DevSecOps is a methodology and cultural approach, not a single tool or product. It combines development, security, and operations practices to integrate automated security controls throughout the software development lifecycle. While DevSecOps relies on tools such as vulnerability scanners and CI/CD security automation, it is primarily a process and organizational model.
DevSecOps is a software development approach that incorporates security measures throughout the entire DevOps process. It emphasizes collaboration and integration between development, operations, and security teams to ensure that security practices are implemented at every stage of the software development lifecycle.
DevSecOps is a software development practice that adds cybersecurity (Sec) to DevOps, which is itself a combination of software development (Dev) and IT operations (Ops). Before DevOps practices became widespread, software development and IT operations teams typically worked in separate stages of the delivery process. Code would move through multiple handoffs — often involving QA, release engineering, and operations — before deployment to production. These traditional handoffs often created silos between teams. As agile software development methodologies accelerated the pace of software code releases, these handoffs between organizations became unmanageable. To solve the problem, DevOps unified the development and deployment processes, along with the respective teams who handled the work.
The difficulty is that security doesn’t disappear just because DevOps has sped up the process of writing and releasing code. If anything, the faster pace of development creates more exposure to security threats targeting applications and infrastructure. The chance that a vulnerability or malicious code will make it into production increases as the delivery process accelerates.
DevSecOps offers a solution. It integrates security measures into each stage of the DevOps software development lifecycle (SDLC) — making security part of the continuous integration/continuous delivery (CI/CD) pipeline. Working with DevSecOps, developers, QA team members, and IT operations staff can attend to security issues as they arise. This model supports a shift left approach, meaning security testing and security checks are introduced earlier in development rather than added at the end. This is an improvement over the previous practice of introducing security steps late in the SDLC.
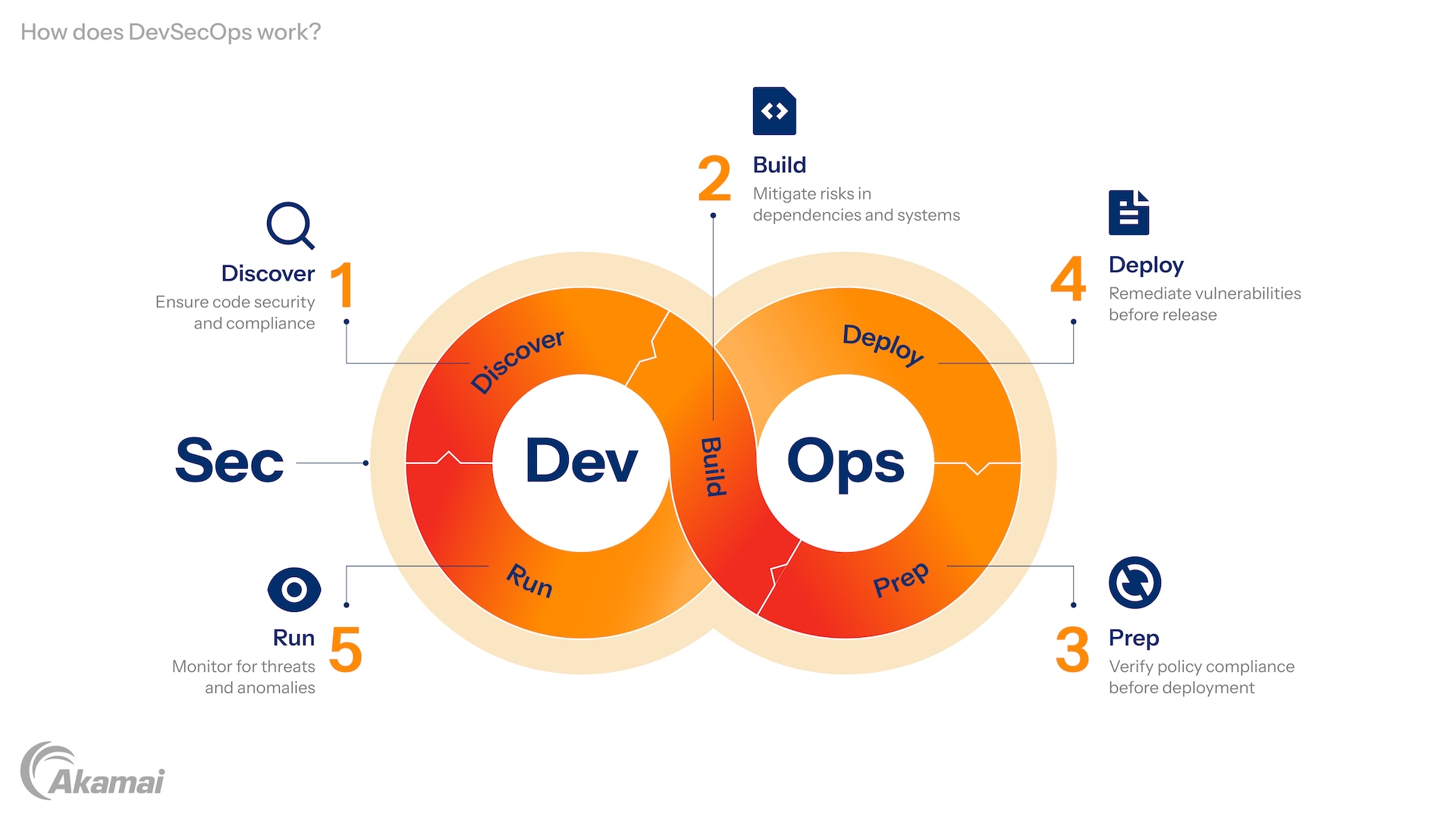
How does DevSecOps work?
