Editorial and additional commentary by Piero Vera
Executive summary
Since the start of the 2026 conflict in the Middle East on February 28, 2026, Akamai has observed a 245% increase in cybercrime targeting critical businesses and institutions in North America, Europe, and parts of Asia-Pacific.
Handala, a hacktivist group that is reported to have links to Iran’s intelligence agencies, has claimed responsibility for a data-wiping attack against Stryker, a global medical technology company headquartered in Kalamazoo, Michigan.
Geopolitically motivated hacktivists are using proxy services in countries like Russia and China as a source for billions of designed-for-abuse connection attempts.
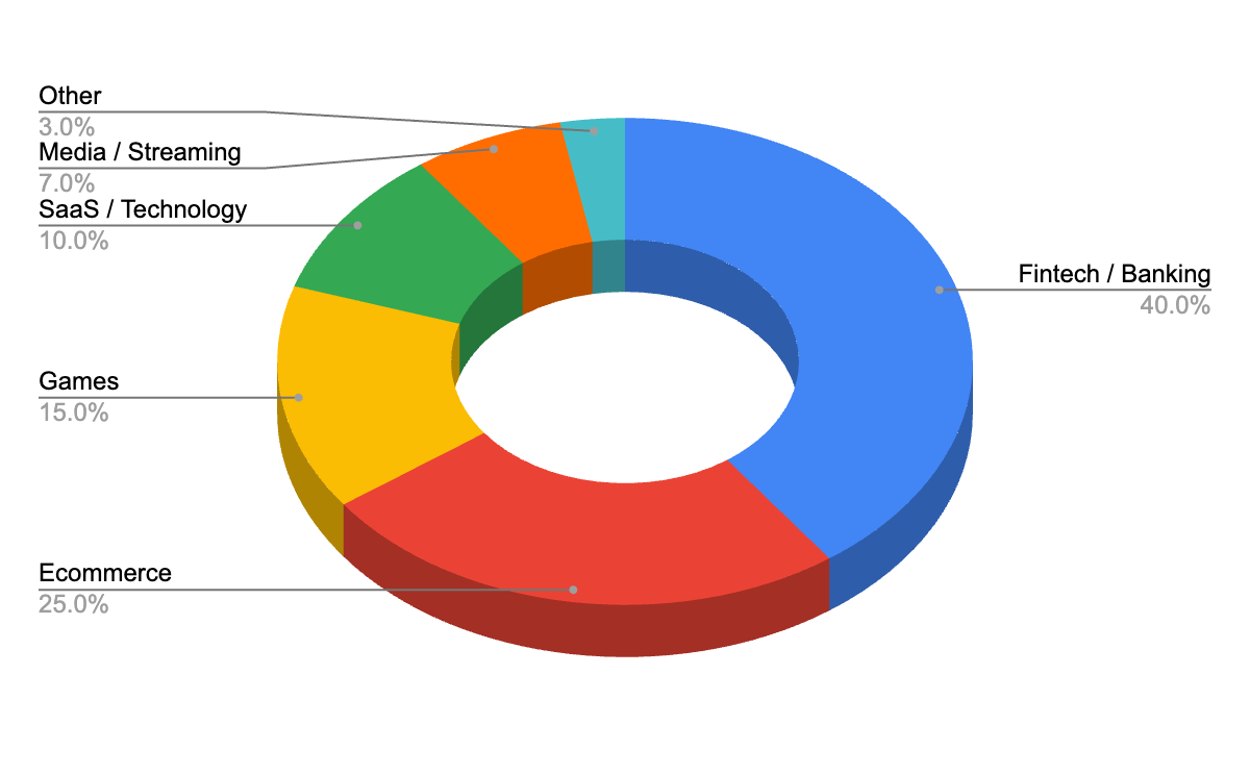
Banking and financial services, ecommerce, and video games alone account for 80% of the destinations for malicious traffic. Banking and financial services and ecommerce together account for more than 50% of the target destinations.
