Why Zero Trust Needs the Edge
Backhauling traffic destroys performance, and backhauling attack traffic can destroy even more. Nevertheless, in a traditional security deployment model, we are faced with the lose-lose options of either backhauling all traffic to the security stack or allowing some accesses to not go through the security stack. Of course, in the modern world where cyberattacks can cause enormous damage, the latter option is not really an option at all. All traffic must route through a robust security stack. So how do we accomplish this goal without backhauling? The answer is Zero Trust security deployed and delivered as an edge service.
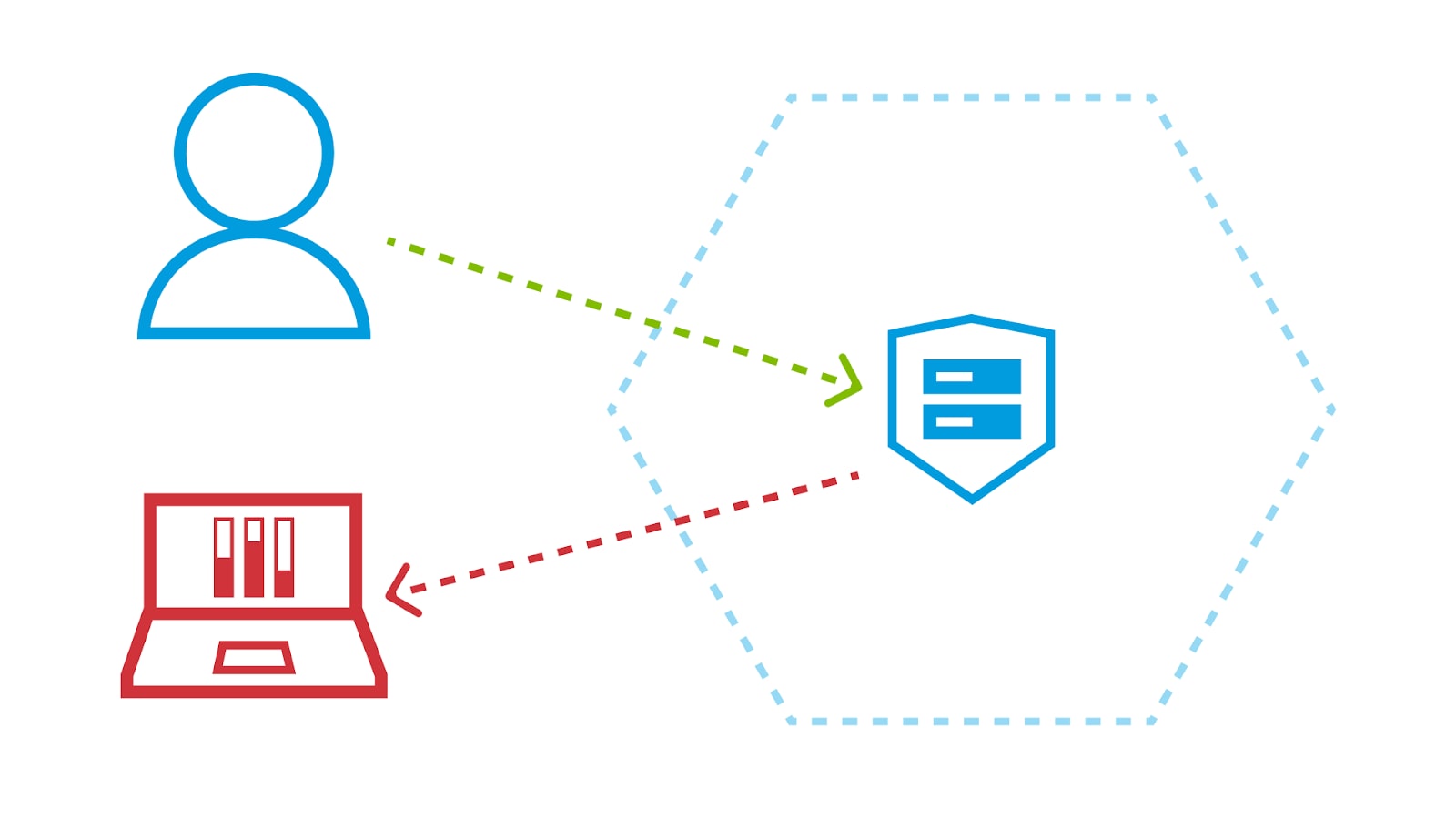
Looking deeper at the traditional deployment model, let's first consider the case of employees accessing internet-based web applications. Such applications could, for example, be SaaS applications that are necessary for work, web applications that are used in a work context, or other web applications that are being used for personal activities. Securing these traffic flows calls for a secure web gateway (SWG).