To understand how DevSecOps works, it’s first necessary to grasp how the DevOps workflow operates. There are, of course, many ways to implement DevOps. It’s an approach to software development, not a standard or a product. Indeed, DevOps is often depicted as an infinite loop that incorporates a wide variety of tools and DevOps practices. DevOps pipelines can vary widely by organization and tooling. Many pipelines include stages such as planning, coding, building, testing, deploying, and monitoring. DevSecOps embeds security checks and controls throughout these stages:
- Discover: In coding, DevSecOps works to ensure that open source software components pulled from external repositories don’t contain known security vulnerabilities or include malware, both of which are common risks in today’s software supply chain. Teams may implement security scanning, code reviews, and threat modeling during this phase. QA testers may also run security tests on the source code as well as on application programming interfaces (APIs) connected to the web application or service being built.
- Build: At the build stage, DevSecOps applies controls that mitigate risks related to operating systems, application dependencies, and runtime environments. This includes scanning container images, validating configurations for Kubernetes clusters, and ensuring that cloud native workloads are hardened before release. Automated testing tools assess code integrity, dependency risks, and infrastructure configurations across multi-cloud environments.
- Prep: Before the Ops team deploys the code, DevSecOps takes steps to ensure that the application follows the organization’s security policies and access control requirements. For example, if policy dictates that data must be encrypted in transit, DevSecOps should include a check to make sure this is occurring.
- Deploy: Vulnerabilities or security-related misconfigurations need to be identified and remediated before deployment. Infrastructure-as-code templates, cloud permissions, and orchestration platforms like Kubernetes are reviewed to reduce exposure to security threats.
- Run: When the application is in production, DevSecOps needs to apply monitoring to catch threat signatures as well as anomalies that indicate that an attack is underway.
DevOps vs. DevSecOps
It’s not entirely accurate to say that DevSecOps is simply DevOps with security measures thrown in. A DevOps process, on its own, almost always contains some security steps. The issue is how and where they are placed in the DevOps workflow. In some organizations, security has historically been treated as a separate phase late in the development lifecycle. DevSecOps addresses this by integrating security practices and automation throughout the DevOps workflow rather than treating security as a separate gate.
The implication of DevSecOps is that it’s DevOps, with security added as an integrated, collaborative part of the entire workflow. Security exists at each stage in the SDLC. It’s not, to borrow a phrase from the old days of coding, “thrown over the wall.” It’s important to note, however, that DevSecOps also implies the use of special tools and automation.
DevSecOps also implies the use of automation to optimize functionality and efficiency while enforcing consistent security standards. Automated policy enforcement, vulnerability scanning, and security validation reduce friction and help eliminate silos between teams.
What are the benefits of DevSecOps?
DevSecOps delivers two interrelated benefits: It speeds up the development of secure software. And the software itself is more secure than it would have been under traditional development workflows. On the first point, security almost always slows down the cycle of developing, testing, and releasing software. If security steps come later in the cycle, the slowdown is all the more pronounced. In the worst case, if security teams detect vulnerabilities or the presence of malicious code after deployment to production, that results in a long, costly, and public remediation process.
