Executive summary
- On February 2026’s Patch Tuesday, Microsoft patched CVE-2026-21513, a security features bypass vulnerability within MSHTML framework.
- The vulnerability affects all Windows versions, is actively exploited in the wild, and carries a CVSS score of 8.8.
- Using PatchDiff-AI, Akamai researchers performed automated root cause analysis of the patch and correlated it with an observed in-the-wild exploit attributed to the Russian state-sponsored threat actor APT28.
- This blog post provides a technical breakdown of CVE-2026-21513, a description of its root cause, and an analysis of its exploitation.
- We have included a list of indicators of compromise (IOCs) in this blog post to assist in defense against this threat.
The vulnerability
Microsoft’s February 2026 Patch Tuesday addressed 59 vulnerabilities, including six actively exploited zero-days. CVE-2026-21513 stands out because of its active exploitation, high impact, and ability to bypass browser security boundaries and trigger arbitrary file execution.
We used the multi-agent system called PatchDiff-AI to analyze CVE-2026-21513 and its patch. PatchDiff-AI generated a detailed report that reveals insights about the vulnerable component and the attack vector.
The root cause
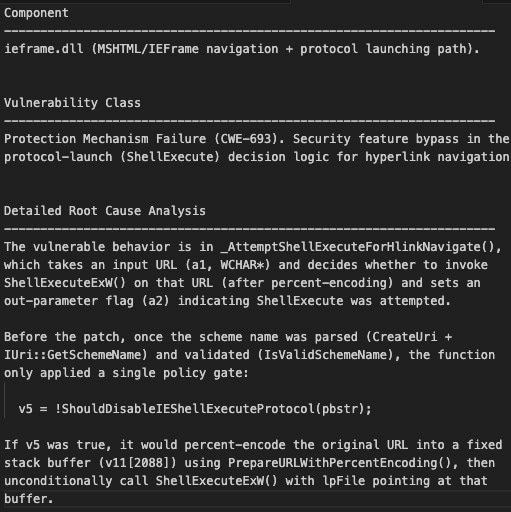
