injection and cross-site scripting attack groups.
· 950002 — CMD Injection Attack Detected (OS Commands 4)
· 3000156 — CMD Injection Attack Detected (PHP High-Risk Functions)
· 973307 — Cross-site Scripting (XSS) Attack (Eval/Atob Functions)
· 3000081 — Cross-site Scripting (XSS) Attack (Attribute Injection 2)
· 3000005 — CMD Injection Attack Detected (OS commands with full path)
Automated Attack Groups is detecting and blocking the current weaponized exploits based on existing rules in command injection and cross-site scripting attack groups.
· 1000002 — XSS Attack Group
· 1000005 — CMD Injection Attack Group
Kona Rule Set is detecting and blocking the current weaponized exploits based on existing
rules in PHP injection and cross-site scripting attack groups.
· 958976 — PHP Injection Attack (Common Functions)
· 950109 — Multiple URL Encoding Detected
· 973307 — XSS Attack Detected
· 3000081 — Cross-site Scripting (XSS) Attack: Attribute Injection
Final Note
It is the same pattern we have seen in the past, where threat actors show an ability to adapt PoC exploits for fresh zero-day vulnerabilities within a single day. Having a web application firewall as another protection layer might buy you some very precious time until a patch is deployed on the vulnerable target, and significantly reduce the risk on your web applications.
The Akamai Threat Research team continues to monitor any new exploit variations, and rapidly responds by providing rule updates and latest recommendations to customers.