Address your pressing security challenges with Zero Trust
Why Zero Trust security?
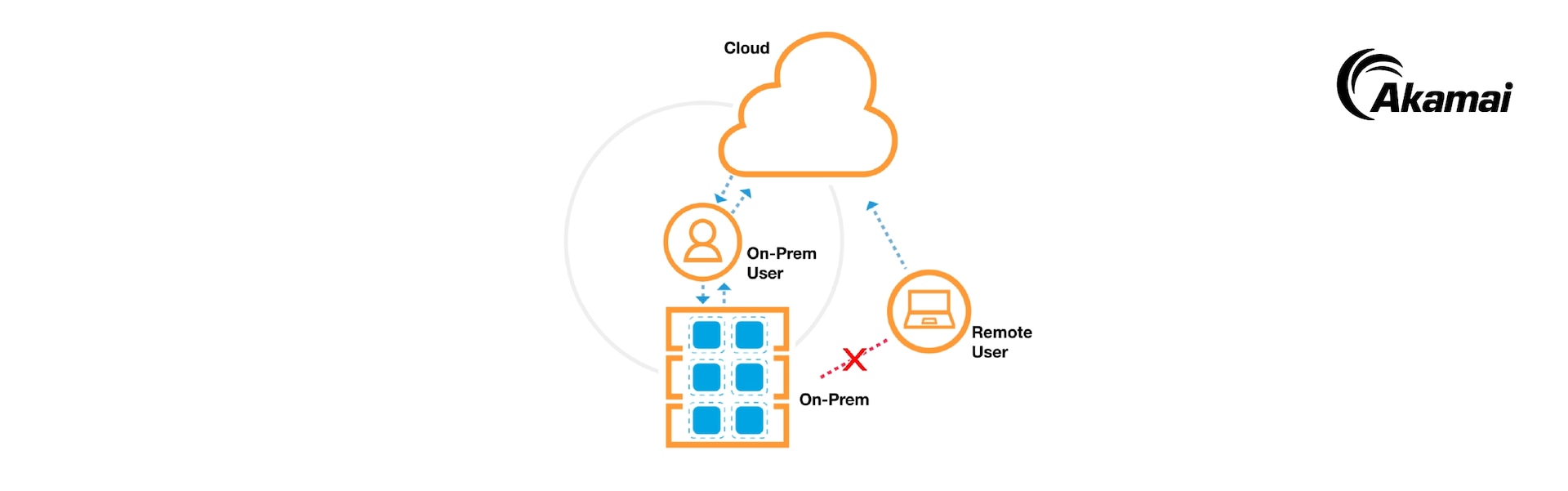
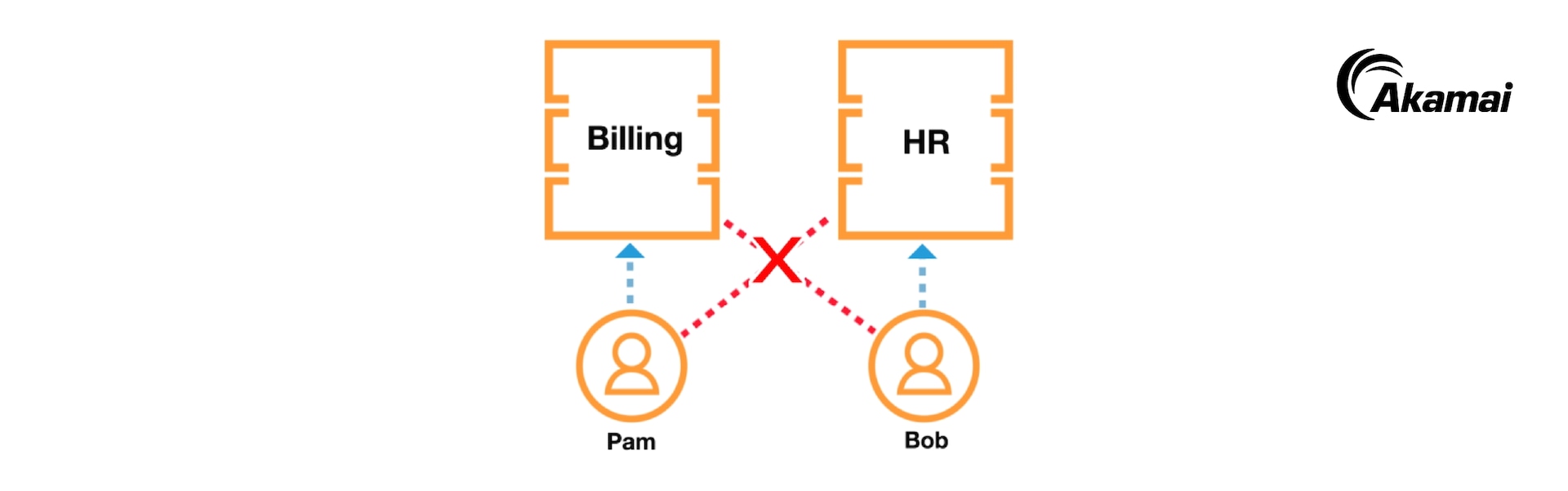
Eliminate reliance on firewalls and VPNs with Akamai’s Zero Trust solutions. Secure your entire IT environment — on-prem, cloud, legacy apps, SaaS, and remote or on-site employees. Gain deep visibility and expert threat detection to stop attacks and prevent lateral movement.
