Executive summary
Akamai researchers have found vulnerabilities within three popular servers that implement the MCP standard.
CVE-2025-66335 is a Structured Query Language (SQL) injection vulnerability in Apache Doris MCP. We also found vulnerabilities in Apache Pinot MCP and Alibaba RDS MCP projects.
The issues we found are common vulnerability classes of unsanitized input on SQL queries, missing authentication, and unauthenticated data exposure — each demonstrating a different way that insufficient back-end security validation can be exploited in MCP servers.
In this blog post, we provide technical details of the vulnerabilities, and recommend mitigations for securing your network from similar attack vectors.
The full research, along with the tool used to find these vulnerabilities, will be presented at x33fcon in June 2026.
Introduction
Model Context Protocol (MCP) servers entered our lives recently but drastically improved the capabilities of AI models. (For an examination of the inner works of MCP, read our previous blog post.)
If you've been paying attention, you know the security issues involved with giving AI models access to external applications. MCP servers sit at the center of that approach, and researchers quickly found ways to exploit those servers: tool description poisoning, cross-server context injection, and supply chain attacks on platforms that host them.
This blog post addresses a different aspect of MCP security: The flexibility the protocol gives developers when implementing back-end communication. The protocol deliberately leaves back-end implementation decisions to the developers; for example, decisions about how clients authenticate, how credentials are stored and used, and what privileges the server holds when talking to its back end are all decided during development time, not by the protocol specification.
This flexibility leads to a very different implementation for each security feature on each server. And when a server is sitting between an AI agent and a production database or cloud service, those implementation choices can have serious consequences for organizations.
Evaluating MCP servers at scale
Our goal was to evaluate the security posture of the approximately 300 official MCP servers with regard to their back-end communication implementation. We reviewed how they implemented authentication, authorization, tool capabilities, and how they invoke commands on back-end instances.
To do this, we developed an automated, AI-supported tool to replicate, analyze, and identify vulnerabilities across the entire server network. This analysis found vulnerabilities in MCP servers of three widely adopted projects:
Apache Pinot (6,000 stars)
Apache Doris (15,000 stars)
Alibaba RDS
This showcases a common theme in the current way MCPs are being developed: There is missing or faulty security validation between the MCP server and its back end.
CVE-2025-66335 — SQL injection in Apache Doris MCP
Apache Doris is a high-speed database system designed to quickly analyze large amounts of data, often used for dashboards, reports, and real-time analytics.
Apache Doris MCP server allows AI agents to communicate and perform operations on a deployed Doris instance, like performing SQL queries or retrieving table and schema metadata.
Security-wise, the Apache Doris MCP integration includes a custom Security Manager that is responsible for authenticating users, constructing their security context, and validating every query before execution. Every time a “user” attempts to connect to the MCP server their JSON Web Token is being verified.
After successful authentication, the server creates a SecurityContext object that assigns the user’s clearance level (Public/Internal/Confidential/Secret) and attaches validator modules based on default rules or an external configuration file.