Akamai customers have successfully blocked billions of packets of unwanted and potentially malicious traffic by using the powerful and easy-to-use capabilities of Akamai Prolexic Network Cloud Firewall, which help them enforce a positive security posture at the edge of their networks.
As the volatile situation continues, customers are advised to remain vigilant and adopt a proactive security posture across their entire network surface to avoid potential downtime or performance degradation.
One of the most defining characteristics of modern geopolitical conflicts and warfare is that it is no longer confined to the physical realm. Often, the most devastating attacks in a conflict today focus on the digital realm. It makes sense: In a digital-first world, cyberattacks can very effectively wreak havoc on businesses, critical public infrastructure, and public confidence.
Geopolitics — The underlying catalyst for cyberthreats
Geopolitical ideology and motivation have often been catalysts for cybercrime, including attempts by nation-state–sponsored threat actors to infiltrate or take down the digital infrastructure of victim organizations and institutions.
As the world begins 2026, the global geopolitical theater is in the throes of multiple concurrent and significant conflicts around the world. The Russia-Ukraine war has entered its fourth consecutive year. Several cyber espionage campaigns are regularly traced back to threat actors based in China, Iran, Pakistan, and North Korea.
And over the past few years, there have been sporadic regional conflicts between India and Pakistan, Thailand and Cambodia, and Pakistan and Afghanistan. Each of these conflicts witnessed an increase in cyberattacks.
The conflict in the Middle East that started on February 28, 2026, has sent rippling effects across travel, hospitality, and energy sectors of the global economy. Even more concerning is the significant increase in cybercrime emanating from nation-state actors and ideologically motivated hacktivists, who might operate from an entirely different part of the planet to orchestrate highly sophisticated attacks.
On March 11, 2026, Handala, a hacktivist group that is alleged to have links with Iran’s intelligence services, claimed to have orchestrated a massive data-wiping attack on Stryker, a global medical technology company. The attack has reportedly wiped away several terabytes of critical data. There have also been sporadic and unconfirmed media reports that Iran could attack the physical offices, as well as the digital infrastructure, of several U.S.-headquartered technology companies, including Google, Amazon, Microsoft, NVIDIA, and others.
