Akamai Cloud (Linode) is a registered Hashicorp Terraform provider. Akamai provides Terraform template resources as infrastructure as code (IaC) to create, modify, and delete Linodes Block Storage volumes. The upcoming changes in the provider code make enabled block storage disk encryption the default.
What is happening?
Starting in Akamai Cloud provider version 3.9, Akamai will make block disk encryption the default option. When you create a new block volume on Akamai Cloud, it will now be encrypted by default and secure your data at rest. This will help you increase your security posture by protecting against data leaks. This does not affect existing volumes.
Apply the updated configuration in 9 easy steps
Use the following nine Terraform steps to create a block volume and apply the updated configuration.
Step 1: Install Terraform (Mac OS). Installation may vary depending on your operating system.
% brew tap hashicorp/tap
% brew install hashicorp/tap/terraform
Step 2: Confirm installation.
% terraform -version
Step 3: In Cloud Manager, navigate to Profile → API Tokens → Create A Personal Access Token (or use existing API token).
Step 4: Set Linode API token as Terraform variable.
% vi terraform.tfvars
linode_token = "12345..."
Step 5: Create a configuration file called main.tf file to define your volume. Note the provider source and version. Version 3.9 will introduce block disk encryption enabled by default.
% vi main.tf
terraform {
required_providers {
linode = {
source = "linode/linode"
version = "~> 3.9"
}
}
}
provider "linode" {
token = var.linode_token
}
variable "linode_token" {
type = string
description = "Linode API Token"
}
resource "linode_volume" "my_volume" {
label = "my-volume"
size = 20
region = "us-east"
encryption = "enabled"
}
Please note: The change means that if the line encryption = “enabled” is missing from configuration, the volume will be encrypted by default.
Step 6: Initialize your Terraform project.
% terraform init
Step 7: Plan the infrastructure to tell Terraform what you want to provision.
% terraform plan
Step 8: Apply the configuration to build your volume.
% terraform apply
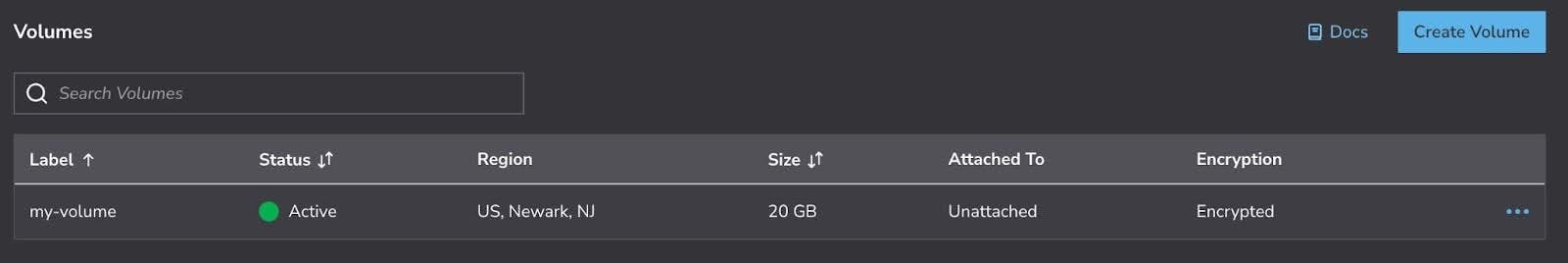
Step 9: In Cloud Manager, you will see your new encrypted block storage volume (Figure 1).
How to disable and reapply
If you want to disable volume encryption (not recommended), modify the encryption setting in your main.tf file.
From:
encryption = "enable"
To:
encryption = "disabled"
To reapply the configuration, run the following command.
% terraform apply
Please note: This will destroy the existing encrypted volume and create a new unencrypted volume.
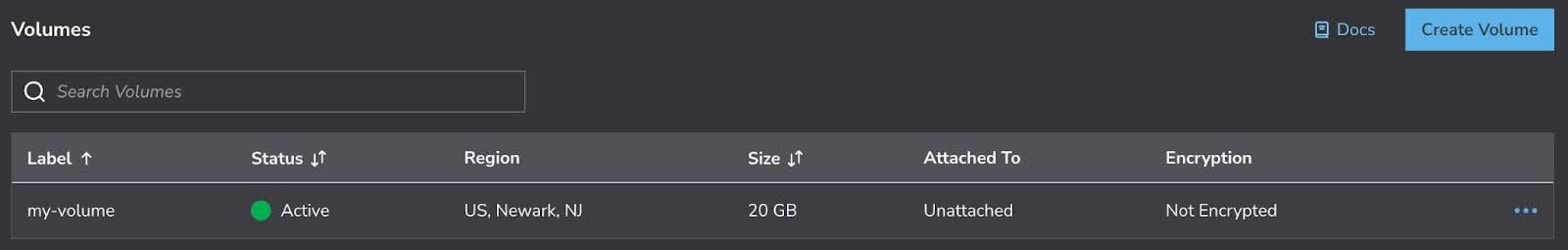
In Cloud Manager, you will see your new unencrypted block storage volume (Figure 2).
Alternatively, you could use a previous provider version (prior to version 3.9).
Summary
In this blog post, we have shared the update that makes block storage disk encryption the default in Akamai Cloud’s Terraform provider code, and we’ve provided instructions on how to use the Terraform code.
If you have any questions about block storage disk encryption by default, please open a support ticket.
Tags