When organizations talk about breach incidents, the conversation almost always centers on how the attacker got in and, while that makes sense, it’s also incomplete. Attackers assume breach is inevitable. Resilience is about assuming; containment is not.
In this blog post, I’ll discuss reframing cyber resilience away from just perimeter defense or business continuity and more toward controlling the blast radius because the difference between an incident and a crisis is almost always lateral movement. When every control technically worked, alerts fired, and playbooks ran, and the business still went offline, the question arises: What happened?
Most breaches don’t fail security audits; they fail operational resilience and control. No board presentation ever starts with “We were compromised.” They all start with “Customers were impacted.”
Assume that a breach is only a matter of time
What cyber resiliency allows you to do is take the hit but keep moving forward. Operators and defenders can continue to triage as usual. When we talk about script kiddies, hacktivism, enterprise criminals, or state-sponsored attackers, their motivations sometimes far outweigh our ability to prevent the breach.
According to a Proofpoint survey, 68% to 76% of CISOs assume that breach is inevitable. With the rise of ransomware as a service (RaaS) and other mainstream toolkits that established groups of threat actors are still using today, it’s only a matter of time.
Tech and government agencies aren’t failing because they lack tools; they’re failing because their environments were never designed to absorb compromise safely. Different sectors, different tools, same architectural failures.
When outages cascade, customer trust erodes, regulators get involved, and recovery timelines can stretch from hours to weeks: this is not the conversation you want to have with leadership.
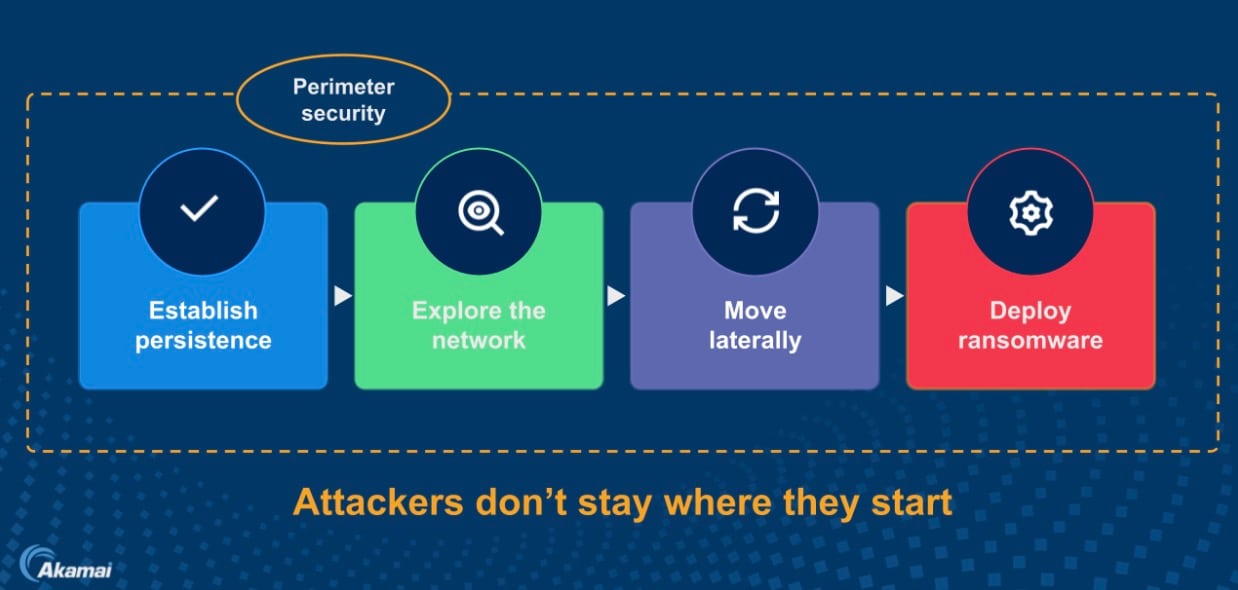
Cyber resilience isn’t a technical aspiration — it's a requirement for business survival. The board is increasingly asking whether security architectures are designed for prevention only, not absorption or disruption. Detection without containment is observation; containment is control — because attackers don’t stay where they start (Figure 1).