The SWG can ensure that acceptable use policies are being enforced, an employee is not accidentally trying to access phishing sites, and malware is not being downloaded onto the employee's device, among other things. The SWG is an essential component of the security stack, and a strong cybersecurity posture requires that all access to internet-based web applications goes through the SWG.
The problem is that the traditional SWG deployment model, in which the SWG is deployed as an appliance or virtual appliance in one or a small handful of locations, requires backhauling. Of course, if nearly all employees are working in one or a small number of office locations, then those SWG locations can be chosen to be in or near those offices, with no need to backhaul. This scenario may have applied to some enterprises some number of years ago, but it's safe to say that this scenario no longer applies today or in the future.
Employees frequently work remotely, so now the traffic has to be backhauled to a SWG, typically by means of a remote-access virtual private network (VPN), which destroys performance and has other scaling challenges. Even when employees are in the office, if they are in a satellite office, then the traffic again must be backhauled to a SWG, typically by means of dedicated inter-office telecommunications links (e.g., MPLS) -- a process that is very expensive.
 Backhauling Traffic Destroys Performance
Backhauling Traffic Destroys Performance
Moreover, the SWG is not the only essential component of the security stack. A strong cybersecurity posture requires that all traffic flows be subject to access control and inspection, not just those internet-bound flows that go through the SWG. This requirement is a fundamental tenet of Zero Trust.
Consider, specifically, the case of employees accessing internal corporate-owned applications that could be deployed in a corporate datacenter or in the cloud. These traffic flows also must go through the security stack, through a component that is often referred to as Zero Trust Network Access. This component is essentially an Identity-Aware Proxy whose job is to ensure that each application can be seen and accessed only by users who have already been strongly authenticated and authorized to access that application.
The point here is that in a Zero Trust security posture, all traffic flows need to go through the security stack, and in the traditional deployment model, this requirement forces backhauling, with all of the associated problems. Backhauling is expensive and destroys performance, but it gets worse when we consider that some of this traffic could be attack traffic.
After all, dealing with attack traffic is one of the functions of the security stack, and we do not know which traffic is attack traffic until it gets to the security stack. Backhauling attack traffic just gives it that much more opportunity to interact with network links and devices, and to do damage, possibly taking out critical upstream links and rendering the entire security stack inaccessible. So what are we to do?
Rather than backhauling traffic to the security stack, we can deploy the security stack where the traffic is, at the edge. In this model, a full Zero Trust security stack is provided as a service running on edge infrastructure. With the security stack at the edge, it is near all users/employees, wherever they may be working, whether that is in an office, at home, or on the road. Likewise, it is near all applications, wherever they may be deployed, whether in a data center, in a cloud, or under someone's desk.
