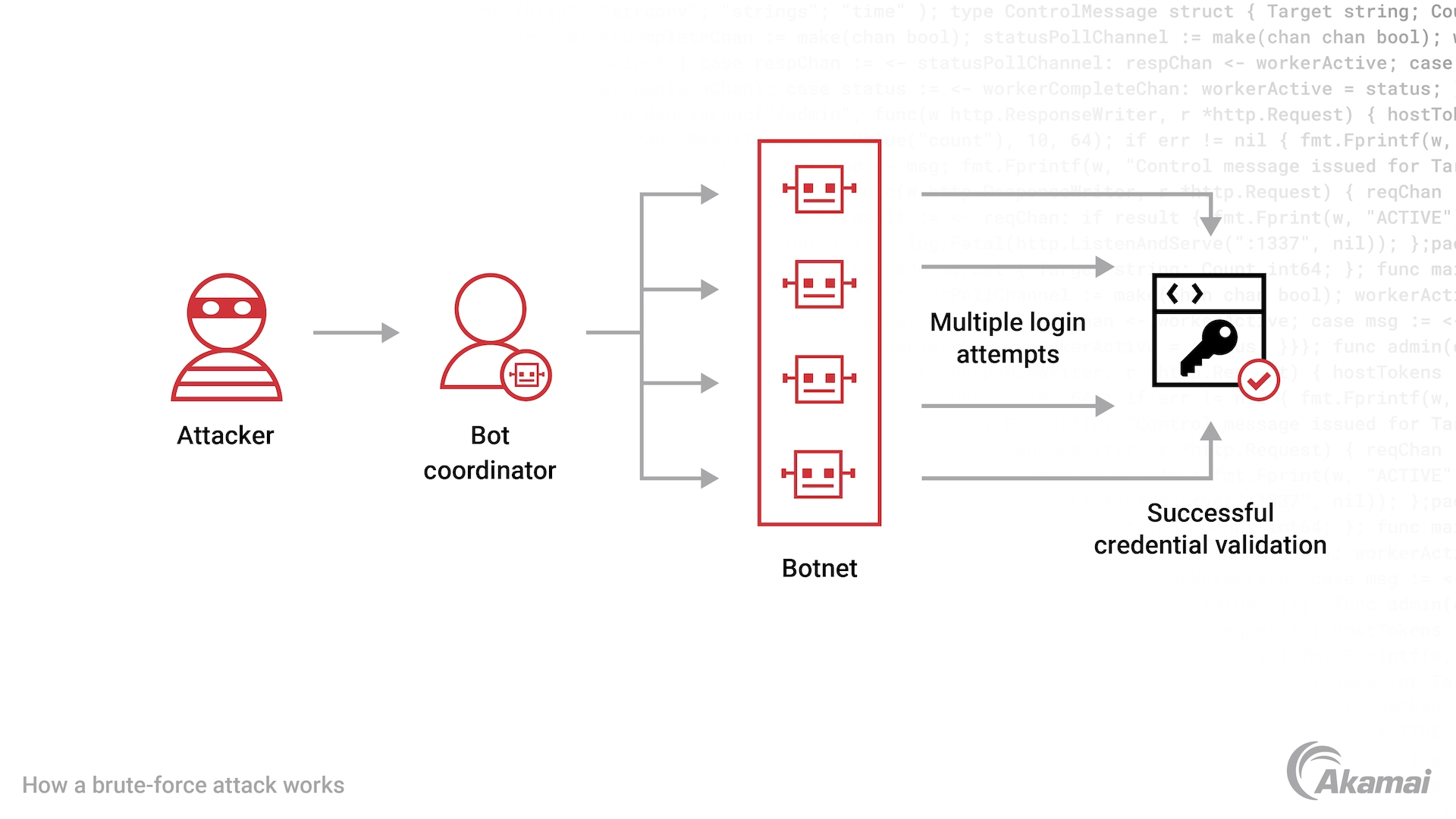
A brute-force attack is a cyberthreat in which attackers use automated tools to repeatedly try username and password combinations until they gain unauthorized access to an account or IT environment. These attacks are typically carried out by botnets that can perform hundreds of thousands of login attempts per hour, increasing the risk of account takeover and data exposure.
Defending against brute-force attacks
In the field of cyberthreats, brute-force attacks remain a popular and profitable attack method for cybercriminals. In these attacks, threat actors attempt to access user accounts by entering a large number of username and password combinations into login pages on websites or web applications, cycling through millions of possible credentials using significant computing power. These attacks are often carried out using botnets that automate large numbers of login attempts across distributed systems. While automation increases the scale of attacks, modern defenses such as rate limiting, MFA, and bot detection significantly reduce their success rates.
It’s critical to block these attacks before they gain access to user accounts and personal data. Once inside an account, brute-force attacks are much more difficult to stop, especially if the attackers are able to decrypt sensitive data, steal password hashes, or access encryption keys. The right bot detection solutions must be able to differentiate between legitimate bot traffic from malicious bots, while also tracking bots and botnets (short for “robot networks”) as they rapidly evolve in an attempt to evade detection. Controls such as CAPTCHA challenges, account lockout policies, and IP address reputation analysis can further reduce attack success rates when used alongside bot management.
