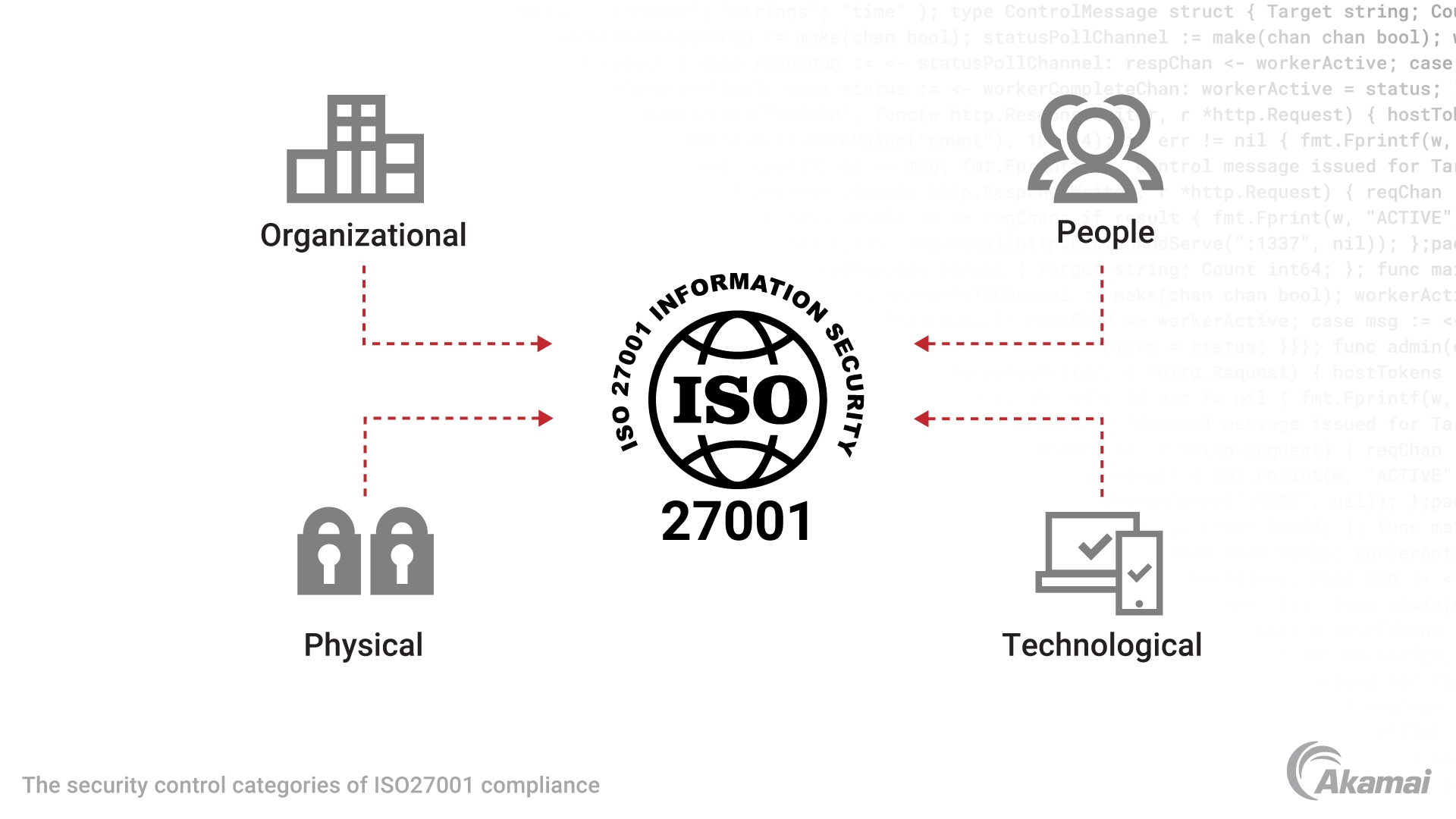
A fundamental approach within the ISO 27001 standard control objectives is that of Zero Trust security. Controls include:
- Access control, to establish physical and logical access controls to information and other associated assets
- Privileged access rights, to ensure “least privilege” access
- Segregation of networks, as part of a Zero Trust security approach
These controls help an organization establish a Zero Trust environment.
Here are three examples of sectors that benefit from implementing Zero Trust under ISO 27001:
ISO 27001 for critical infrastructures
Attacks on critical infrastructures have devastating effects. A relevant example is a security incident at the U.S. oil supplier Colonial Pipeline . The entire Southwest of the United States was affected; all it took to circumvent operations security and infect the company with ransomware was a single compromised password. Critical infrastructures cover many vital services, including utilities, chemical manufacturers, and transport. The critical nature of these services makes them an attractive target for hackers. Unauthorized access and credential exposure that includes the wider supply chain is a central area of focus. The increased connectivity to the broader internet and an expanded attack surface of modern connected industrial units have allowed malicious actors to open once firmly closed doors into critical systems. Implementing ISO 27001 and associated information security policies and procedures mitigates the risk of cyberattacks on critical infrastructures.
ISO 27001 for healthcare
The wider healthcare sector is an ideal target for cybercriminals. The sector is data rich, a critical infrastructure, and highly dependent on technology and supplier relationships. As a result, healthcare institutions are at risk from many forms of cyberattack, including data breaches and ransomware. In 2024, the FBI issued an advisory for critical infrastructure entities, namely within the healthcare industry, regarding ongoing ransomware threats. The FBI’s Internet Crime Complaint Center reported more reports of ransomware attacks targeting healthcare in 2022 than any other critical infrastructure sector. As a complex service, healthcare can benefit from the rigor required to implement an ISMS as part of ISO 27001 certification. A Zero Trust approach to information security risks will ensure that healthcare organizations can control access to sensitive data and maintain control over critical systems and services.
ISO 27001 for financial services
A 2023 International Monetary Fund (IMF) survey across 51 countries found that cyberthreats against financial instructions are “proliferating,” indicating a proper response by the sector is urgently needed. The financial industry suffers a variety of cyberattacks, including ransomware, data breaches, and DDoS attacks. The 2022 Verizon Data Breach Investigation Report broke the type of attacks against the financial sector into “Ransomware, Use of Stolen Creds, and Phishing,” covering 80% of breaches. With stolen credentials playing an integral role in most attacks in the sector, ISO/IEC 27001 provides critical mechanisms for the financial sector to enforce a Zero Trust approach to unauthorized access.