Significantly increased threat activity
Since February 28, 2026, Akamai has observed a staggering 245% increase in malicious traffic targeting businesses and institutions operating in North America, Europe, and parts of Asia. The table summarizes some of the more recurrent forms of threat activities that have increased in volume since the conflict began.
Threat activity |
Observed trend |
|---|---|
Automated reconnaissance traffic |
Significant increase (+65%) |
Credential harvesting attempts |
Elevated activity (+45%) |
Infrastructure scanning |
Widespread probing of exposed services (+52%) |
Botnet-driven discovery traffic |
Large-scale automated scanning (+70%) |
Pre–distributed denial of service (DDoS) reconnaissance |
Increased probing before volumetric attacks (+38%) |
Types of cyberattacks that have increased in frequency and volume since February 28, 2026
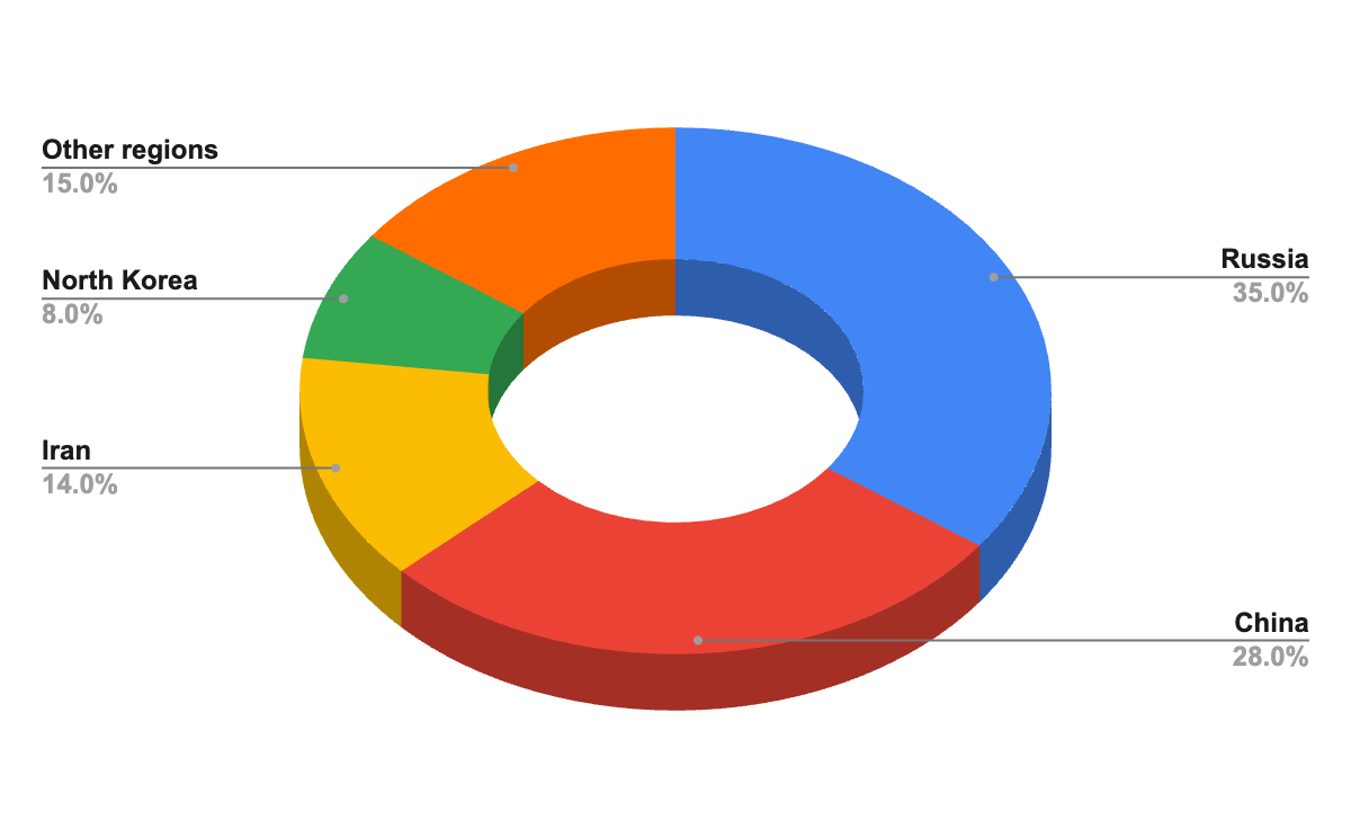
Geographic distribution of the source IPs for malicious traffic
Figure 1 shows the key regions from where malicious traffic was generated by threat actors to saturate or disable the digital infrastructures and applications of customers protected by Prolexic Network Cloud Firewall.
Opportunitistic cybercriminals, geopolitically motivated hacktivists, and potential nation-state threat actors are using proxy services as a source for billions of designed-for-abuse connection attempts.
Considering the rapidly evolving nature of the ongoing geopolitical conflicts across the world, it is critical for businesses, particularly in highly regulated industries like financial services, to proactively fortify their cybersecurity defenses and block malicious traffic at the edge of their network to avoid outages and performance degradations.
The verticals most frequently targeted by malicious traffic
Figure 2 shows some of the key industries that are being persistently targeted by malicious traffic from threat actors each time there is a sudden spike in geopolitical conflicts.
Banking, financial services, and fintech (including payment processing platforms and infrastructure) are the most targeted verticals. Businesses and institutions in these industries are the backbone of any economy, and any disruption to organizations in these verticals would have an outsized impact. Just imagine the scale of the impact if users in the United States were unable to log in to their banking apps or use their credit cards.