The report by PatchDiff-AI ties CVE-2026-21513 to a specific function within ieframe.dll (Internet Explorer frame). The vulnerability resides in the logic responsible for handling hyperlink navigation. Insufficient validation of the target URL allows attacker-controlled input to reach code paths that invoke ShellExecuteExW, enabling execution of local or remote resources outside the intended browser security context (Figure 1).
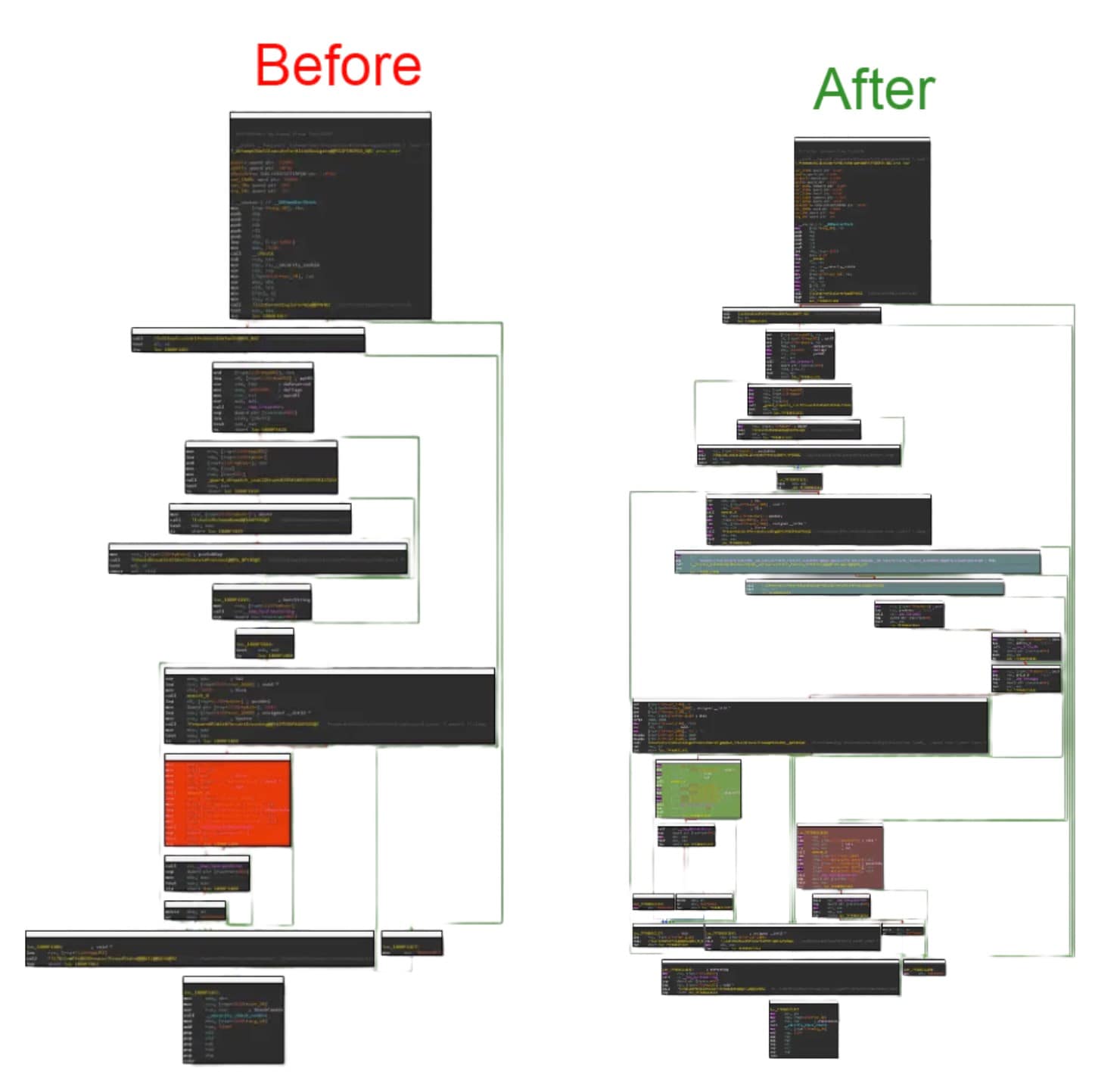
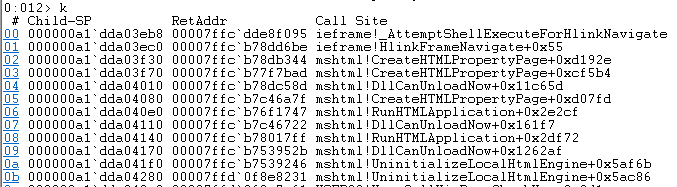
The code path visualization in Figure 2 shows flow differences in the function _AttemptShellExecuteForHlinkNavigate applied by the patch.
To trigger the vulnerable code block, we needed to invoke Internet Explorer using an ActiveX form to track down what exactly initiates the flow. Using the component of “System.Windows.Forms.WebBrowser” and displaying it on the “System.Windows.Forms.Form” object, we loaded an HTML file that was parsed and constructed using the MSHTML and IEFRAME modules.
Another important component is the “htmlfile,” which exposes the DOM interface and allows us to manipulate it in a way that will trigger the vulnerable function.
While exploring the vulnerable code and the function calls that trigger it, we were led to the following exploit.