Fixing security problems in software was also traditionally a point of friction between developers and security teams. Developers might have an “it’s not my job” attitude about security controls and resent the intrusion and task-switching involved in rewriting insecure code. This dynamic, coupled with security’s tendency to slow things down, often led to security being de-emphasized or ignored outright — a move that negatively affected security posture.
DevSecOps reduces the likelihood of this outcome. With the ability to streamline and automate security in the DevOps CI/CD workflow, DevSecOps makes it possible to execute more security tests and controls on software before it reaches production. The resulting software should be more secure than code produced in the traditional way. In production, DevSecOps enable more rapid patching of vulnerabilities. This will occur if the DevSecOps workflow includes vulnerability scanning, including the ability to identify and patch Common Vulnerabilities and Exposures (CVEs).
Why DevSecOps matters
DevSecOps matters today because of a dangerous confluence of trends in technology. Applications are composed of microservices, APIs, open source components, and containerized workloads orchestrated by Kubernetes. This complexity increases the attack surface.
At the same time, attackers are targeting weaknesses in CI/CD pipelines, software supply chains, and exposed APIs. Organizations cannot afford to treat security as an afterthought.
DevSecOps practices enables organizations to maintain a rapid delivery process while proactively managing security threats. By embedding automated testing, threat modeling, and policy enforcement into the SDLC, organizations can protect their applications without sacrificing speed or innovation.
Application security testing in DevSecOps: Identifying vulnerabilities early
One of the core practices in DevSecOps is application security testing, which focuses on identifying and mitigating vulnerabilities in the code before it reaches production. By conducting regular and automated application security testing, DevSecOps teams can reduce the risk of security incidents happening once the application is live.
Types of application security testing:
- Static application security testing (SAST): Analyzes the application’s source code to find potential vulnerabilities in the development phase.
- Dynamic application security testing (DAST): Tests the running application in real time to find vulnerabilities that might occur during runtime.
- Interactive application security testing (IAST): Combines aspects of both SAST and DAST, providing real-time analysis of the application’s security.
Implementing these testing methodologies in the DevSecOps process helps to create a proactive security posture, enabling continuous protection and reducing the risk of vulnerabilities reaching the production environment. Regular testing reinforces security as a core part of DevSecOps, ensuring applications are built with security in mind from the start.
Frequently Asked Questions
DevOps focuses on collaboration between development and IT operations teams to accelerate software delivery. DevSecOps extends DevOps by integrating security as a shared responsibility across development, security, and operations teams.
In DevSecOps, security controls, automated testing, and threat modeling are embedded throughout the CI/CD pipeline rather than added at the end of the development process.
Shift left in DevSecOps means introducing security testing and security checks earlier in the software development lifecycle. Instead of waiting until deployment or production to evaluate security risks, development teams run automated security scanning, code analysis, and threat modeling during coding and build stages.
This approach reduces remediation costs and improves overall software quality.
DevSecOps strengthens software supply chain security by scanning open source software components, container images, and third-party dependencies for vulnerabilities. Automated security scanning tools analyze code repositories and build artifacts to detect Common Vulnerabilities and Exposures (CVEs) before deployment.
This reduces the risk of compromised dependencies entering production systems.
Key DevSecOps best practices include:
Integrating security scanning and testing into CI/CD pipelines
Automating vulnerability detection and compliance checks
Conducting threat modeling during application development
Securing Kubernetes clusters and cloud native workloads
Promoting a DevSecOps culture of shared security responsibility
Common DevSecOps tools include:
Static, dynamic, and interactive application security testing tools (SAST, DAST, IAST)
Container image and Kubernetes security scanners
Software composition analysis (SCA) tools for open source software
Configuration management and policy enforcement tools
Runtime monitoring and vulnerability management platforms
Organizations measure DevSecOps success using metrics such as:
Mean time to remediate (MTTR) vulnerabilities
Frequency and severity of security incidents
Percentage of builds passing automated security checks
Compliance adherence rates
Reduction in high-risk supply chain dependencies
Why customers choose Akamai
Akamai is the cybersecurity and cloud computing company that powers and protects business online. Our market-leading security solutions, superior threat intelligence, and global operations team provide defense in depth to safeguard enterprise data and applications everywhere. Akamai’s full-stack cloud computing solutions deliver performance and affordability on the world’s most distributed platform. Global enterprises trust Akamai to provide the industry-leading reliability, scale, and expertise they need to grow their business with confidence.