If you are an organization that does not conduct business in these conflict-impacted regions or you are a critical public services institution (such as a local hospital or utility company) that does not have legitimate users in these regions, one of the most effective defenses is to stop all attempts originating from these countries. Prolexic Network Cloud Firewall allows geo-based traffic restrictions with a single click of a button.
The invisible shield that protects your edge with one click
Prolexic Network Cloud Firewall is a highly nimble and powerful firewall that sits at the edge of your network, outside all other firewalls and protections. It is your first line of defense against a wide range of cybercrime and zero-day vulnerabilities, and a highly critical tool in the overall toolbox available to network security professionals.
While legacy firewalls operate inside your network or cloud environments, and are often designed to protect a specific part of your network or application from malicious and abusive traffic, Prolexic Network Cloud Firewall enforces security policies and posture at the edge of your network, at a global scale, in real time.
This offloads a significant amount of policy enforcement away from other security systems and allows your network security teams to keep downstream firewalls and security systems up and running.
The power of edge enforcement
Akamai Network Cloud Firewall customers can simply block — with a single click — entire geographies that they do not serve. This eliminates large portions of unwanted traffic instantly.
If you are a financial services institution operating in the United States, for example, it may be safe to assume that you do not have a lot of legitimate users in Iran, Russia, or North Korea. With geo-block rules enforced at the edge, you can protect your digital networks and assets from nearly all malicious traffic originating from these regions. One click and you are done.
With great power comes greater simplicity
At Akamai, we believe that “with great power (of Prolexic Network Cloud Firewall) comes even greater (operational) simplicity.” With Prolexic Network Cloud Firewall, malicious traffic never reaches your origin servers, load balancers, critical APIs, or other foundational elements of your infrastructure, thus preventing resource exhaustion and operational noise — all with a single click.
Prolexic Network Cloud Firewall in action
The following examples illustrate how the volatile geopolitical climate can act as a catalyst for a sudden spike in cybercrime. Occasionally, the crime originates from regions that are not directly or explicitly involved in the conflicts.
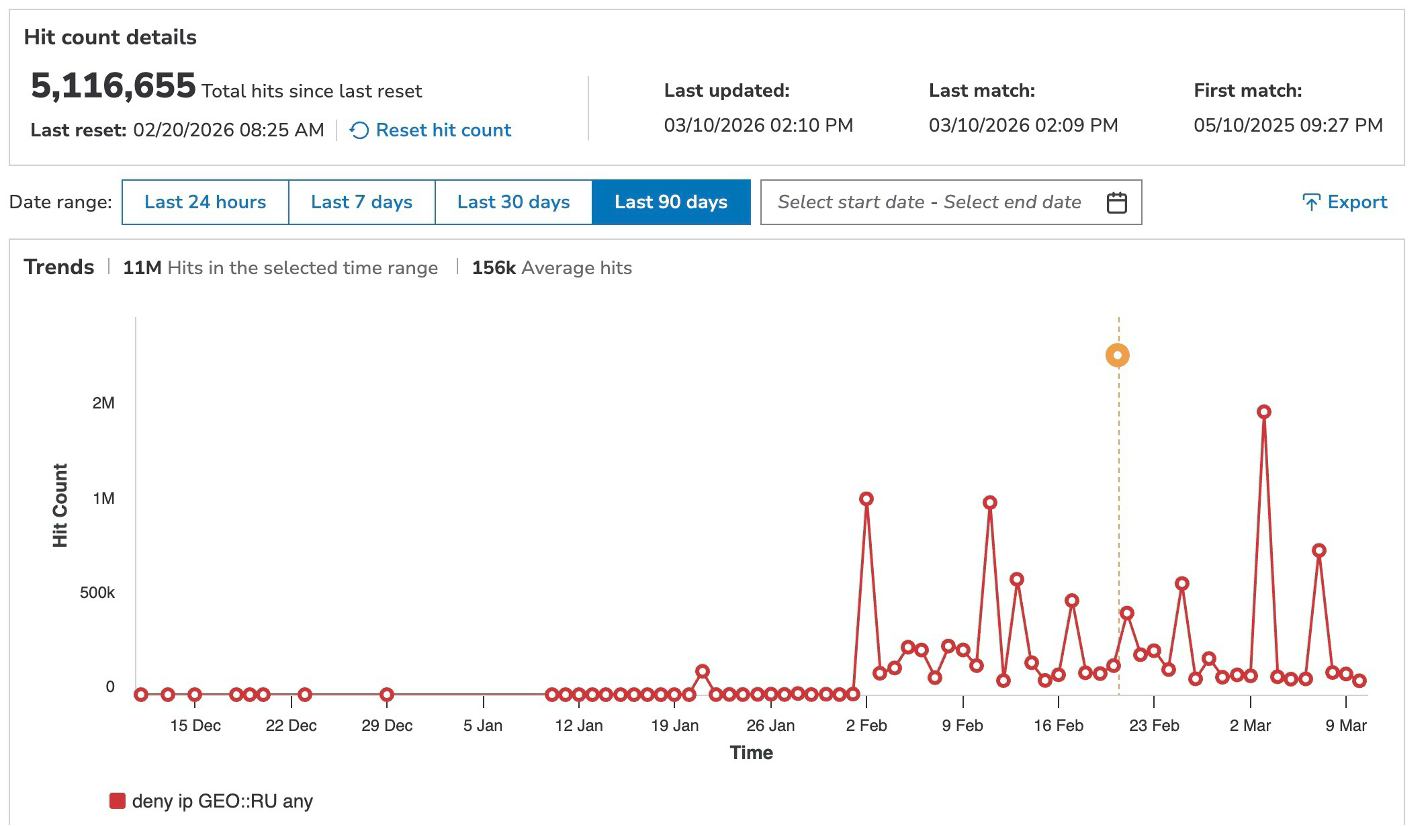
A critical payment infrastructure company in Asia-Pacific blocked 11 million packets from Russia
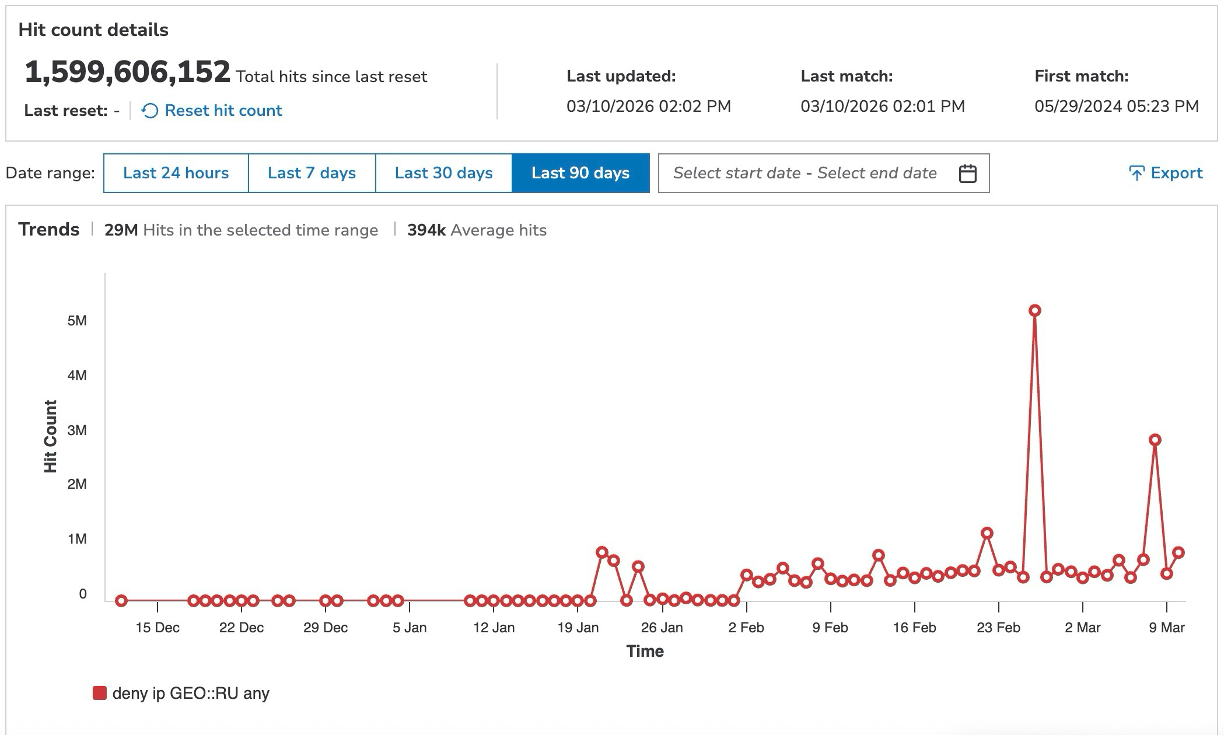
One of the largest and most critical real-time payment processing platforms and infrastructure in the Asia-Pacific region experienced a massive surge in malicious traffic originating from Russia, since the start of the 2026 conflict in the Middle East.
This regional critical financial infrastructure institution does not have any legitimate users in Russia or Central Asia, and has proactively placed Prolexic Network Cloud Firewall rules that block any and all traffic originating from IPs in the regions where it does not operate.