The exploit
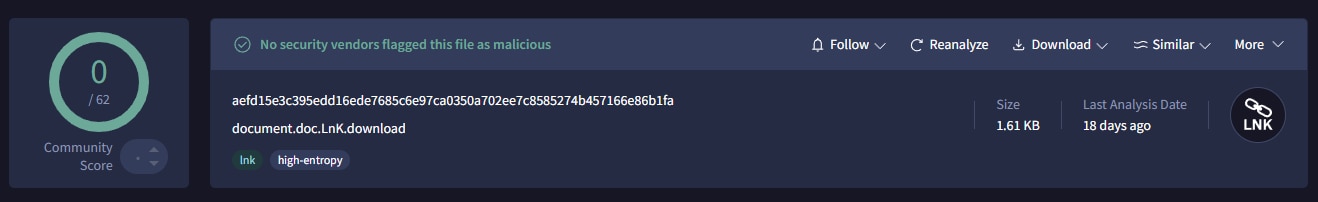
By correlating the vulnerable code path with public threat intelligence, we identified a sample that was leveraging this functionality: document.doc.LnK.download.
The sample was first submitted to VirusTotal on January 30, 2026, shortly before February’s Patch Tuesday, and is associated with infrastructure linked to APT28, an active Russian state-sponsored threat actor (Figure 3).
This payload involves a specially crafted Windows Shortcut (.lnk) that embeds an HTML file immediately after the standard LNK structure.
The LNK file initiates communication with the domain wellnesscaremed[.]com, which is attributed to APT28 and has been in extensive use for the campaign’s multistage payloads.
The exploit leverages nested iframes and multiple DOM contexts to manipulate trust boundaries.
This technique allows the attacker to bypass Mark of the Web (MotW) and Internet Explorer Enhanced Security Configuration (IE ESC), effectively downgrading the security context before triggering the vulnerable navigation flow. Ultimately, this allows attacker-controlled content to reach a code path that invokes ShellExecuteExW, leading to execution outside of the browser sandbox (Figure 4).
{ h1 = new window[0].ActiveXObject('htmlfile'); };
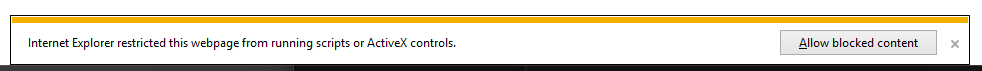
('<html><body><iframe src=%22about:blank%22></iframe><iframe src=%22about:blank%22></iframe>%3cscript defer%3ewindow[1].document.Script.open(%22http:///%22,%22_parent%22)%3c/script%3e</body></html>'));If we run this script in Internet Explorer directly, we will encounter the security feature mentioned above, which warns the user and reduces the chances for successful exploitation (Figure 5).
Successful exploitation will bypass the security features and execute code controlled by the attacker. The screenshot in Figure 6 shows the top of the call stack, a very long one, where we can see the call to the vulnerable function _AttemptShellExecuteForHlinkNavigate.
While the observed campaign leverages malicious .LNK files, the vulnerable code path can be triggered through any component embedding MSHTML. Therefore, additional delivery mechanisms beyond LNK-based phishing should be expected.
The fix
Microsoft introduced stricter validation to the hyperlink protocol that ensures supported protocols (such as file://, http://, and https://) will execute within the browser context rather than being passed directly to ShellExecuteExW.
Protecting your assets
Applying Microsoft’s February 2026 security updates fully mitigates this vulnerability.
APT28’s domains are tracked in Akamai’s proprietary threat intelligence. Akamai Hunt detects and alerts on activity patterns associated with this attack [T1204.001, T1566.001], and automatically notifies customers when vulnerable assets are detected.
PatchDiff-AI quickly analyzes the root cause of a vulnerability, enabling rapid root cause identification of vulnerabilities and accelerating analysis of in-the-wild exploitations.
IOCs
Name |
Indicator |
|---|---|
| document.doc.LnK | aefd15e3c395edd16ede7685c6e97ca0350a702ee7c8585274b457166e86b1fa |
Domain |
wellnesscaremed[.]com |
MITRE Techniques |
T1204.001, T1566.001 |
Tags