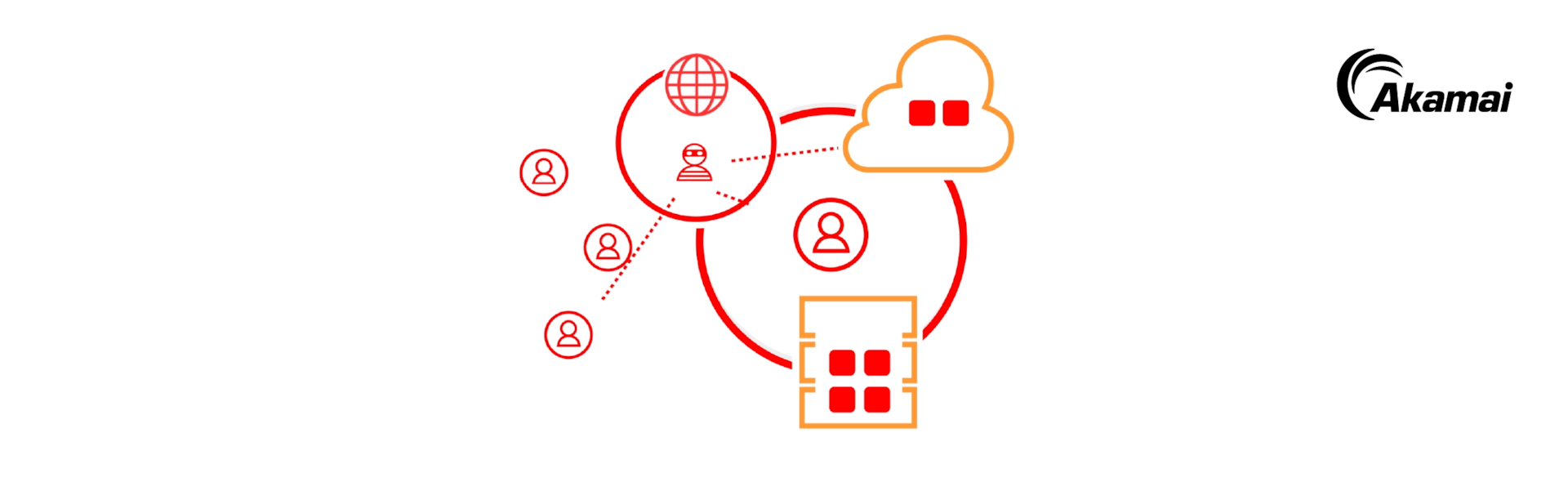
How Zero Trust works
Industry Leading Zero Trust Security Solutions
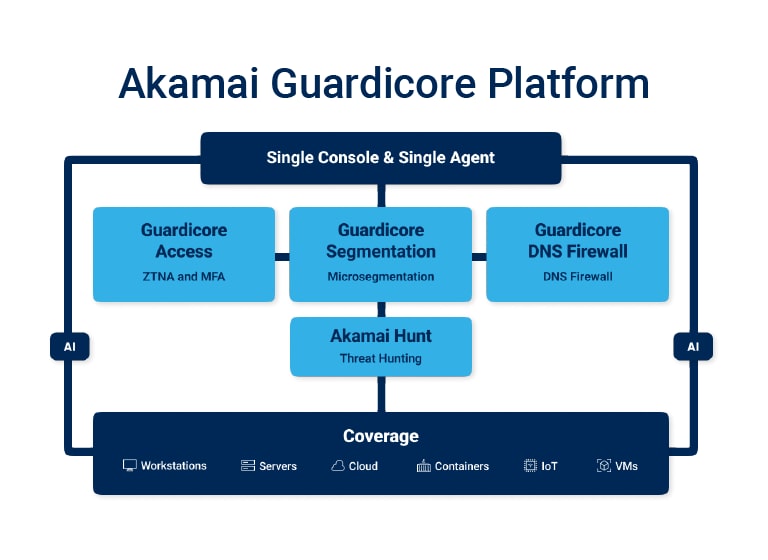
Zero Trust Product Portfolio
Resources
1The Forrester Wave™ is copyrighted by Forrester Research, Inc. Forrester and Forrester Wave are trademarks of Forrester Research, Inc. The Forrester Wave is a graphical representation of Forrester’s call on a market and is plotted using a detailed spreadsheet with exposed scores, weightings, and comments. Forrester does not endorse any vendor, product, or service depicted in the Forrester Wave. Information is based on the best available resources. Opinions reflect judgement at the time and are subject to change.
2Forrester does not endorse any company, product, brand or service including in its research publications and does not advise any person to select the product or services of any company based on the ratings included in such publications. Information is based on the best available resources. Opinions reflect judgement at the time and are subject to change. For more information read about Forrester’s objectivity here.