The proactive edge security posture management adopted by the institution successfully blocked more than 3 million hits originating from Russia with just a single rule — [deny ip GEO:: RU any] — in a single day. In fact, more than 65% of the total traffic blocked by this customer since deploying Network Cloud Firewall in their defense stack from 2025 took place in March 2026.
Had this customer not adopted a strict and proactive posture with Prolexic Network Cloud Firewall, and consequently experienced a performance degradation or outright outage, the cascading consequences could have been staggering in scale.
Moreover, as a critical financial infrastructure services institution, any degradation in performance or unavailability would have triggered an audit into compliance mandates of baseline performance and availability of services.
Figure 3 shows the malicious and unusual traffic spikes originating from Russia over 90 days in early 2026 and how Prolexic Network Cloud Firewall helped this customer seamlessly block this unwanted packet traffic with a single click.
A payment processing platform in Europe blocked nearly 1 billion hits from Russia
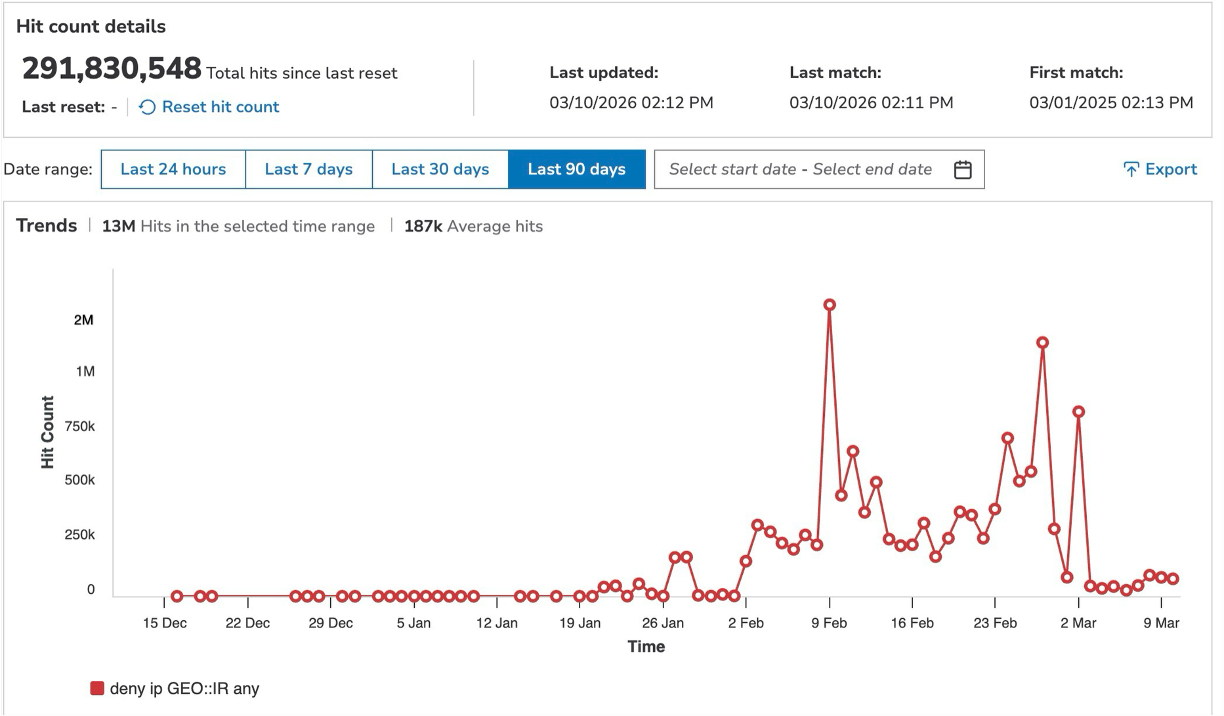
In another instance, a major payment processing platform in Europe experienced a significant spike in malicious traffic from IP sources in Russia over 90 days. Close to one billion packets were denied at the customer’s edge using Prolexic Network Cloud Firewall.
This customer experienced 978 million hits over 90 days, of which 46 million hits were recorded on the Network Cloud Firewall rule — [deny ip GEO:: RU any] — in a single week (Figure 4).
The same customer seamlessly blocked 3 million packets originating from Iran in the weeks leading up to the start of the conflict in the region. The customer had proactively placed an additional rule — [deny ip GEO:: IR any] — to block all traffic and packets originating from Iran.