Lateral movement determines impact
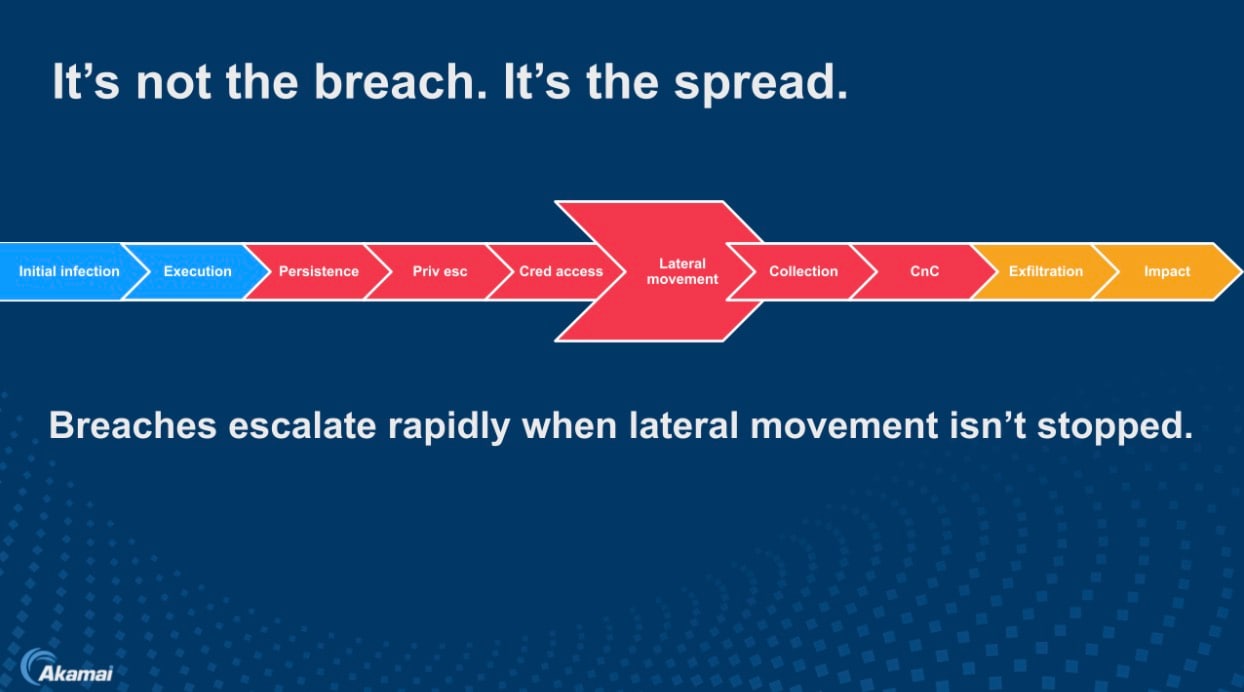
If you map modern attacks across the kill chain, one phase consistently determines impact: lateral movement. Initial infection is noisy and sometimes detected; lateral movement is quiet, fast, and devastating. Once attackers move east-west leveraging common administrative tools, they escalate privileges, harvest credentials, and position themselves near crown jewel assets (Figure 2).
Breaches escalate not because defenders are slow, but because networks were never designed to say “no” internally. Picture one compromised workload with 1,000 allowed connections. That’s not lateral movement; that’s permission expansion. The speed of spread matters more than the speed of detection. Most flat networks weren’t designed — they were inherited.
Cyber resilience outcomes are often business driven
Cyber resilience is often framed as a technical discipline, but its outcomes are unmistakably business driven. Resilience reduces regulatory exposure, limits reputational damage, and keeps critical services online during disruption. More important, it shortens recovery timelines and stabilizes executive decision-making under pressure.
The goal isn’t perfection but predictability. When leadership knows the blast radius is constrained, incident response becomes controlled rather than reactive, and recovery becomes an operational exercise instead of a catastrophic event. Resilience is what helps leadership make calm decisions instead of having to react under pressure. This is why cyber insurance questionnaires now ask about containment, not just controls.
Microsegmentation: Changing attack economics
Attackers don’t stay where they start because they don’t need to. Perimeter security alone cannot deliver resilience. And microsegmentation changes the economics of an attack. Instead of relying on IP ranges, firewall access control lists (ACLs), or VLANs alone, microsegmentation enforces those concepts as well as policies based on identity, process, and application behavior.
In a hybrid environment, ransomware doesn’t fan out — it stalls and lingers. Ideally, you’d want an attacker hitting friction at every step, and experiencing automatic containment . That shift alone can turn a catastrophic event into a manageable incident.
A common mistake that many organizations make during mergers and acquisitions (M&A), for example, is focusing on connectivity first and control later. Speed matters, but uncontrolled speed creates systemic risk. The goal isn’t to block integration, but to enable it safely.
That means visualizing dependencies, approving only explicit flows, and defaulting everything else to deny until mean time to innocence is determined. Without microsegmentation, one compromised user becomes a gateway to finance systems, backups, domain controllers, and executives. With microsegmentation, the same initial event is isolated, logged, and contained.