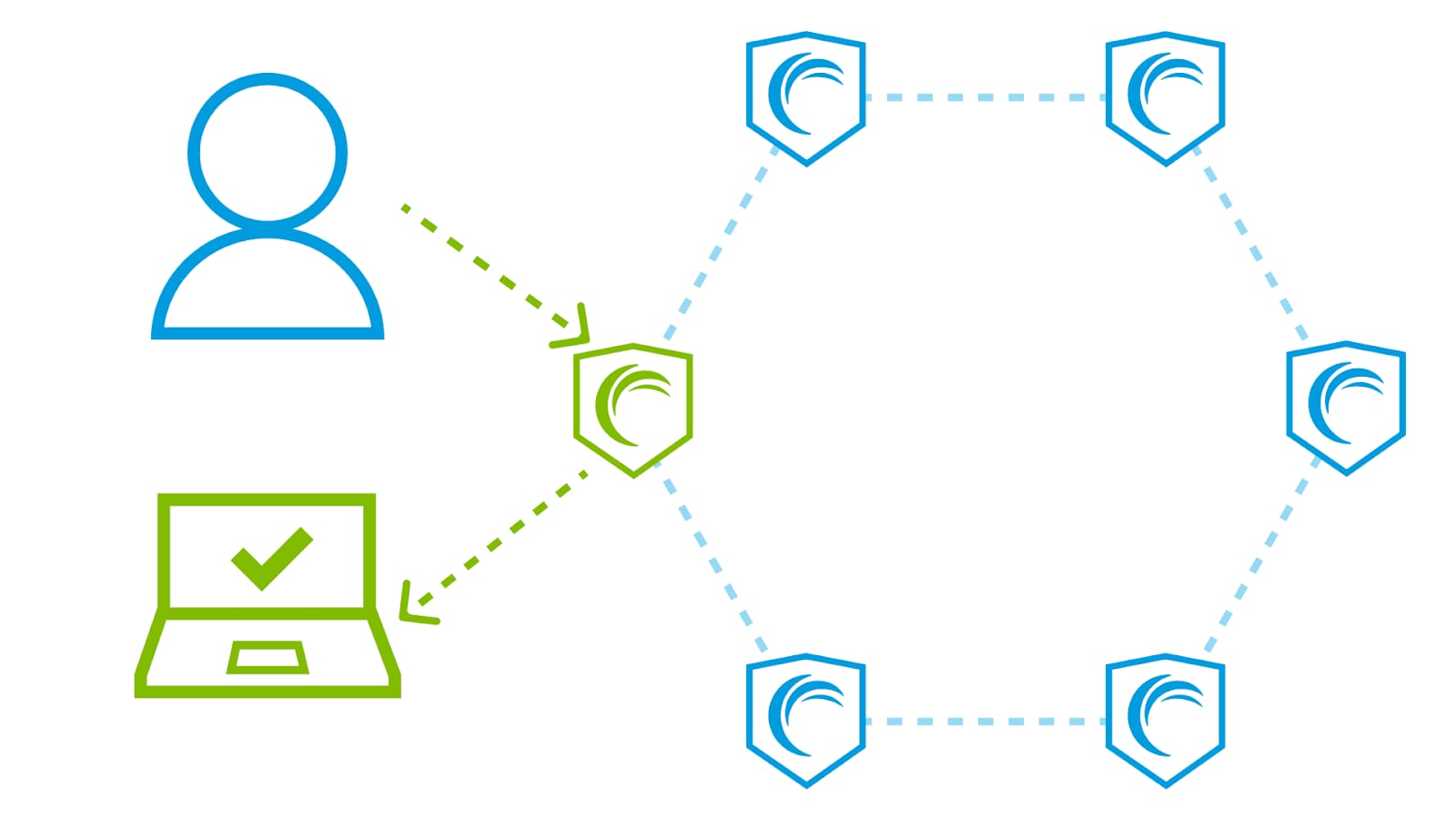 Backhauling when security is deployed around the edge
Backhauling when security is deployed around the edge
At the edge, near the users and applications, the security stack is right where it's needed, where the traffic is, with no need for backhauling. In addition, at the edge, the security stack is near any attackers, whether they are compromised corporate devices or bots, so the attack traffic can be blocked near its source, before it has a chance to do any harm.
With a Zero Trust security stack as an edge service, all traffic flows can be secured without backhauling.