Unsurprisingly, the number of hits against this Network Cloud Firewall posture precipitously declined since the start of the war in the region and after Iran effectively enforced a near-total internet shut down.
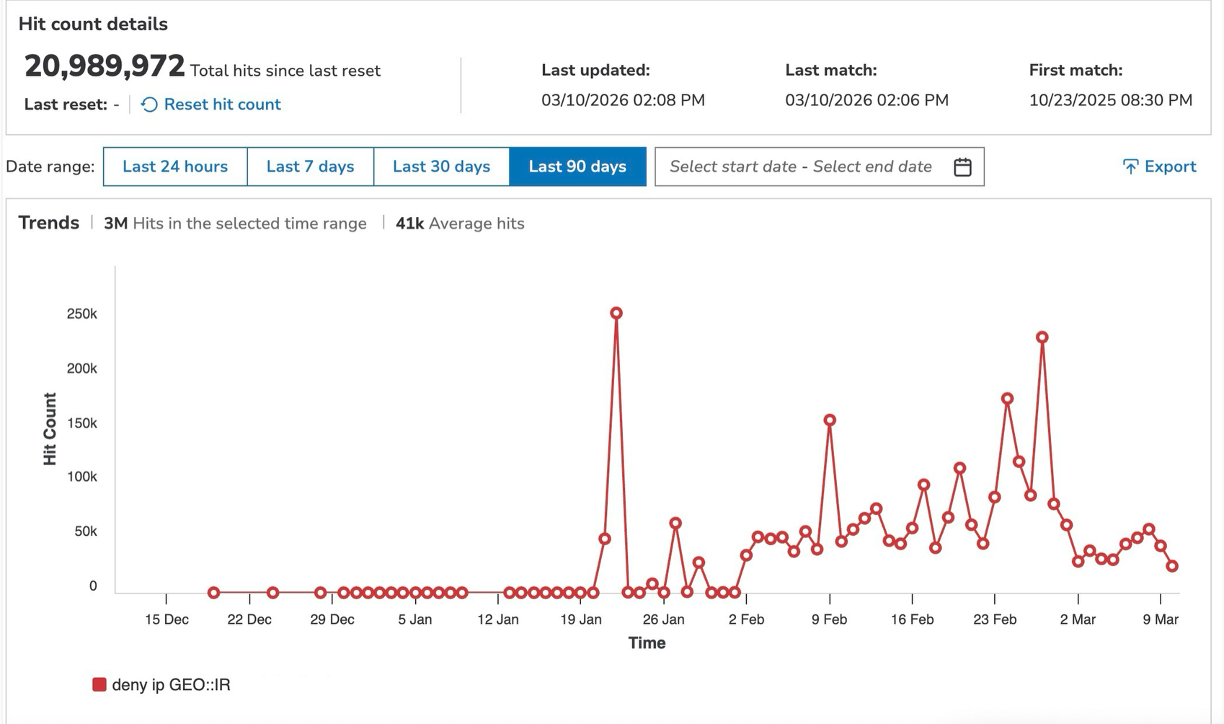
Figure 5 shows the massive and unusual surge in packet traffic originating from Iran that was successfully blocked by Prolexic Network Cloud Firewall at the edge of the customer’s network.
A major U.S. financial services organization blocked 13 million packets from Iran
Similarly, a major U.S. financial services institution experienced an unusual spike in traffic originating from Iran in the weeks leading up to the 2026 conflict. Of the total 13 million hits over 90 days, Prolexic Network Cloud Firewall blocked 10 million packets of traffic from Iran with the [deny ip GEO:: IR any] rule in just a 30-day period.
Figure 6 shows the repeated traffic spikes during this 30-day period.
A global real estate management organization blocked 29 million packets from Russia
These recent attacks aren’t limited to the banking and financial services vertical alone. A global real estate and professional services management organization headquartered in the United States experienced 29 million hits from Russia in the same period — between mid-January to March 2026.
On February 28, the date when the conflict in the Middle East began, the customer blocked more than 5 million malicious packets in a single day with Prolexic Network Cloud Firewall (Figure 7).
These examples illustrate the value of adopting a proactive security posture by deploying highly effective tools like Prolexic Network Cloud Firewall so that your network and application security teams rarely have to scramble in an emergency to block the malicious traffic impacting your origins.