Attackers move by opportunity
Mature organizations treat security policies as software: versioned, testable, and reversible. Microsegmentation without vulnerability awareness is a static defense in a dynamic threat landscape. What matters isn’t only knowing how the network is drawn, but where risk exists right now and whether policy adapts before attackers do.
VLANs enforce trust by proximity, but attackers move by opportunity, which is why identity and process-level policy matters. Enforcing intent down to the workload and process are the types of security controls that shouldn’t trade off viability, feasibility, and visibility across hybrid infrastructures and workloads.
Attackers exploit rigidity
The most effective architectures are hunt-friendly by design, enforcing policy while generating clean, actionable telemetry. Modern resilience isn’t just about staying up, it’s about maintaining control while under attack. That’s the difference between security that survives audits and security that survives reality.
Organizations that can’t re-deploy, re-identify, and re-assert control under pressure don’t have a resilience problem, they have a rigidity problem. And rigidity is what attackers exploit.
Understanding the continuous operating model of cyber resilience
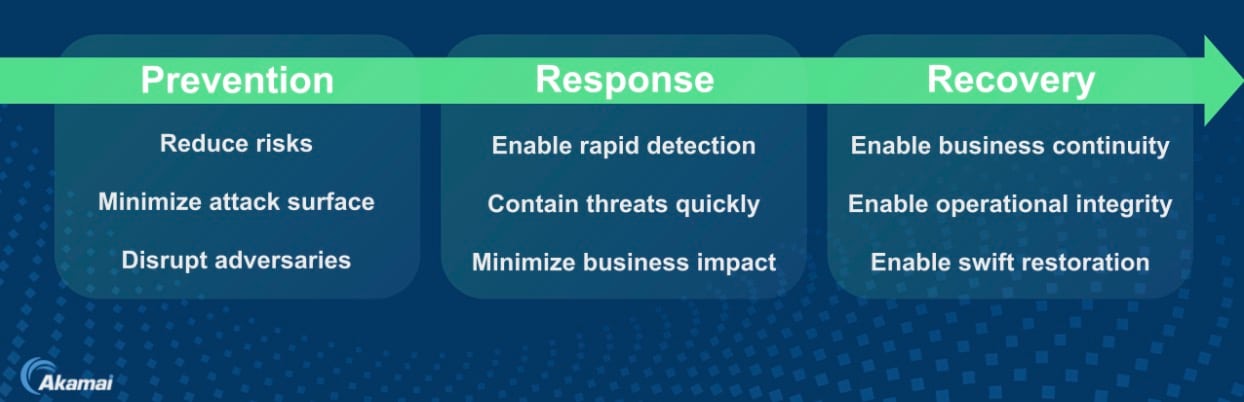
Cyber resilience isn’t a linear checklist or a phase; it’s a continuous operating model (Figure 3).
Cyber resilience starts with deployment and identification, because you can’t protect what you can’t see or classify, and most organizations still discover their environment only after an incident forces the issue.
Detection and response aren’t about stopping every attack. They’re about containing impact fast enough to keep the business running while recovery is already in motion. That’s the real measure of resilience: not whether an incident occurs, but how quickly and decisively an organization can recover without losing trust, data, or momentum.
The organizations that struggle are the ones that treat these as separate initiatives. Detection feeds containment, containment simplifies recovery, and recovery informs better policy. The speed of that loop, not the number of tools, defines maturity. Defender fatigue is a real thing.
Indeed, I’ve spent four years in the Akamai Security Operations Command Center (SOCC) fighting attacks 10 to 12 hours a day. Often when I’m investigating or reverse engineering an attack, the network or environment does not have the correct attributes or details to identify the asset, configuration, and services supported on the system. In that case, it’s not telling the truth about what it is, and that can lead to delays involving additional investigation time and due diligence. Hunting works when the environment tells the truth.
This is where Zero Trust becomes practical. Policy is no longer static or network-bound; instead, it’s software-driven, vulnerability-aware, identity-based, and hunt-friendly. VLANs and firewall rules can’t keep pace with modern environments, but software-defined policy can.
The lesson here is simple: Resilience improves not when environments get simpler, but when control becomes more precise. Precision is more important than simplicity.
Prevention, response, and recovery
Today, cyber risk reduction and cyber resilience include prevention, response, and recovery (Figure 4).
Prevention
- Prevention reduces risk by implementing proactive security controls that limit attack surfaces and disrupt adversaries before they gain a foothold.
- Reduces risk by identifying and addressing vulnerabilities before they’re exploited
- Limits attacker movement through Zero Trust and microsegmentation strategies
- Strengthens employee awareness to minimize human error
Response
- Reponse enables the rapid detection and containment of threats, minimizing business impact through automated defenses and adaptive security strategies.