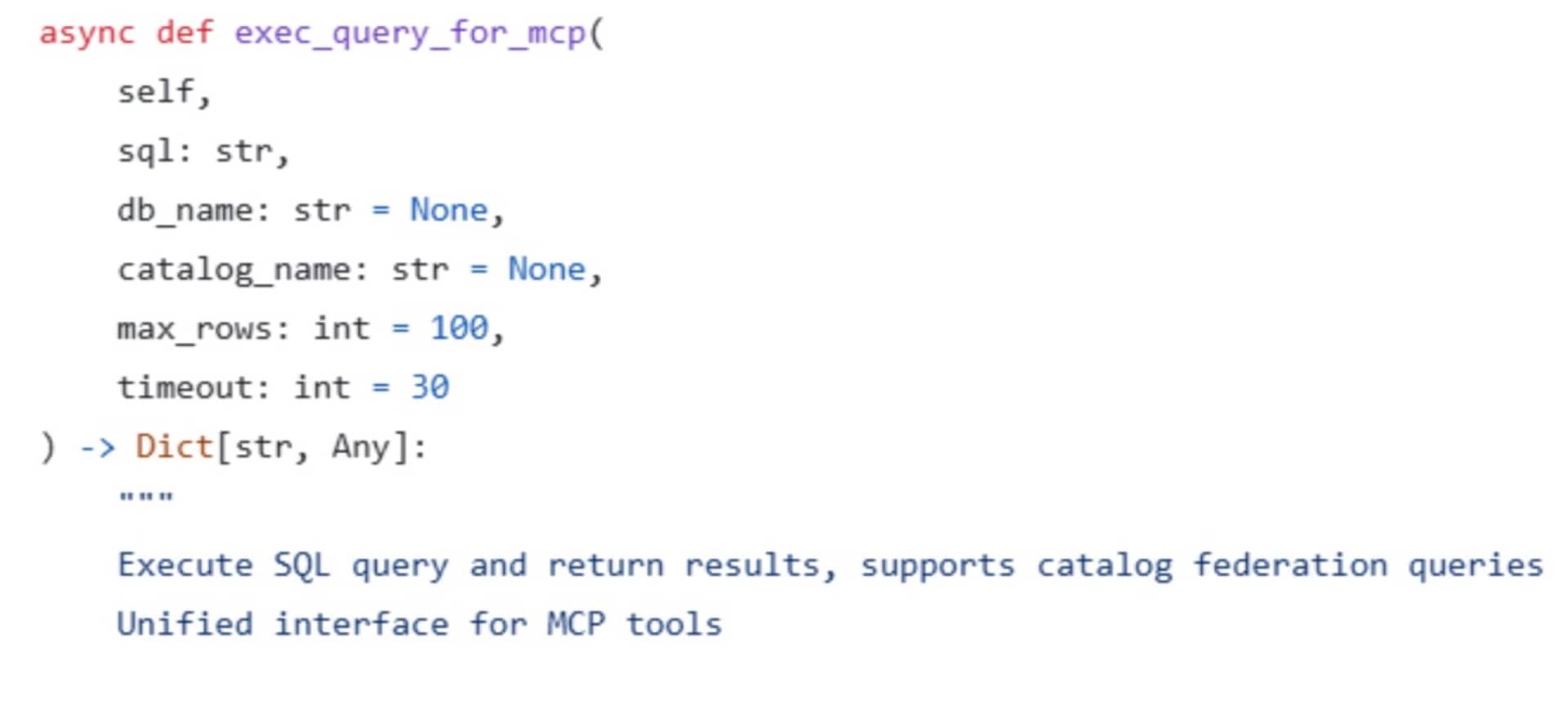
When an MCP tool is invoked, the server calls an inner “exec_query” function that takes five parameters: query, db_name, catalog_name, max_rows, and timeouts.
Despite this layered validation (the clearance level and query), one parameter slips through: The db_name parameter is not being validated or sanitized. Therefore, an attacker can invoke the “exec_query” function with a malicious db_name parameter containing: semicolons, comments, or even full SQL statements. This attacker-controlled parameter is then prepended to the final SQL query string.
The issue is amplified by the fact that the SQL validator only checks the first portion of the query and disregards the rest:
async def validate(self, sql: str, auth_context: AuthContext) -> ValidationResult:
# If security check is disabled, always return valid
if not self.enable_security_check:
self.logger.debug("SQL security check is disabled, allowing all queries")
return ValidationResult(is_valid=True)
try:
# Parse SQL statement
parsed = sqlparse.parse(sql)[0]As a result, any attacker that gains access to a client connected to the Doris MCP server can execute arbitrary commands on the victim’s Apache Doris instance.
Authentication validation bypass in Apache Pinot MCP
Apache Pinot is a real-time analytics database designed to deliver extremely fast queries on large, constantly updating data streams, such as user events, metrics, and logs.
