Cyberweek 2020 Attracted Both Online Shoppers and DDoS Attackers
As we close out 2020, it should come as no surprise that Cyberweek (the week of Thanksgiving through Cyber Monday) proved big for DDoS attacks. Threat actors were out in force during this key shopping season, and they shifted their sights toward disrupting digital commerce-related industries.
This makes sense -- 2020 has shown both record busting bps and pps attacks and the most prolific DDoS extortion campaign recorded by Akamai (which is still ongoing). This holiday season is ripe with pent-up online shopping demand, as many consumers still face lockdowns and other restrictions, leading to increased spending and time spent online searching for blowout Black Friday bargains.
Not surprisingly, Cyberweek 2020 saw large increases in both the total number of attacks and the number customers attacked.
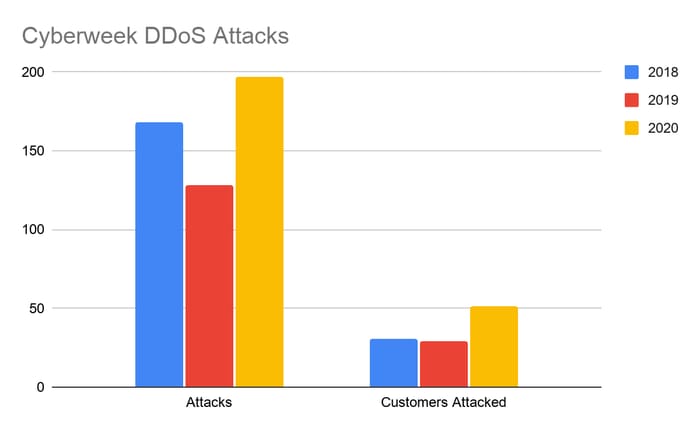
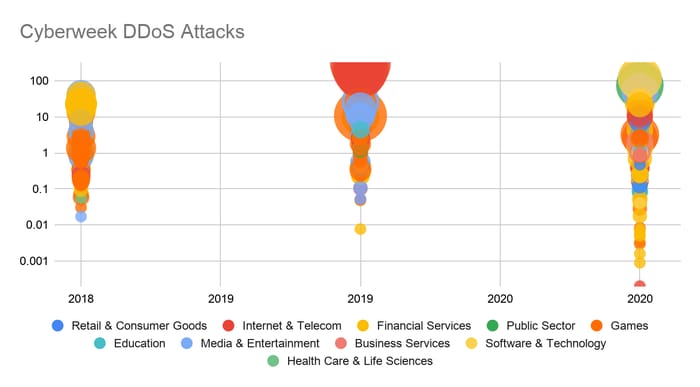
While peak Gbps/Mpps values were down from 2019 highs, we saw 65% more attacks levied against our customers. The number of customers attacked in 2020 was also up 57% as attackers expanded to target a wider variety of industry verticals -- similar to what was witnessed with the latest DDoS extortion campaign and reflective of a broader trend for the year.
For example, we noted a dramatic shift in industry focus from Games customers to Financial Services (up 4x), Business Services (up from 0 attacks in 2019), and Retail and Consumer (up 8x).
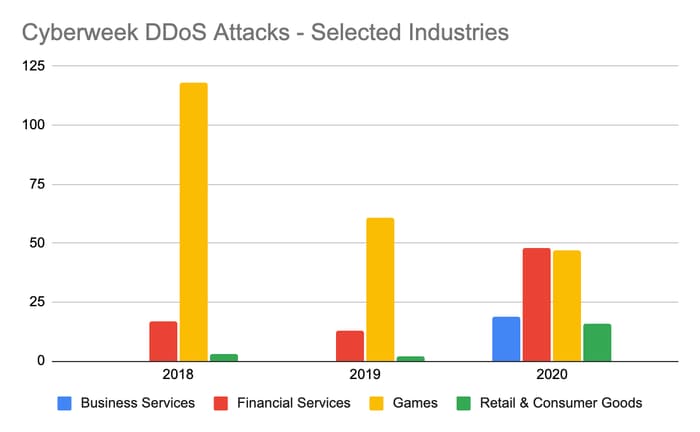
Attacker intent appears to have moved from largely interference in Games (aimed at players gaining a competitive advantage) to digital commerce-related disruption. A targeted campaign against a key Business Services customer netted 19 separate attacks over the week, intended to disrupt the digital commerce supply chain.
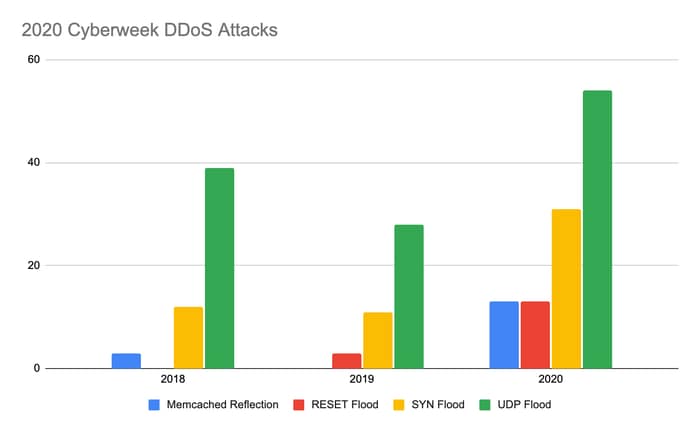
Jumps in UDP Flood, SYN Flood, Memcached, and Reset Flood attacks led the increase in overall attack activity, while most other DDoS vectors remained relatively flat.
Although we didn't see any giant attacks like the 300 Gbps whopper from Cyberweek 2019, attacks over 50 Gbps remained at consistent threat levels year over year.
Throughout 2020, it seems DDoS cybercriminals did not take much of a breather and are unlikely to pump the brakes anytime soon. As we head into 2021, it's important to consider the following to help strengthen defensive postures:
'Tis the season for peace and goodwill, but preparing now during peacetime means you don't have to scramble to deploy DDoS defenses when attacker activity heats back up. The time to secure mitigation controls is now, not after you have been attacked.
Don't assume you're at low risk of DDoS attack because your industry is rarely hit or you've never experienced an attack before. As we've seen time and time again this year, attackers are expanding their horizons and targeting verticals and industries more broadly, leaving anyone with internet-facing assets exposed.
Based on the level of sophistication, persistence, and attacker reconnaissance of customer environments and IP spaces, organizations need to engage providers who are true experts in combating DDoS at scale and helping customers proactively and effectively reduce their attack surface.