As the world’s most distributed computing platform, Akamai offers superior bot security technology with intelligence gleaned from 11.5 billion bot requests and 280 million bot logins daily. With Akamai anti-bot security solutions, cybersecurity teams can effectively block brute-force attacks without slowing down performance or impacting the online experience for legitimate users across websites, mobile apps, and Android or iOS environments.
How do brute force attacks work?
In a brute-force attack, hackers use numerous username/password combinations to gain access to a user account or an IT environment. Most modern brute-force password attacks rely on automated tools—such as bots, password-cracking software, or distributed computing resources—that can rapidly generate and test large numbers of credential combinations. Many of these password-cracking attacks are carried out by botnets, which is a network of bots comprising hundreds or thousands of computers infected with malware, which allows them to be controlled by a single attacker.
Common types of brute-force attacks include:
- Simple brute-force attacks. A simple brute-force attack systematically tries every possible character combination for a password or PIN until the correct one is found. Simple attacks are often successful because so many users don’t use a password manager and still rely on weak passwords with common words that can be easily guessed.
- Dictionary attacks. In a dictionary attack, attackers test passwords from predefined wordlists—often containing common words, phrases, and previously leaked passwords—against one or many user accounts. They also amend words with special characters and numbers to identify possible passwords.
- Hybrid brute-force attacks. This format uses external logic to determine password variations and possible combinations that are most likely to be successful, then tries as many variations as possible.
- Reverse brute-force attacks. In a reverse brute-force attack, attackers start with a known or common password—often obtained from a breach—and attempt to identify accounts that use that password.
- Credential stuffing. Attackers use known passwords acquired from data breaches to attempt to log in to a variety of other sites. This approach is successful even when users have complex passwords because many individuals reuse the same credentials across a wide range of accounts.
Offline brute-force attacks. In these attacks, cybercriminals work offline to crack stolen password hashes or encryption keys, often using rainbow tables to speed up the process without triggering login defenses.
Blocking brute-force attacks requires technology that can quickly detect and mitigate malicious traffic from bots and botnets. Yet because so much web traffic today originates from good bots as well as bad, superior solutions must be able to distinguish and block bots with few or no false positives. That’s where Akamai technology excels.
Stop brute-force attacks with Akamai Bot Manager
Akamai Bot Manager provides the visibility and control that security teams need to protect against brute-force attacks and many other bot-related threats. Bot Manager features unmatched detection and mitigation capabilities that effectively stop bad bots and botnets while enabling legitimate bot-related activity to operate effectively and safely.
Using multiple patented technologies to detect and mitigate bots, Akamai Bot Manager stops bots where they make initial contact instead of allowing them to reach a site first. Detection engines are continually updated with threat intelligence produced by Akamai’s security research teams, which analyze hundreds of terabytes of attack data daily.
To distinguish malicious from legitimate bot traffic, Bot Manager collects data on “clean traffic” across a wide distribution of data types and in large volumes of traffic on Akamai Cloud. Our platform protects some of the largest and highest-profile companies in the world — which are often the targets of the most advanced bot operators. When a new bot is detected at one customer, the data is added to a known bot library and informs the algorithms for all customers.
Bot Manager uses a scoring model to calculate the likelihood that any request is coming from a bot vs. a human being. High-scoring requests (definitely a bot) can be aggressively mitigated, while low-scoring requests (likely a human) can be watched and monitored. For scores in the “gray area,” Bot Manager issues cutting-edge challenges that can slow attacks and drive up costs for bot operators.
Benefits of Akamai bot management technology
With Akamai Bot Manager, security teams can:
- Protect organizations, users, and IT environments from the impact of brute-force attacks
- Easily distinguish legitimate bot traffic from malicious attacks
- Build customer and partner trust with protection from fraudulent activity
- Reduce the burden of remediating the fallout of bot attacks such as replacing stolen accounts, checking for compromised accounts, and managing user complaints
- Enhance operational control to reduce business and financial risks, while controlling IT spend and strategically managing partner bots
- Improve decision-making with data-driven analysis and reporting that allows IT administrators to make creative and effective choices about security posture, risk tolerance, and IT operations across their network security
Frequently Asked Questions
To combat brute-force attacks, security teams can deploy bot management technology, two-factor authentication, or multi-factor authentication solutions, and encourage users to adopt strong passwords. Unique passwords are often longer passwords with a mix of lowercase and uppercase letters as well as numbers and symbols. Password length impacts the amount of time it takes for bots and botnets to guess your password.
Credential stuffing is a brute-force attack in which attackers use previously exposed usernames and passwords from data breaches or the dark web to gain unauthorized access to accounts on other websites or applications. This attack is effective because many users reuse the same credentials across multiple services.
A bot is an automated software program that performs specific tasks without human intervention. While many bots are used for legitimate purposes, malicious bots can generate fake traffic, steal data, or carry out cyberattacks such as brute-force attacks as part of a botnet controlled by an attacker.
Why customers choose Akamai
Akamai is the cybersecurity and cloud computing company that powers and protects business online. Our market-leading security solutions, superior threat intelligence, and global operations team provide defense in depth to safeguard enterprise data and applications everywhere. Akamai’s full-stack cloud computing solutions deliver performance and affordability on the world’s most distributed platform. Global enterprises trust Akamai to provide the industry-leading reliability, scale, and expertise they need to grow their business with confidence.