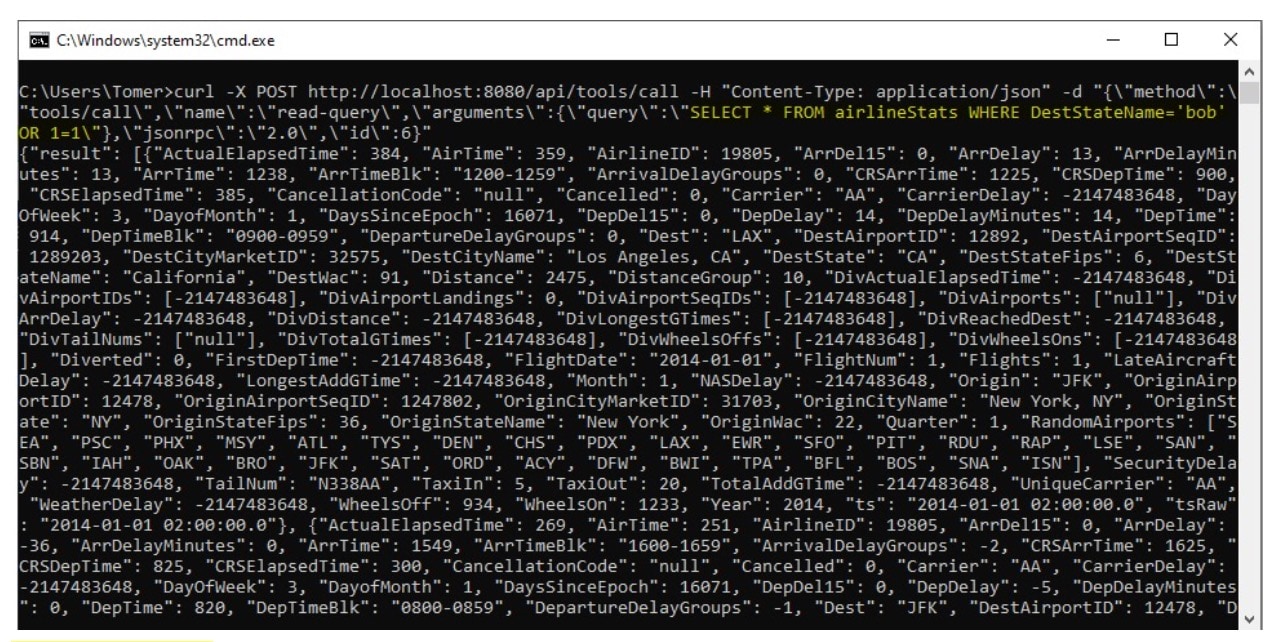
StarTree’s MCP integration for Pinot before v2.0.0 allowed users to run queries directly from their AI agent against their Pinot instance. The project implemented a custom HTTP transport layer. When HTTP transport is enabled, the MCP server binds to 0.0.0.0:8080, which is not inherently problematic — however, it exposes every vulnerability to any remote attacker that can reach the interface.
class ServerConfig:
"""Configuration container for MCP server transport settings"""
transport: str = "both" # "stdio", "http", or "both"
host: str = "0.0.0.0"
port: int = 8080
ssl_keyfile: str | None = None
ssl_certfile: str | None = None
endpoint: str = "/sse"Normally, when an MCP agent is allowing the use of HTTP as the transport layer, it will also implement an authentication mechanism to safeguard its exposed tools.
Anyone who is able to reach that endpoint can invoke MCP tools exposed by the server, including those that allow direct SQL execution.
async def app(scope, receive, send):
if scope["type"] == "http":
path = scope["path"]
method = scope["method"]
if path == server_config.endpoint and method == "GET":
# Handle SSE connection
async with transport.connect_sse(scope, receive, send) as streams:
read_stream, write_stream = streams
try:
await server.run(
read_stream,
write_stream,
InitializationOptions(
server_name="pinot_mcp",
server_version="0.1.0",
capabilities=server.get_capabilities(
notification_options=NotificationOptions(),
experimental_capabilities={},
),
),
)
except Exception as e:
logger.error(f"Error in SSE connection: {e}")
raise
elif path == server_config.endpoint and method == "POST":
# Handle POST messages
await transport.handle_post_message(scope, receive, send)
elif path == "/api/tools/call" and method == "POST":
# Simple REST API endpoint for direct tool calls
await handle_rest_api_call(scope, receive, send, server)The server does attempt to validate SQL queries before execution. However, the validator only ensures that the query string begins with "SELECT", without performing any additional checks on content, structure, or intent. This means an attacker can issue any SELECT-based query targeting any table.
