The Adaptive Security Engine — A Quantum Leap Forward for Application and API Protection

At Akamai, our mission is to make application and API security highly effective and easy. As part of that effort, we are excited to announce the Adaptive Security Engine -- a new core technology powering Akamai's application and API protection offerings, designed to enable a hands-off approach to protecting web applications and APIs with the highest degree of confidence.
Our North Star while architecting the new engine was to give customers:
Strong, high-quality security outcomes
High confidence in protecting applications and APIs without gating app-dev teams and impacting legitimate users
A high degree of available configuration and automation flexibility
A low- to no-touch operational experience for protecting entire web application and API estates -- at scale
Although the above is achievable today, our newest technology is designed to take security outcomes to the next level -- a quantum leap in delivering the best defense while simultaneously reducing operational friction. At Akamai, protecting apps and APIs is what we do best -- as evidenced by our market-leading position and validated by the customers we successfully serve -- and this passion has continued to accelerate our journey to breakthrough ideas.
Let's dive into the latest technologies behind the Adaptive Security Engine and how they work together to optimize protections and drive out complexity for our customers.
Adaptive threat detections
Supreme coverage and accuracy with the ability to adapt automatically to new threats
Akamai's unparalleled visibility into malicious activity across more than 1.3B daily client interactions across the internet gives us unique insight into attackers armed with new tactics, tools, and skills. The intelligence derived from this insight allows us to understand the different risk profiles of incoming requests attempting to hit your applications and APIs.
We've created a new multidimensional threat scoring model that combines this platform intelligence with data/metadata from each request. We then action this data with decision-making logic designed to accurately identify real attacks. Adaptive detections are especially effective in identifying highly targeted, evasive, and stealthy attacks since sophisticated attackers invest more effort and reconnaissance to uncover vulnerable entry points. As attackers scan for vulnerabilities and misconfigurations, we collect and build correlating evidence about their tactics. This not only makes them immediately identifiable, but it leaves behind a historical fingerprint of the types of activities being undertaken should they return later. The harder an attacker tries, the more aggressive our protections get.
In addition to the actual payload and its location within the request, examples of other attack dimensions evaluated for each client include:
History of reconnaissance or actual attacks against the protected app/API or others on the Akamai platform
Any signs of malicious automation and attack tooling
Correlation to known sources of attack traffic
The underlying detection engine was fully re-calibrated and enhanced with two new technologies: Smart Detect, which tokenizes the input into a fingerprint for highly accurate detection; and Smart Sniff, which detects the right content-type of the request body to prevent content manipulation and bypass.
Adaptive detections are automatically updated by Akamai's threat research to ensure that you are using the latest and strongest protections available. We leverage our expansive infrastructure and systems to passively run all new detections -- across the entire Akamai production traffic -- and analyze results using machine learning (ML) models for the highest accuracy. This gives you the confidence that automated protections are not just lab-tested against synthetic traffic, but are battle-tested against real-world conditions.
Self-tuning
Yes, we are declaring war against any and all points of friction in application and API protection
The sheer number of alerts that continue to overwhelm security teams make it virtually impossible for analysts to assess and tune every policy. The goal of self-tuning is to take this problem head-on and alleviate security professionals from manual tuning, which can lead to outdated policies, human error, and alert fatigue.
While the new Adaptive Security Engine has been shown to dramatically lower false positives out of the box, it may not lower the number to zero for every application (nor do we claim it will). Self-tuning will, however, move this outcome closer to reality by applying ML, statistical models, and heuristics across all triggers for each of your security policies to accurately differentiate between real attacks and end-user traffic misidentified as attacks. Most notably, it is not a generic platform-wide check that is applied only during initial onboarding, but a continuous process performed 24/7/365, for each of your individual policies without the need for any end-user configuration or intervention.
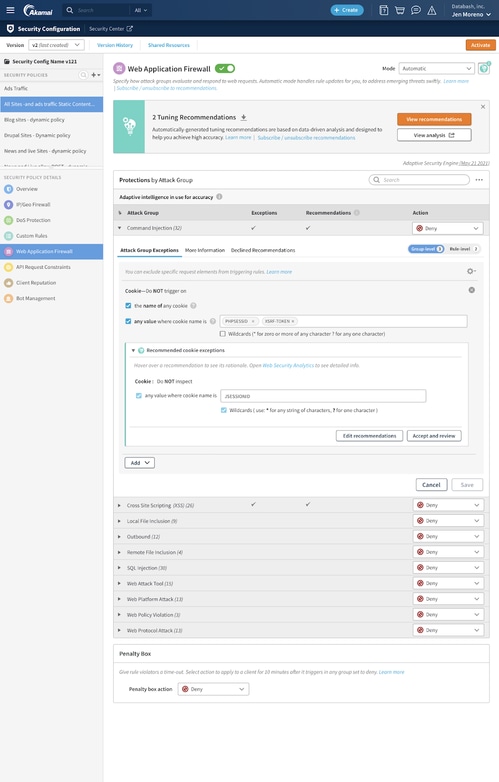
Figure: Adaptive Security Engine with Self-Tuning
Self-tuning was purposely built to be frictionless and simple. You can opt to receive email alerts when new tuning recommendations are available; then, you can easily review and accept recommendations with one-click via the UI, or automate using AppSec APIs, command-line interface (CLI) or Terraform provider. For greater transparency, a pre-filtered link to Web Security Analytics shows all requests deemed as false positives, and our rationale is provided for each recommendation. While this in itself significantly reduces the operational friction, we won't stop here. We're already planning the next iteration of self-tuning where you'll be able to pre-delegate the "acceptance of recommendations" to Akamai to automatically integrate self-tuning with new detections for a truly zero-touch approach to application and API security.
Configuration and automation flexibility
However you want to configure and automate: We have a tool for that!
Adaptive Security Engine has a happy path that is good for a vast majority of customers who want the most balanced experience and security outcome. But if you like to be hands-on with things, Adaptive Security Engine offers an expert mode level of flexibility to run simulations with detection logic; modify debug header behavior and request inspection size; and have a complex set-up of exceptions and conditions for specific policies, hostnames, paths, etc.
Security and DevOps teams can also operationalize security by integrating calls to Akamai APIs using the CLI, Akamai Terraform, or scripts in your CI/CD automation pipeline. This can not only enable rapid onboard applications, but also uniform management of security policies across large application portfolios, centralize security enforcement across hybrid and multi-cloud infrastructures, and improve collaboration between DevOps and security teams in a GitOps workflow for optimal coverage. Configuration and automation flexibility ensure that powerful security never hinders development velocity.
It's time for a new generation of security
To successfully reduce security gaps and mitigate the biggest risks, you need application and API security that not only identifies and stops the most sophisticated attacks, but is easy to use and maintain. Let's face it: Your security teams don't have the time to manually investigate every security trigger or tune every policy. At Akamai, we understand that complex security products and operational friction lead to risk; that's why the new Adaptive Security Engine is designed to intelligently analyze all threats as they arrive in real time, provide security analysts with valuable inputs for far easier decision-making, and reduce false positives in both attack detection and traffic noise.
It's simple. Security teams today need to automate defenses to better respond to threats across the enterprise without a human having to do that work, while also confirming that the security controls they do have operate with maximum efficiency and flexibility. Threat actors are automating, scaling, and commoditizing their attacks -- automating your web application and API defenses in parallel will improve your ability to manage cyberthreats at pace.
To learn more about the Adaptive Security Engine and Akamai's web application and API security solutions, contact your Akamai representative.