- Enables rapid detection and containment of threats to minimize impact
- Maintains business operations even during an active attack
- Improves cross-team coordination for faster decision-making under pressure
Recovery
- Recovery provides resilient systems that ensure business continuity by maintaining operational integrity, enabling swift restoration of critical services after an incident.
- Restores critical systems and data quickly to reduce downtime
- Preserves customer trust and brand reputation
- Supports long-term adaptability by learning from incidents
Cyber resilience is more than just preventing cyberattacks. It’s about continuing to operate through them and recover quickly when they occur.
Action plan
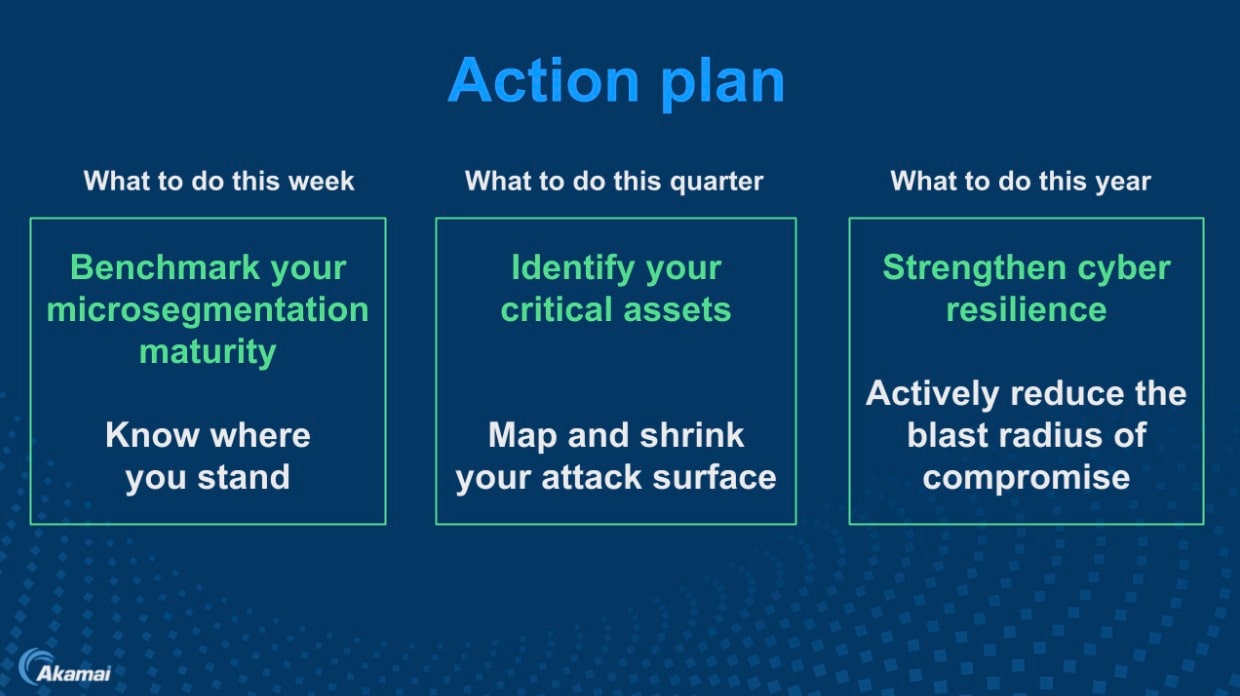
Good news: Cyber resilience, microsegmentation, and achieving Zero Trust don’t require a multi-year transformation. Your action plan should include steps to take this week, this quarter, and this year (Figure 5).
This week: Identify your critical assets and understand who can talk to them.
This quarter: Benchmark microsegmentation maturity and shrink your attack surface.
This year: Enforce least-privilege east-west access and actively reduce the blast radius.
Every step makes the next incident smaller, quieter, and easier to recover from.
Resilient organizations deliberately absorb rather than eliminate risk. You don’t need perfection. The goal isn’t to stop breaches — it’s to make them survivable.
Microsegmentation and Zero Trust: The future of cyber resilience
The strategic takeaway is a simple but hard truth: Microsegmentation and Zero Trust, like M&A, are not just growth and change events, but also risk transfer events. The faster you integrate, the faster you inherit someone else’s attack surface. Control determines whether that risk is absorbed or amplified.
When Zero Trust is enforced at the workload level, organizations integrate faster without increasing systemic exposure. The future of cyber resilience isn’t just about stopping attackers at the door — it’s about ensuring that they never get far enough inside to matter.
Tags