In environments where the MCP endpoint is reachable externally, this behavior allows unauthenticated attackers to execute queries against the Pinot instance, which can allow a full remote takeover of the database.
StarTree added OAuth as an authentication option when using HTTP. Enabling this option lowers the severity of the SQL injection vulnerability that is still present in the code.
Information disclosure in Alibaba RDS MCP server
Alibaba RDS is a database management service that handles administrative tasks, such as installing, running, and configuring SQL engines like MySQL and PostgreSQL, for IT admins. The Alibaba RDS MCP server is configurable, and includes several modular MCP components. Although most of them rely on Alibaba’s own MCP implementation, the retrieval-augmented generation (RAG) MCP within the server is implemented using FastMCP, and it listens like the others on 0.0.0.0:8006.
mcp = FastMCP(
name="MyBase Table Struct Tool",
host="0.0.0.0",
port=8006,
description="根据用户的查询返回对应的表结构信息。",
sse_path='/sse'
)The server exposes a single tool, get_table_struct, which performs a vector-based similarity search over a stored “table_struct” index. This is part of a RAG workflow: User input is embedded into a vector, and the system retrieves the most semantically similar documents.
@mcp.tool()
async def get_table_struct(query: str, topk: int=10) -> str:
res = ""
vectorestore = vectorestores.load_vectorstore_by_name("table_struct")
if vectorestore is not None:
docs = vectorestore.similarity_search(query, k=topk)
res = "\n".join(doc.page_content for doc in docs)
return resThis means that the tool can be invoked without authentication. Any client able to reach the MCP endpoint can issue requests to the server without any query validation.
The vector index may contain table names, schema definitions, or other potentially sensitive metadata, and unauthenticated attackers can exfiltrate this data with little or no effort.
Alibaba has categorized this issue as “not applicable” for a fix and chose to leave it in their codebase. We reported this inaction to the CERT Coordination Center (CERT/CC) to ensure global coordinated disclosure and we are waiting for their response.
Affected versions
Apache Doris MCP — v0.6 and previous
Pinot MCP — v1.1.0 and previous
All versions of Alibaba RDS MCP
Lessons learned
When we began this project, we believed there would be a baseline of security that all servers would have. To our surprise, the MCP specification leaves a lot of flexibility to developers, which creates a wide variation in how MCPs are implemented behind the scenes.
Even though there are several security guidance resources available, vulnerabilities like SQL injection, missing authentication, and insufficient query validation are still showing up. This means that more attention should be given not just to the specification but also to the best security practices guides when developing secure MCP servers.
Conclusion
As MCP adoption grows and more servers are deployed against production databases and cloud services, these gaps will become high-value targets for attackers and we expect more of these issues to surface.
The three servers we highlighted in this post are representative samples of a broader problem: missing or faulty security validation between the MCP server and its back end. Although the OWASP GenAI Security Project has published a practical guide for secure MCP server development, adoption of these practices clearly lags behind the pace of development.
At minimum, servers should enforce authentication at the transport layer, validate all parameters on the server side, and apply least-privilege access to back-end systems.
Disclosure timeline
09/30/2025 — We contacted StarTree.
10/14/2025 — Pinot MCP added authentication that lowers the severity of the vulnerability.
11/17/2025 — We contacted Alibaba.
11/17/2025 — We contacted MITRE regarding Pinot MCP.
11/25/2025 — Alibaba decided not to patch the vulnerability in RDS MCP.
11/27/2025 — Apache was contacted about the vulnerability in Doris MCP.
12/30/2025 — Apache issued a patch for Doris MCP.
01/07/2026 — CVE-2025-66335 was assigned for the Doris MCP vulnerability.
05/04/2026 — An issue was opened in MCP Pinot github repository for the vulnerabilities.
Tags