7 recommendations for customers
Take a proactive approach. If your organization does not conduct business in certain geographies, or if it offers a service for which it is unlikely to have legitimate users outside specific regions of the world (e.g., financial services, public utility companies, or healthcare organizations, among others), we highly recommend denying all traffic from those regions with Prolexic Network Cloud Firewall.
Ensure that you have effective systems to enforce proper caching, rate limiting, and IP reputation controls for websites and critical business applications. The enforcement must take place at the edge of your network to optimize your security posture and the performance of your network.
Review critical subnets and IP spaces, and ensure that they have mitigation controls in place.
Deploy Prolexic DDoS security controls in an always-on mitigation posture to reduce the burden on incident responders.
Closely monitor your web application firewall policies with Akamai App & API Protector and your API behaviors with Akamai API Security to protect your critical web applications.
Adopt Akamai Guardicore Segmentation to prevent threat actors from exploiting vulnerabilities through lateral scanning and movement.
Exercise your runbook by validating your emergency plans, contacts, and lockdown policies for critical applications or network assets.
Tags





![This customer experienced 978 million hits over 90 days, of which 46 million hits were recorded on the Network Cloud Firewall rule — [deny ip GEO:: RU any] — in a single week (Figure 4).](/site/en/images/blog/2026/fortify-network-security-emerging-geopolitical-cyberthreats-four.png)